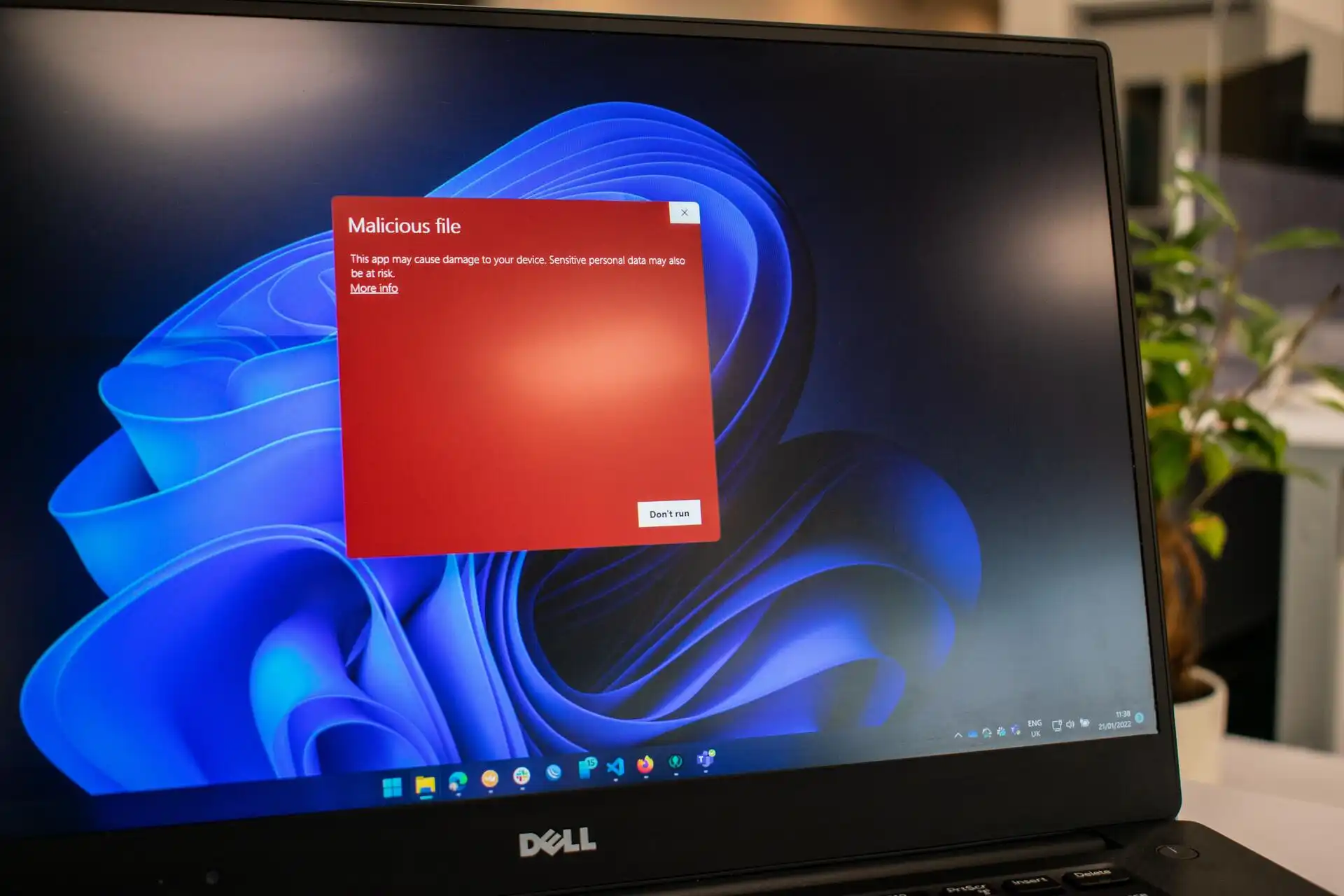
The number 12,345 isn’t just a random figure—it represents the estimated count of malicious domains that can be blocked with a single browser setting. For enterprise IT teams, this translates to immediate cost savings, reduced risk of phishing and malware infections, and minimal operational overhead.
This setting targets third-party cookies from known malicious sites. While third-party cookies are often associated with privacy concerns, their restriction also serves as a critical security measure. By preventing these cookies, browsers limit the ability of malicious actors to track users or serve deceptive content, effectively reducing exposure to phishing attempts and malware.
- Up to 90% of phishing attempts targeting enterprise users can be blocked with this setting.
- No additional software or network-level changes are required; it’s built into modern browsers like Chrome, Firefox, and Edge.
- Cost savings are direct, eliminating the need for specialized security tools.
The impact on operational costs is significant. Traditional security measures often require extensive deployment and maintenance, adding to IT workloads. In contrast, this browser-level tweak requires nearly zero additional effort once enabled. It scales seamlessly across an organization without sacrificing usability or performance.
For enterprises evaluating security enhancements, this setting should be a priority. It aligns with trends toward lightweight, built-in security features that reduce reliance on third-party solutions. While it may not replace comprehensive security protocols, it serves as an effective first line of defense against common threats. Adopting this approach can lead to measurable reductions in malicious activity without disrupting workflows.
Currently, this setting is available in widely used browsers and requires no additional infrastructure. For organizations looking to cut security costs while maintaining robust protection, it offers a low-risk solution with immediate benefits.