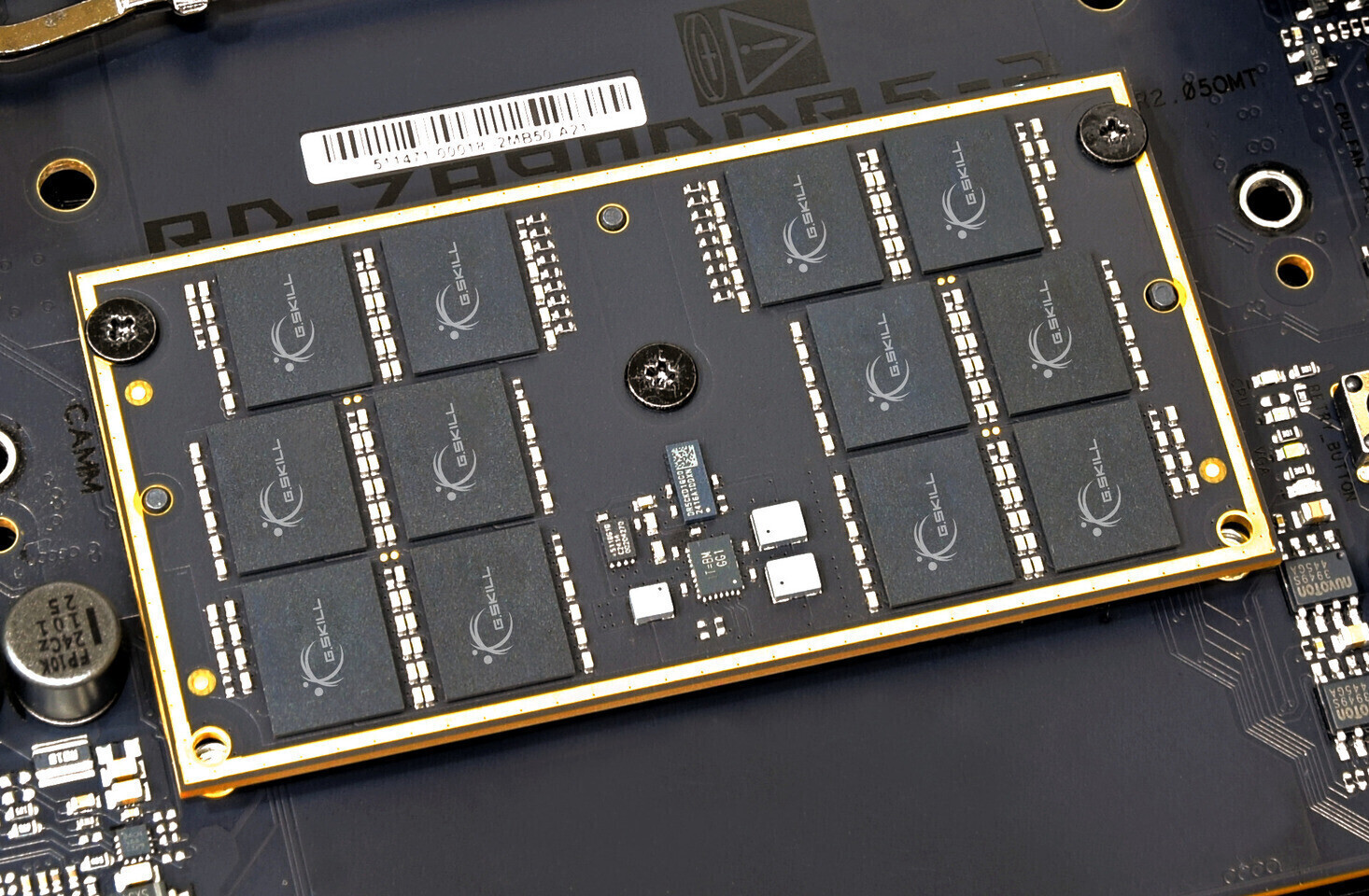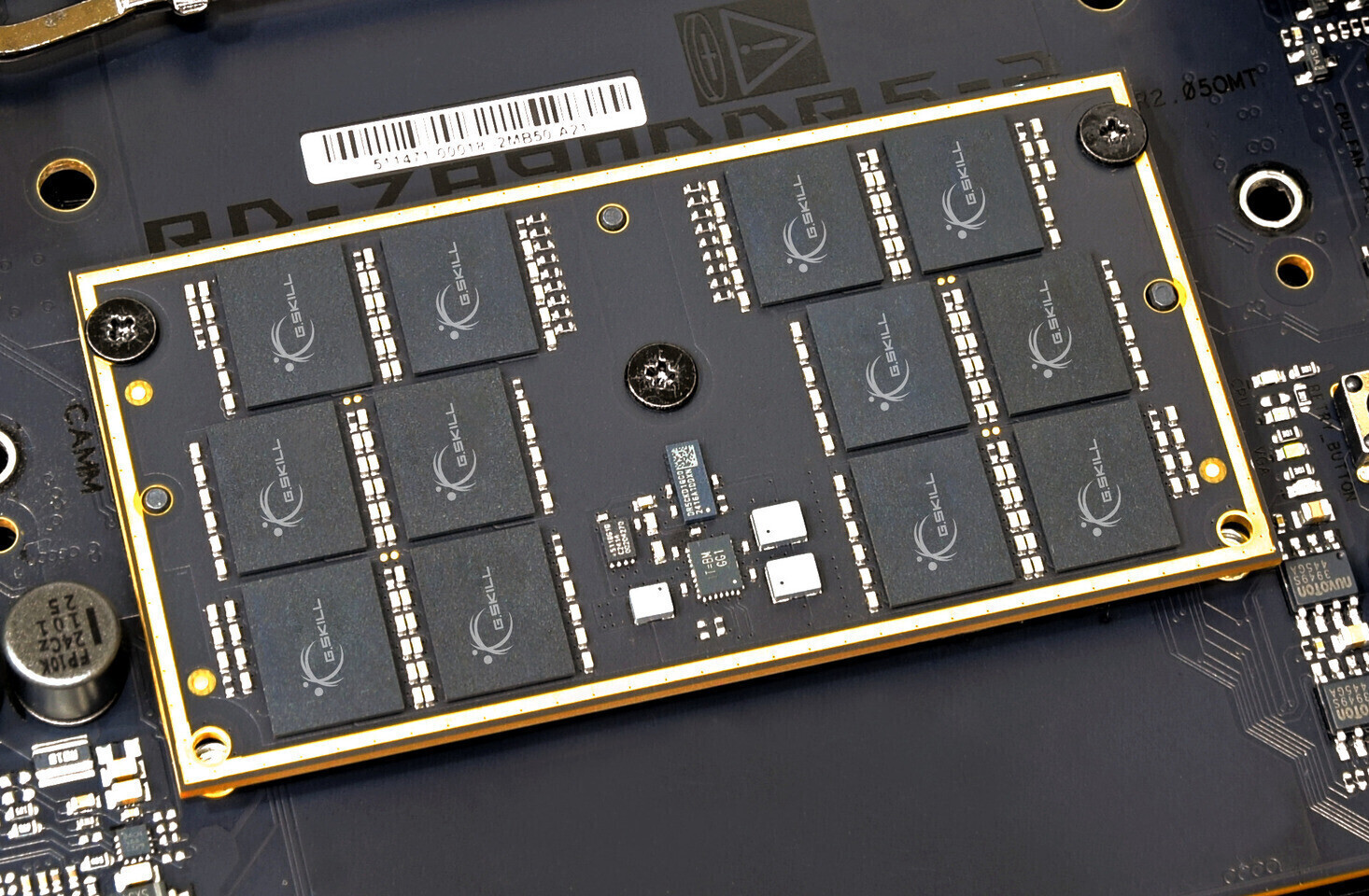
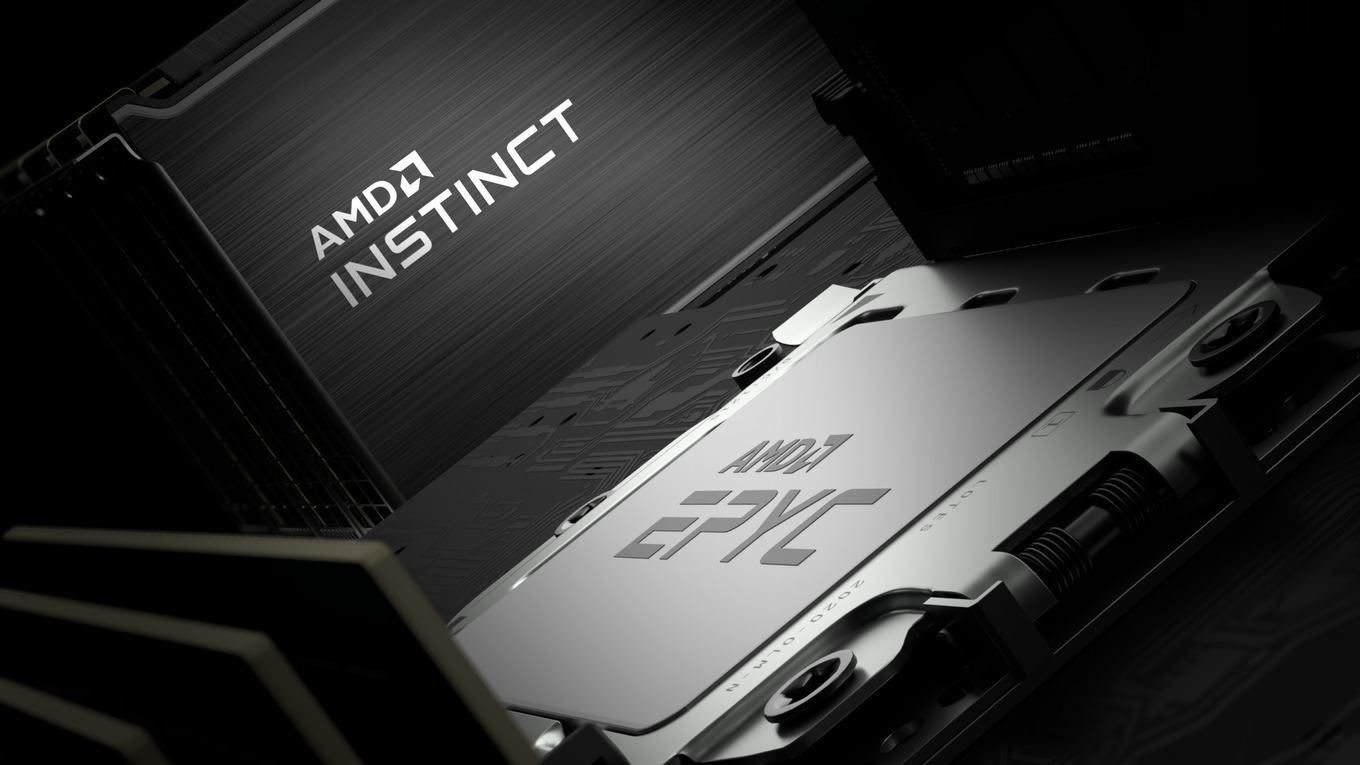
The DDR6 standard is poised to redefine performance benchmarks with speeds up to 17,600 MT/s, but its adoption hinges on overcoming significant engineering challenges. This article explores the tradeoffs behind...









The Pathfinder gaming mouse introduces a modular switch system, custom MCU, and magnesium wheel, addressing longevi...

The Steam Controller arrives next week, promising a new approach to game input that could reshape how players inter...

Valve's Steam Controller launches globally on May 4, priced at $99 in the U.S. This versatile gamepad supports PCs,...

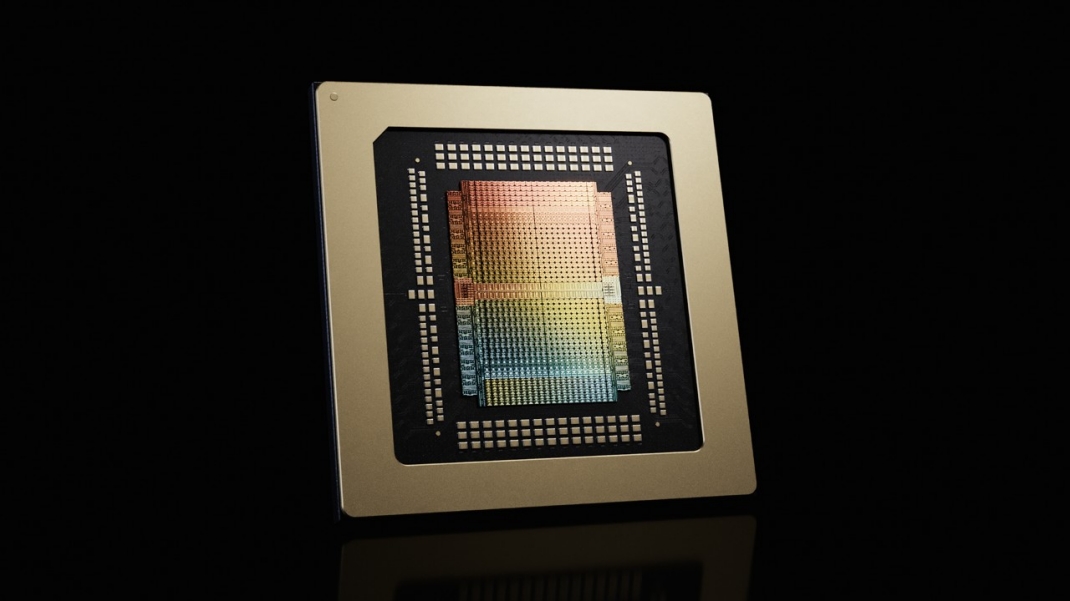
As CPU demand surges, Intel is repurposing edge dies from its silicon wafers—previously discarded due to yield issu...

The upcoming ARC Raiders update is set to transform the game's ecosystem, introducing advanced platform support, a...

The MSI Vector 16 HX AI, equipped with an RTX 5070 Ti GPU, offers powerful performance for small businesses looking...

Two solar-powered security cameras from Aosu deliver 2K resolution at $170, eliminating electricity costs while off...
OpenAI's GPT-5.5 introduces significant performance improvements and efficiency gains, positioning itself as a more...
Reports suggest Ubisoft has reduced the development team for Assassin's Creed Hexe, potentially affecting its 2027...

Kingston has introduced a 30.72 TB Gen 5.0 SSD that delivers 14 GB/s speeds, but adoption hinges on widespread supp...