AMD is seeing an 80% year-over-year increase in server CPU revenue, a sharp rise that highlights how AI is driving major changes in data center hardware. The shift suggests IT teams are moving away from traditi...






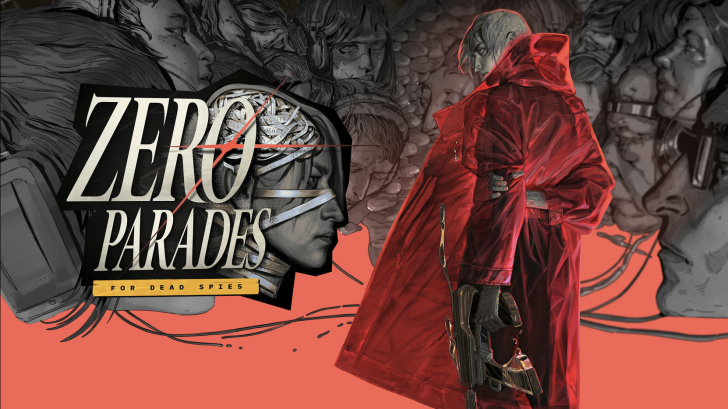
ZA/UM’s follow-up to *Disco Elysium* arrives with a fractured spy narrative, tense 'Dramatic Encounters,' and a pro...

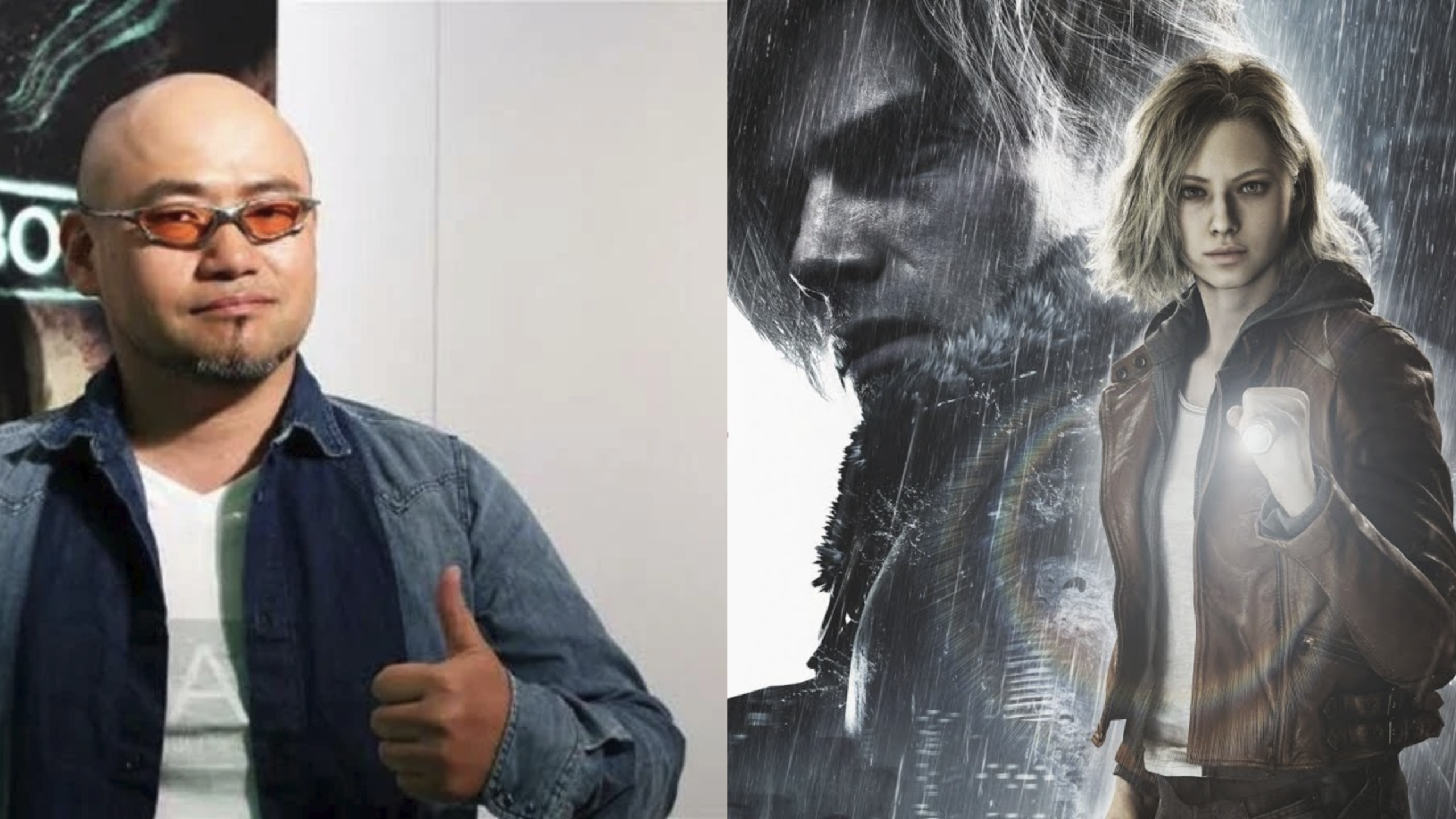
Hideki Kamiya, co-founder of PlatinumGames, has taken an unconventional stance against spoilers for *Resident Evil...
Salt crystals are a rare but vital resource in Disney Dreamlight Valley, unlocking recipes and quests—but only if y...

The G7 Pro 8K PC Aimlabs Edition merges elite hardware with FPS training aesthetics, targeting pro gamers with 8000...

Apple’s next flagship lineup is taking shape with trial production underway for the iPhone 18 Pro and Pro Max, feat...
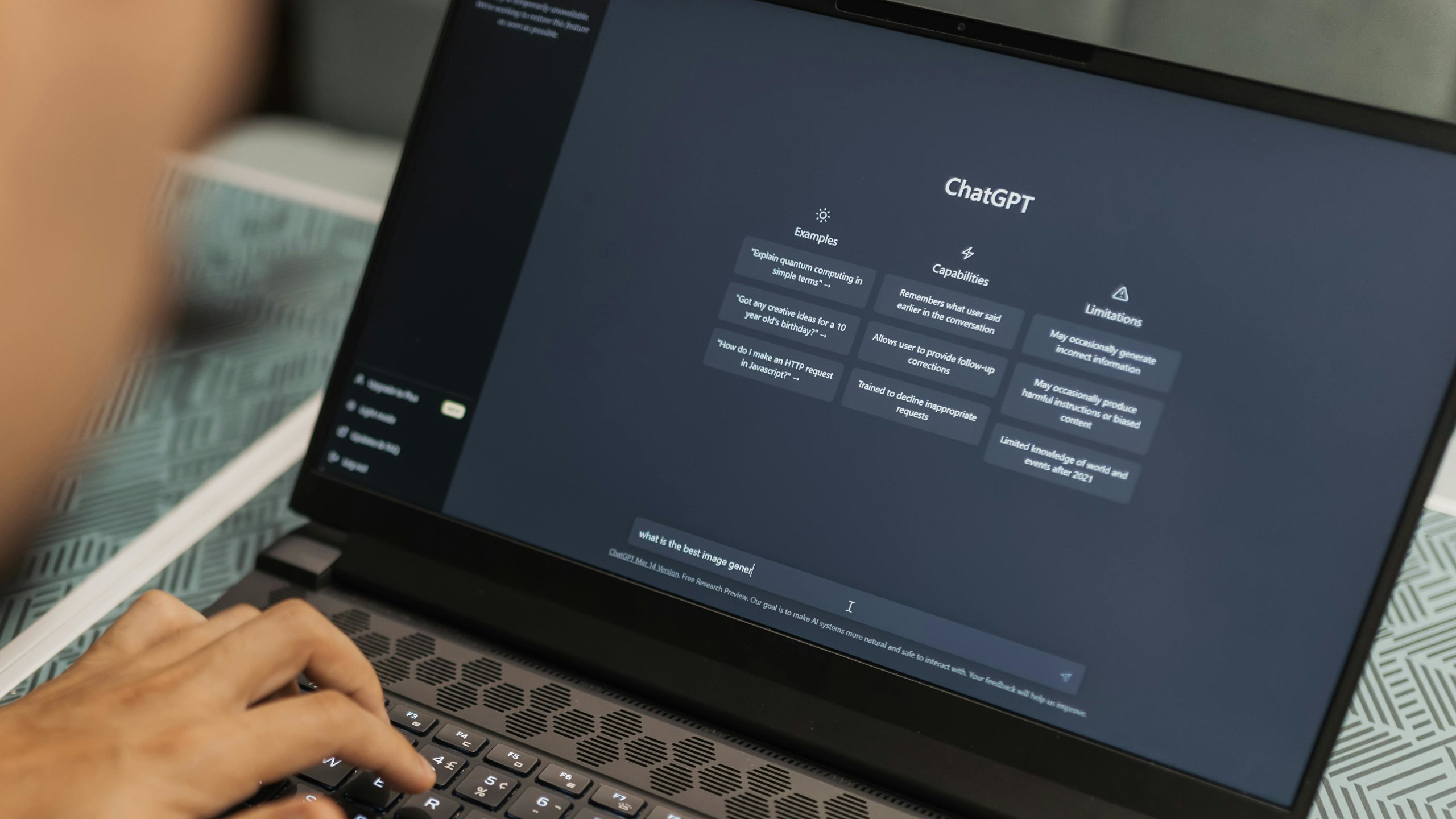
AI tools like ChatGPT, Claude, and Gemini often underperform not because they’re flawed, but because they lack a fu...

The Ugreen Nexode power bank, now priced at $79.97—a 38% discount—delivers laptop-grade charging, three high-speed...

A flagships’ worth of unreleased Galaxy S26 Ultra units have surfaced online, including in Bangladesh’s gray-market...

When inspiration strikes too late—or never arrives—these two browser-based utilities transform passive scrolling in...
Windows-based enterprises are quietly adopting AI agents at scale—but only those optimizing inference costs will se...