Nintendo's upcoming console generation faces both excitement and uncertainty, with potential blockbuster titles on the horizon. While development is underway, industry analysts question whether the company can...







A critical flaw in new ransomware renders encrypted files unrecoverable—not even by attackers—raising fresh concern...

The company’s shift toward high-margin AI chips is delaying the RTX 50 Super and pushing next-gen GPUs into 2028, w...

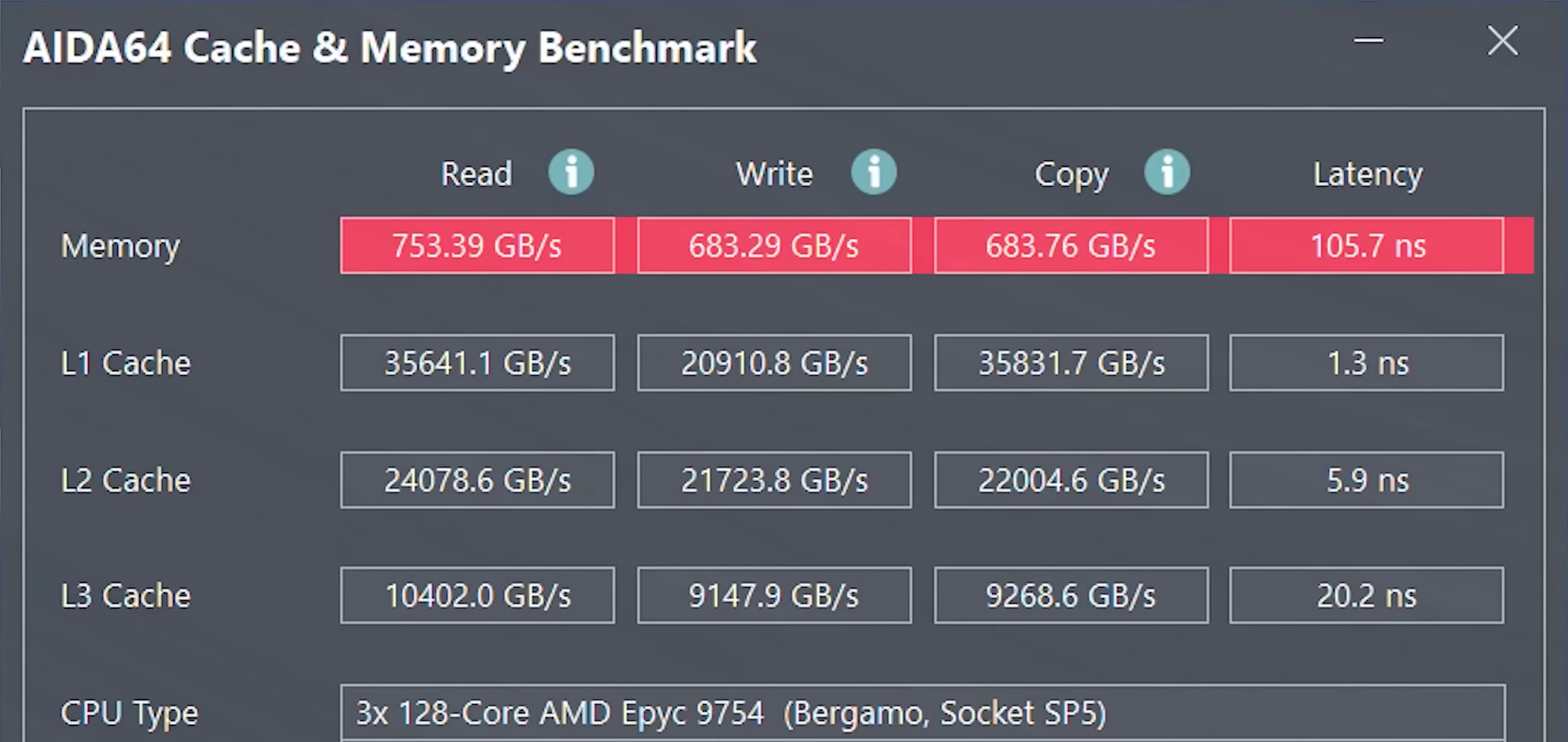
Both Intel and AMD have warned Chinese customers of prolonged delays for server CPUs, with Intel imposing up to six...

A steep $600 discount brings Lenovo’s high-end Legion 5 gaming laptop within reach, but does it still hold up again...
A native Linux app for GeForce NOW is now in beta, but Ubuntu 24.04 exclusivity and missing features like HDR and V...

The game’s voluntary reset mechanic now locks new content behind outdated quest progress, creating a frustrating ca...

Beyond their aesthetic appeal, Nioh 3’s emotes serve a tactical purpose—disarming two types of yokai without combat...

A surge in Nintendo Switch 2 sales in Japan, fueled by blockbuster titles like Pokémon Legends Z-A* and Kirby Air R...

Chris Avellone, the architect behind classics like Fallout: New Vegas* and Planescape: Torment, has publicly distan...
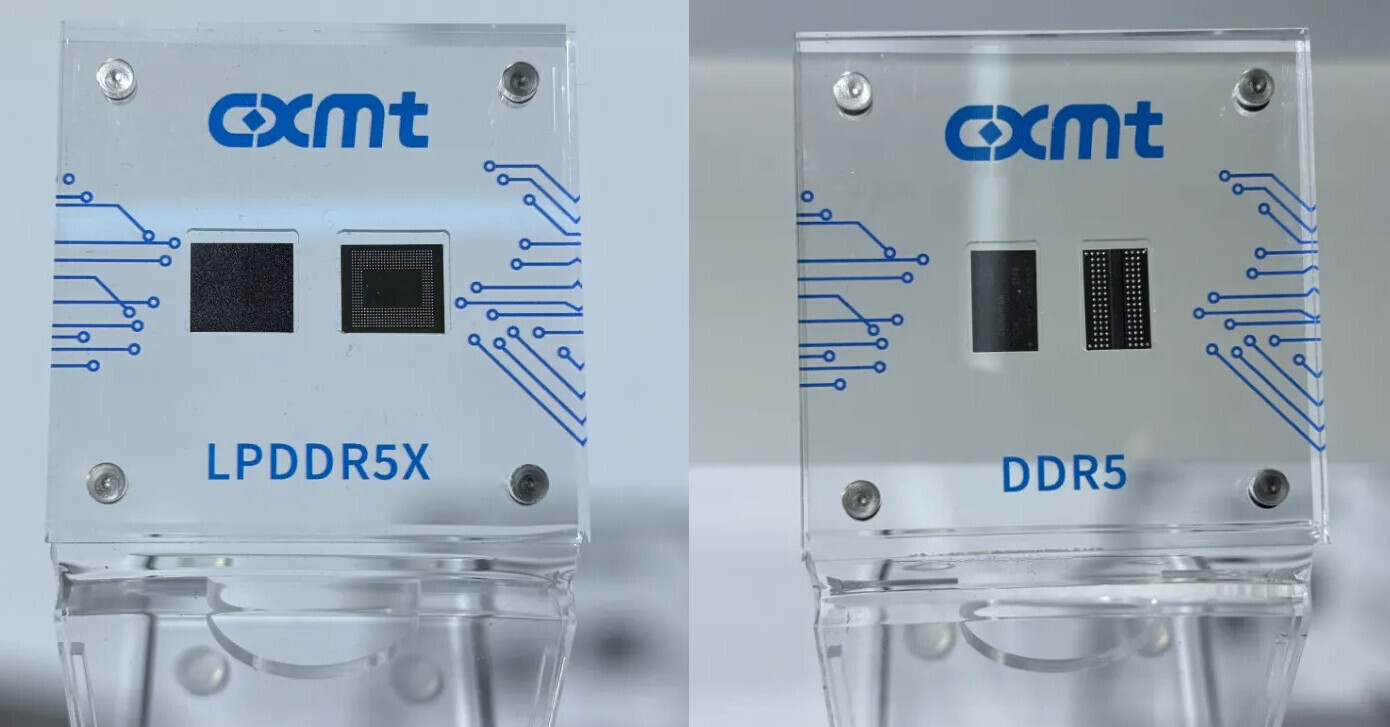
Major brands like ASUS, Acer, Dell, and HP are quietly evaluating memory chips from Chinese manufacturer CXMT as tr...