The surge in AI-driven workloads is putting unprecedented pressure on RAM supplies, with industry experts warning of long-term supply shortages and cost instability. Micron's analysis reveals a growing mismatch...









A strategic price reduction on Ugreen’s 100W USB-C cables eliminates a major cost hurdle, allowing organizations to...

The ASUS Republic of Gamers introduces the ROG Cetra, a pair of open-wireless earbuds designed to redefine in-game...
The RTX 5090 and RTX 4070 cards are set to arrive with distinct pricing strategies. Buyers need to weigh supply con...
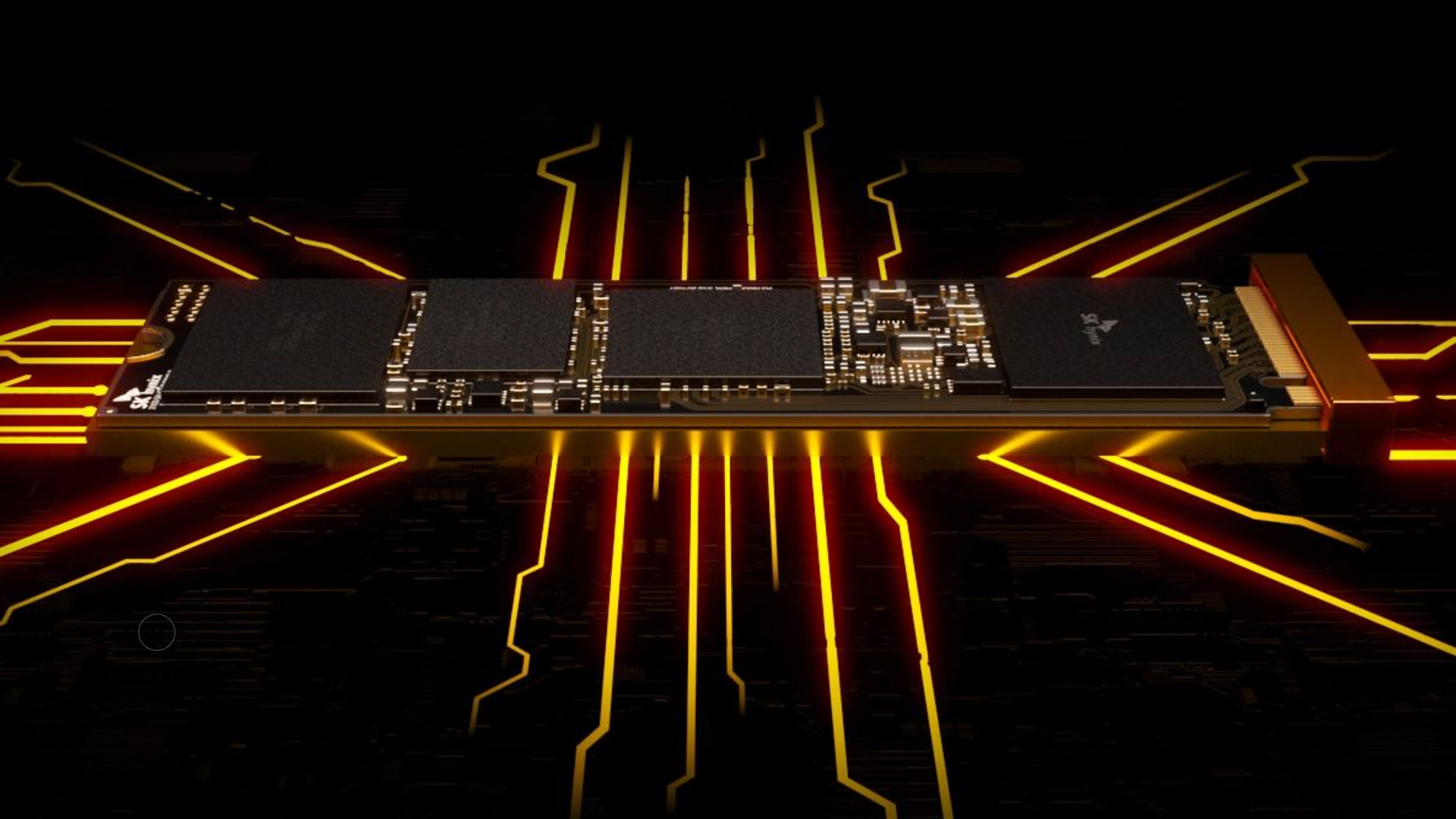
A 16TB M.2 SSD has arrived with performance that defies storage norms, but its real-world impact on gaming and high...

This guide examines the practical challenges IT teams encounter when deploying AMD FSR 4 within Crimson Desert, foc...

A sweeping restructuring at Ubisoft’s Red Storm studio has redefined its role, removing it from active game develop...

The latest flagship phones, iPhone 17 Pro Max and Samsung Galaxy S26 Ultra, have been put to the test in a rigorous...

New performance data highlights the game's demanding AI systems, which could force small businesses to upgrade GPUs...
A new no-code tool allows users to design and publish a functional website in minutes, eliminating the need for cod...

A new unannounced project for The Witcher 3 is set to arrive late this year, but CD Projekt RED has yet to confirm...