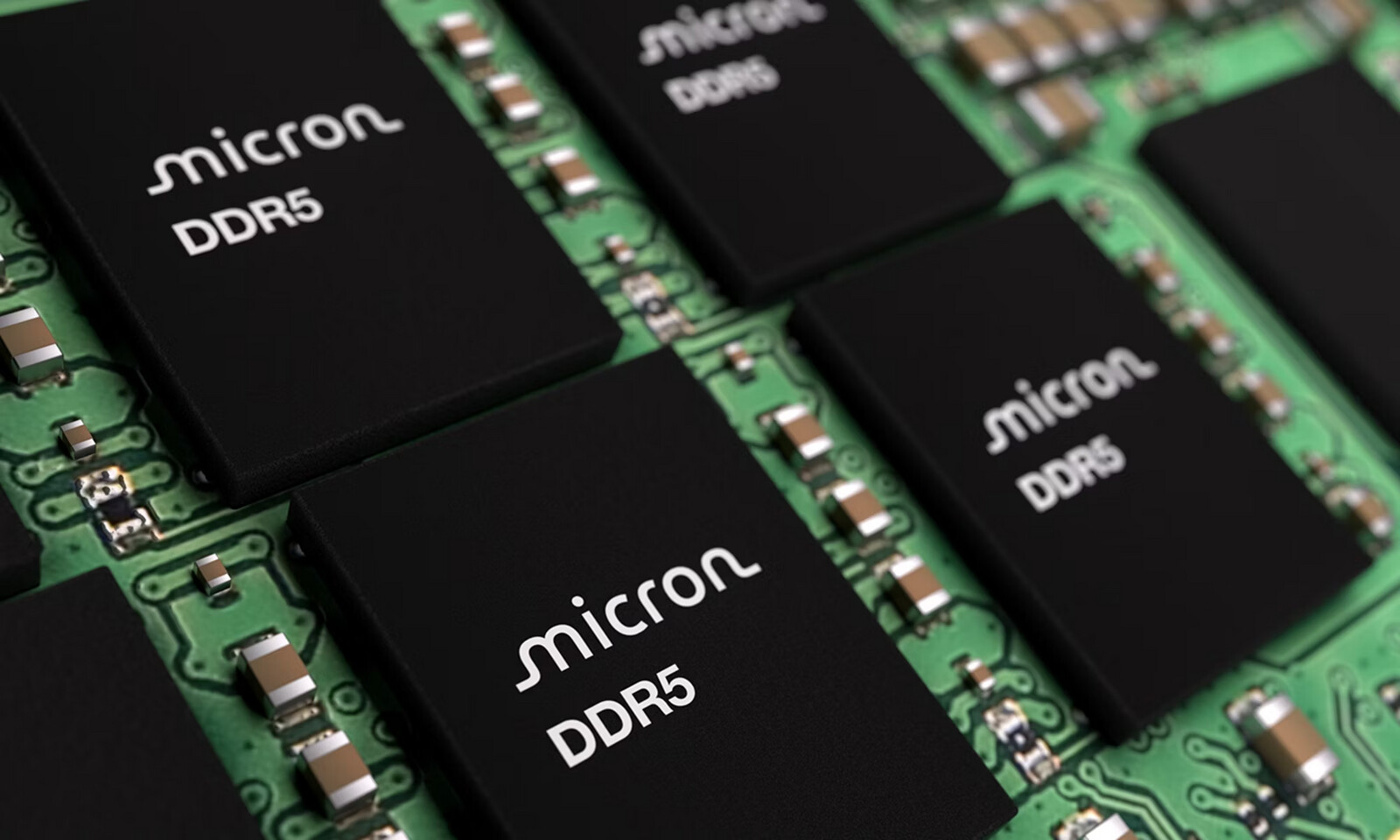
The surge in AI-driven workloads is putting unprecedented pressure on RAM supplies, with industry experts warning of long-term supply shortages and cost instability. Micron's analysis reveals a growing mismatch...









The ASUS ExpertCenter P600 AiO redefines business computing with AMD's Ryzen AI processor, offering a compact yet p...

Anthropic is imposing stricter operational limits on Claude, forcing developers to adapt their approaches. The chan...

NVIDIA's latest AI upscaling technology, DLSS 5, promises significant performance gains but comes with limitations...

Nacon is exploring the sale of its subsidiaries—Spiders Studio, Greedfall, and Steelrising—to stabilize operations...

Enterprise buyers can now preview the Intel Core Ultra 200S Plus desktops, with confirmed pricing starting at $1,89...

The Aqara G410 video doorbell hub delivers stronger performance and gaming-friendly features, but its future value...

A subtle but persistent bug in newer MacBook Pro models is triggering incorrect diagnostic codes, potentially misle...
A new technique from Google could slash the memory needs of AI models by up to six times, but its real-world impact...

The NCT404 quad-port 10G module from Aewin leverages Intel's E610 controllers to deliver power efficiency and exten...

Maingear's integration of Intel's latest Core Ultra 200S Plus processors into its MG-1 desktops reflects a calculat...