The upcoming Forza Horizon 6 introduces a transformative musical experience, blending exclusive collaborations from BABYMETAL and Linkin Park with nine custom radio stations that simulate real-world broadcasts....








The developers behind *Crimson Desert* have drawn a firm line in the sand: while the game’s systems reward calculat...

Two upcoming releases—Styx: Blades of Greed* and Star Trek: Voyager – Across the Unknown*—have officially added sup...

Microsoft’s subscription service is expanding with Kingdom Come: Deliverance II* and The Witcher 3: Wild Hunt Compl...

A new login manager, HDR fixes for Proton gamers, and accessibility breakthroughs define this release—but there’s a...
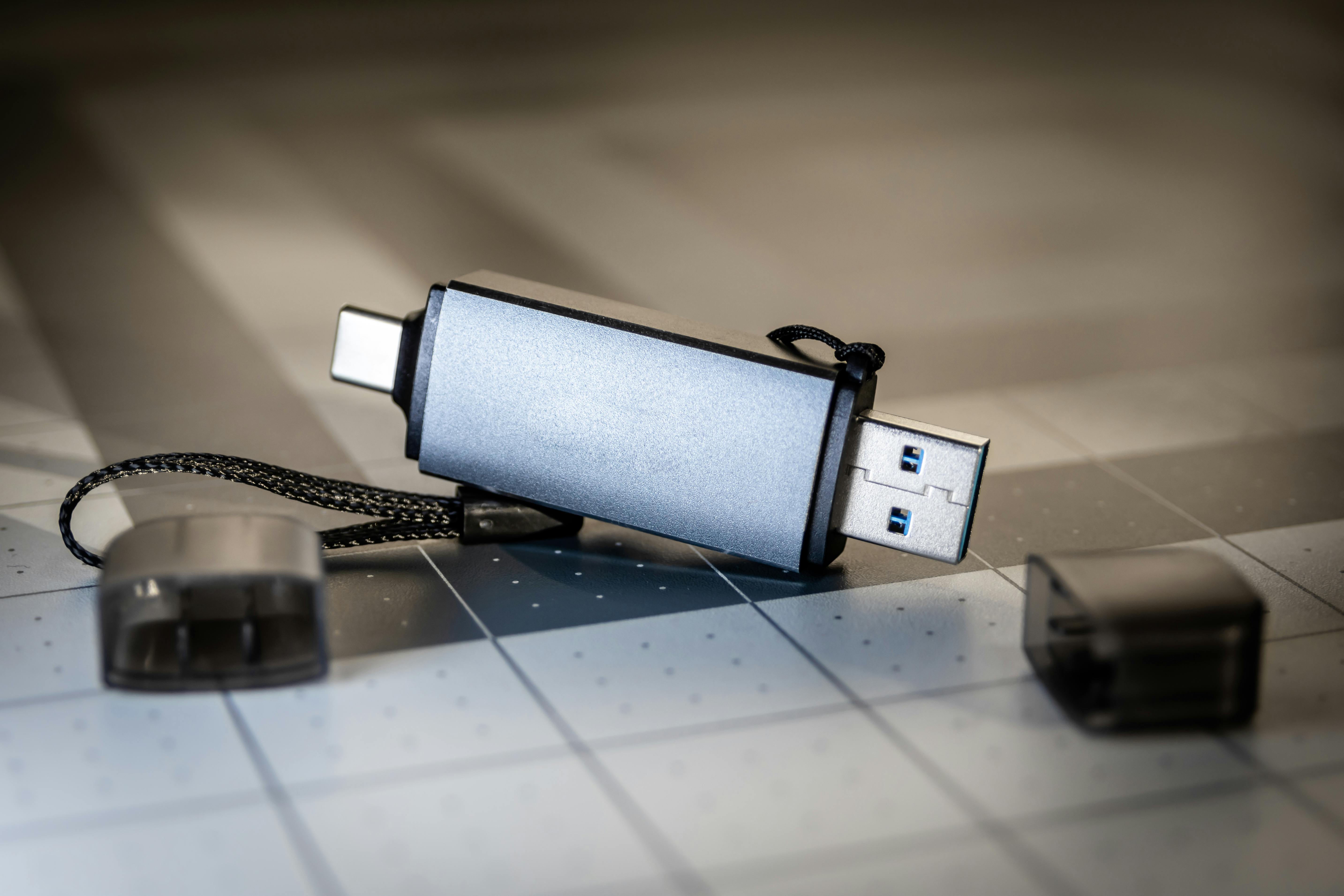
A corrupted USB drive doesn’t always mean permanent data loss. Before hitting 'format,' try these three troubleshoo...

The removal of X’s third theme option—dim mode—has sparked confusion and frustration. A blunt internal admission su...
The new version consolidates vector search, graph traversal, and relational data into one transactional engine, cut...

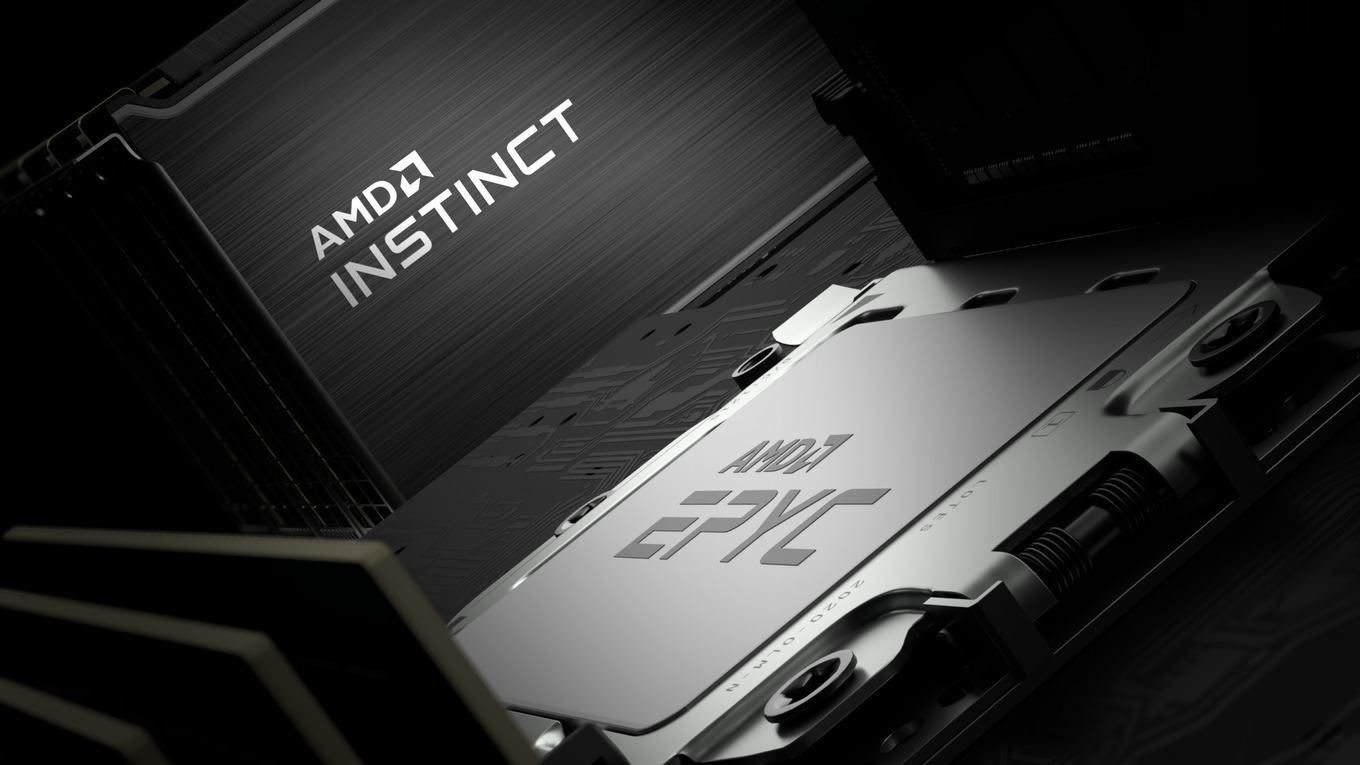
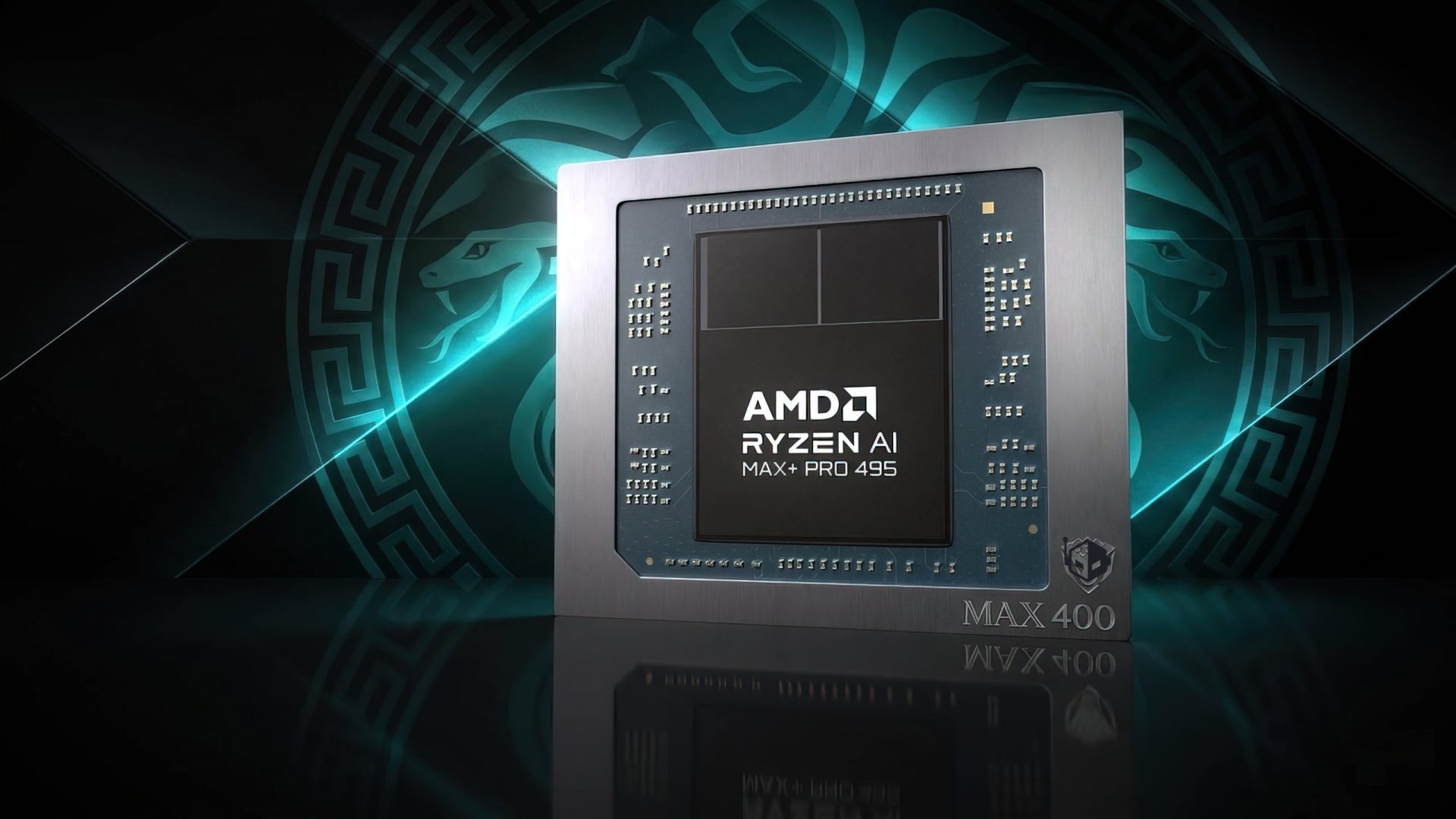
Meta and NVIDIA are collaborating on a multiyear, multigenerational partnership to deploy millions of NVIDIA GPUs,...

A multiyear collaboration will see Meta deploy millions of Blackwell and Rubin GPUs, Arm-based Grace CPUs, and Spec...
A new intelligent Rules System from Qodo aims to eliminate the persistent memory gap in AI-powered code review tool...