

NVIDIA's latest open-source model, Nemotron-3-Super, has surpassed competitors in performance metrics, influencing upgrade decisions for developers and researchers.







The ASUS ROG Ally X delivers impressive mobile performance with an NVIDIA RTX 5060 and 32GB DDR5 RAM, but its premi...

Colorful's latest motherboard launches signal a pivot toward cost-effective DDR5 integration, offering enterprise b...

A new wave of laptops is proving that lightweight, durable designs don’t need to cost a fortune. These models are c...

A revolutionary GPU architecture delivers a 20% performance increase while reducing power consumption by the same a...

Samsung’s withdrawal from the multi-level cell (MLC) NAND market has accelerated consolidation among Taiwanese manu...

The Logitech G512 X keyboard introduces adjustable actuation, making it a compelling option for users who prioritiz...
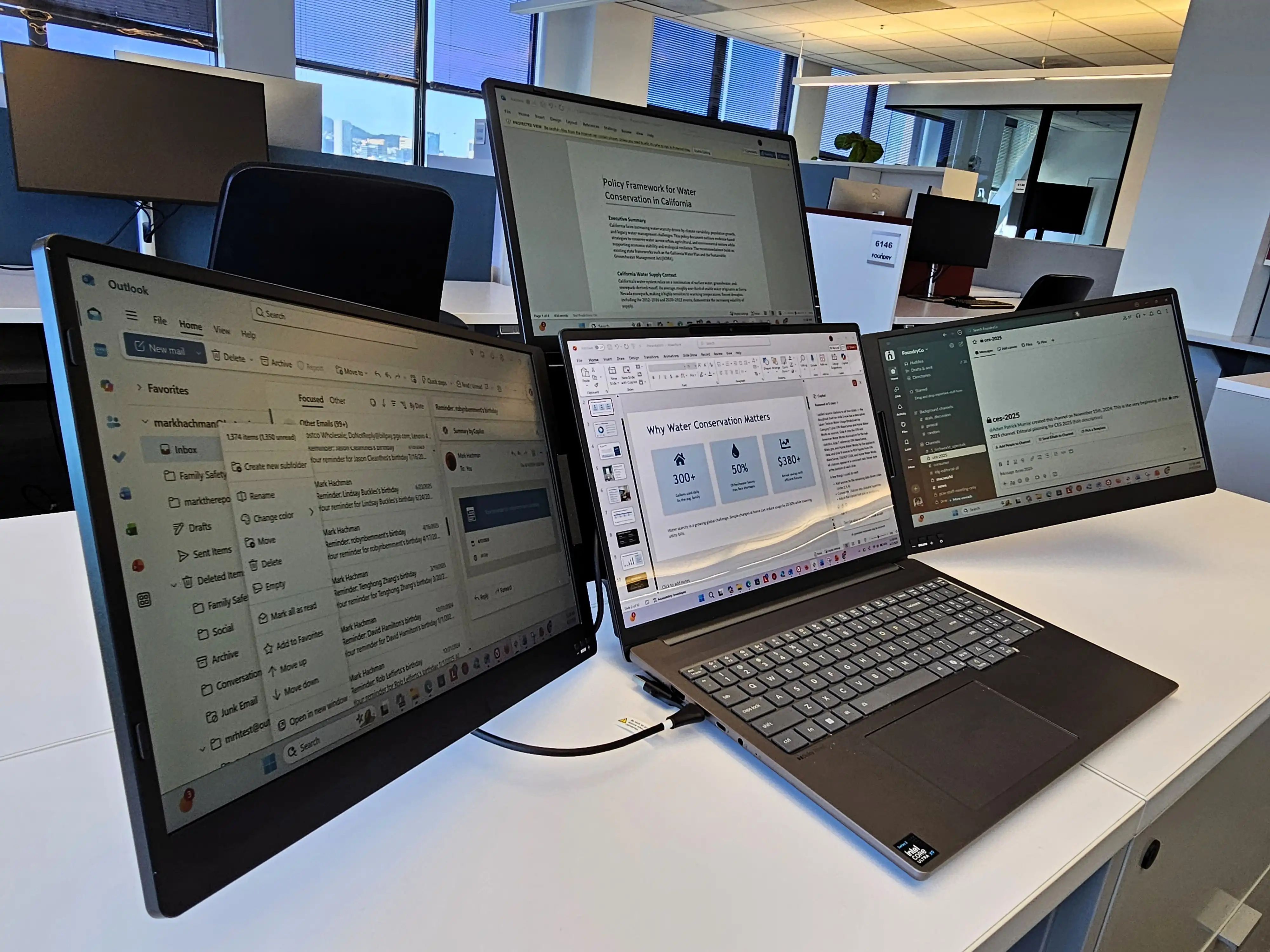
A new triple-screen extender for laptops promises to turn any backpack into a mobile multi-monitor setup—but real-w...
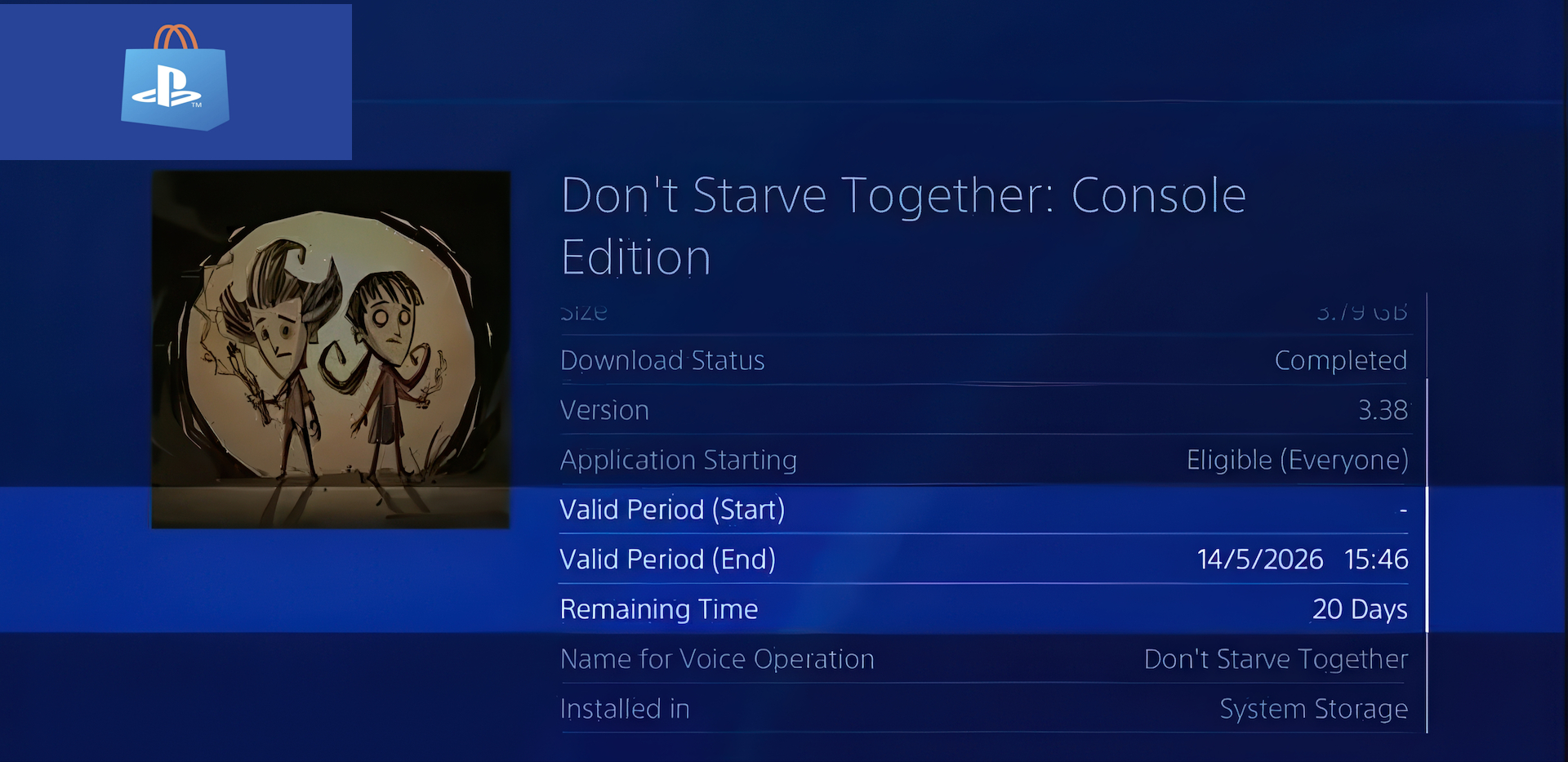
Sony is reintroducing a digital rights management policy on PlayStation that closely mirrors the one it once critic...

The ACEMAGIC F5A Mini PC delivers high-performance computing in a compact form, featuring AMD's Ryzen AI 9 HX 470 p...

The PlayStation 6’s AMD RDNA 5 architecture could push path tracing to 60 FPS, but mandatory handheld support may l...





