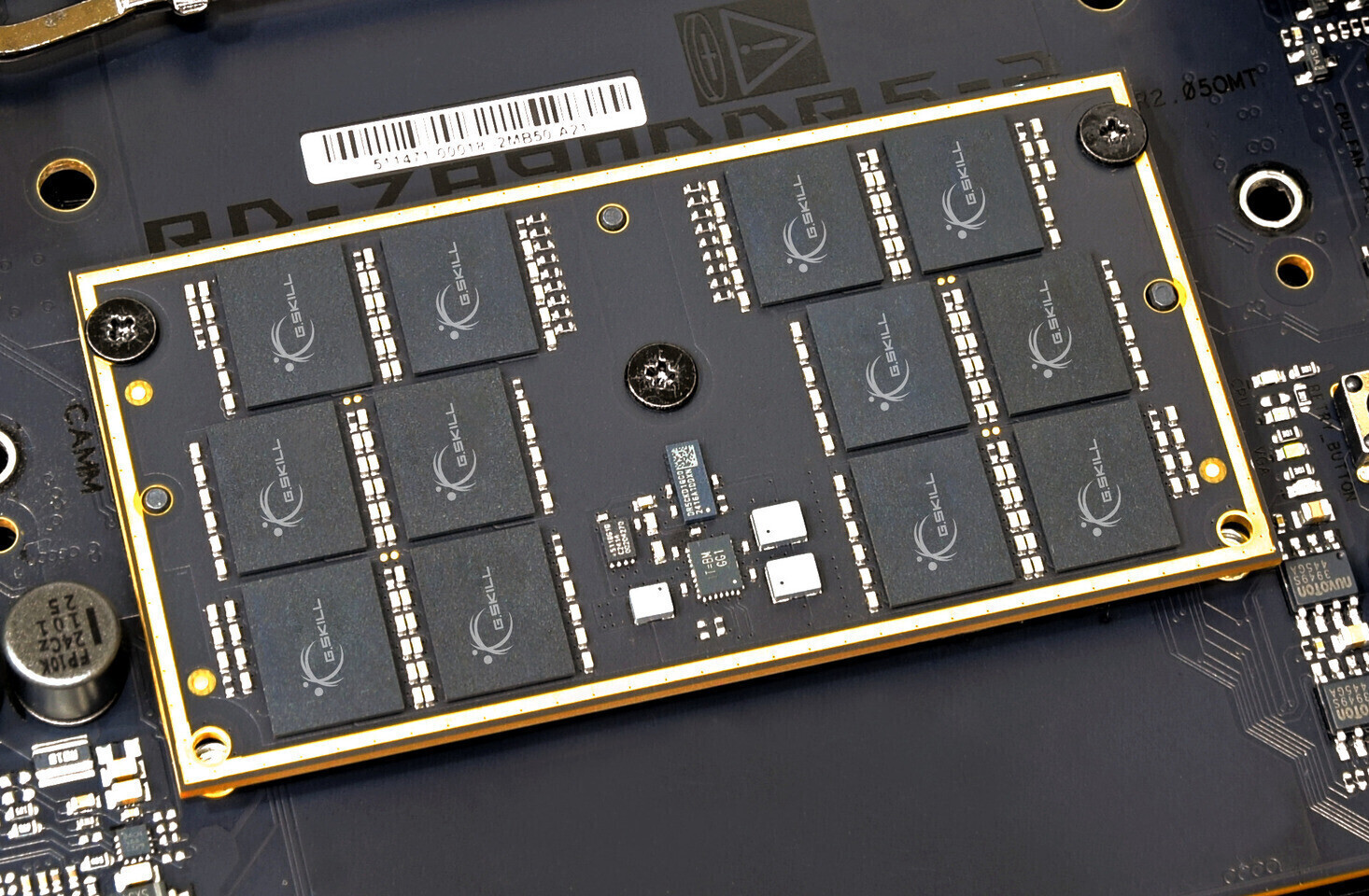
The DDR6 standard is poised to redefine performance benchmarks with speeds up to 17,600 MT/s, but its adoption hinges on overcoming significant engineering challenges. This article explores the tradeoffs behind...










The developer behind Opus Magnum, a celebrated puzzle game, has unexpectedly revived its brand to release a new DLC...
Google’s latest AI architecture eliminates the need for multiple models by dynamically adjusting reasoning power—cu...

The JN-IPS326K-HSPC9 delivers ultra-sharp 6K resolution at 60 Hz, targeting productivity users over high-refresh ga...

A player has uncovered a near-unbreakable warlock build in Diablo 2: Eternal Collection, where summoning a damage-p...
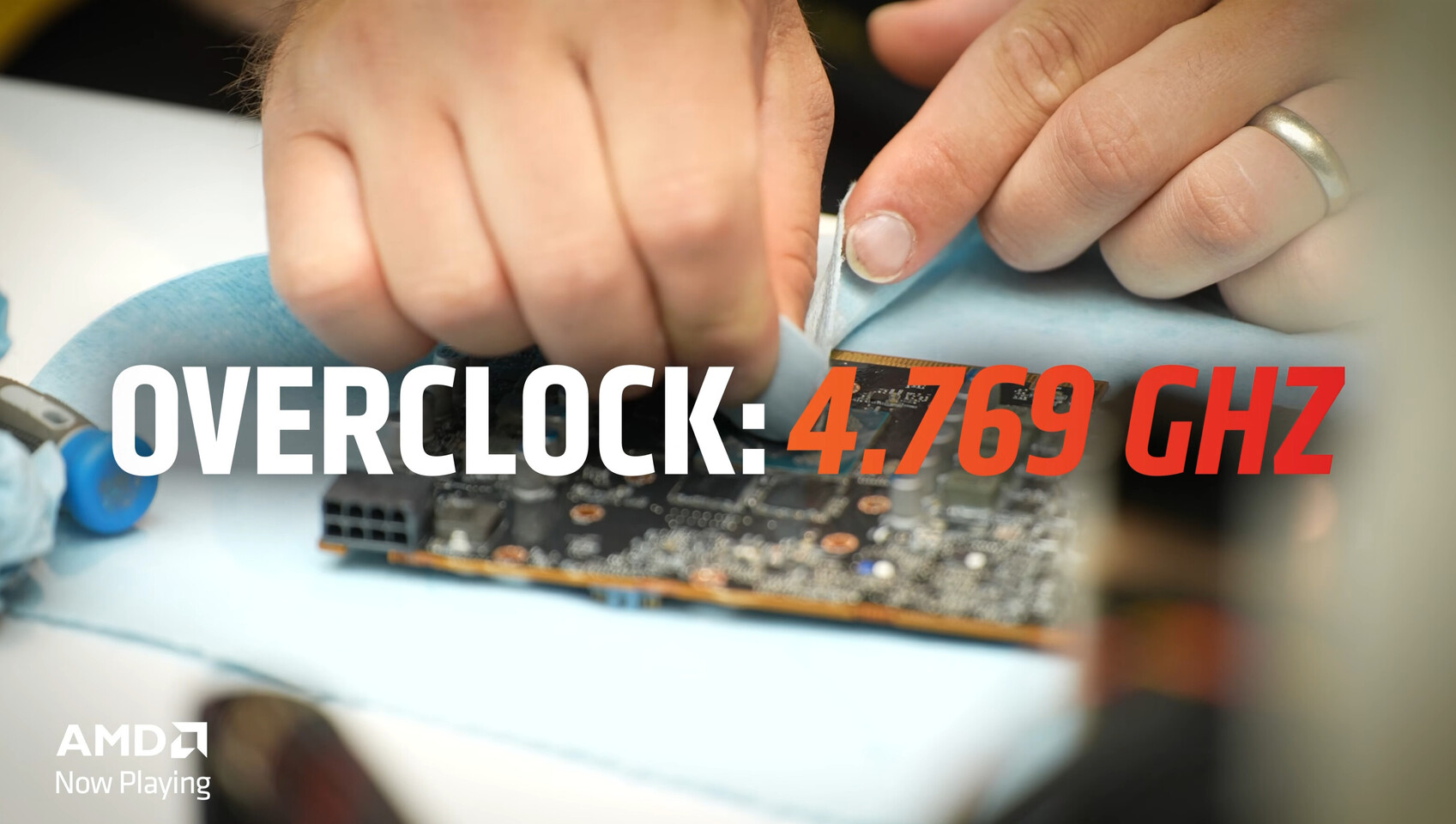
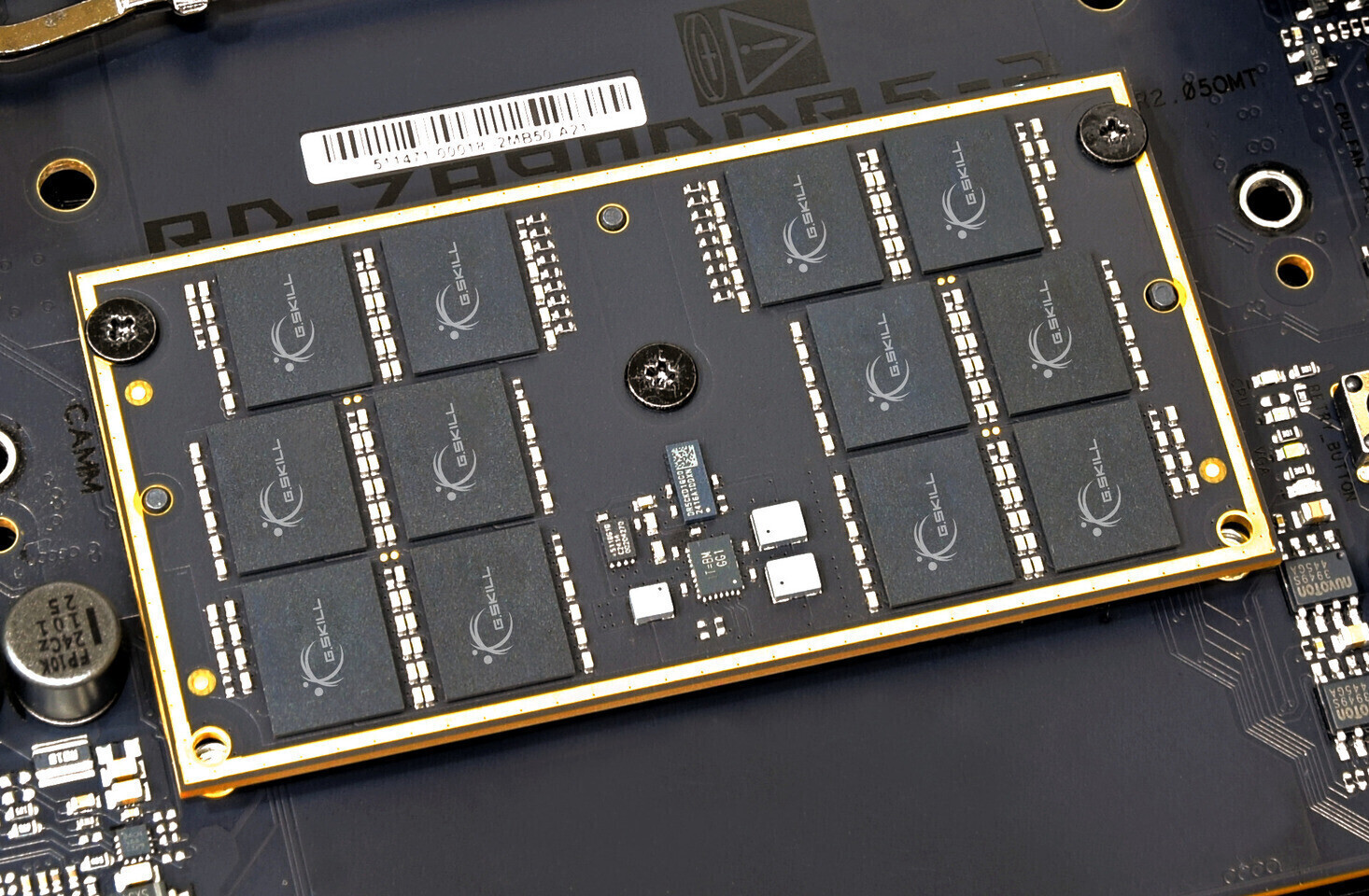
A liquid-nitrogen-cooled RX 9060 XT just hit a new overclocking milestone, pushing RDNA 4 silicon to 4,769 MHz—far...

The creator behind XCOM* and Marvel’s Midnight Suns has closed his studio and shared a rare look at Burbank*, a lif...

The sequel to the beloved roguelike deckbuilder arrives on March 5 with a fully realized co-op mode, letting player...

The French studio behind Life is Strange* and Vampyr has unveiled its latest project—a tense, linear sci-fi adventu...

The latest Battlefield 6 Season 2 roadmap reveals a troubling trend in modern shooters: a relentless, predictable c...

Netflix has acquired global rights to adapt Ticket to Ride—the beloved train-based strategy board game—into scripte...