The surge in AI-driven workloads is putting unprecedented pressure on RAM supplies, with industry experts warning of long-term supply shortages and cost instability. Micron's analysis reveals a growing mismatch...









The HP Envy 16 laptop, now available at a 45% discount, combines strong performance with portability, making it an...

Intel’s latest CPU, the Nova Lake-AX, is poised to enter the market with a desktop-class socket, potentially reshap...

The AMD Instinct MI355X accelerator stands out in MLPerf benchmarks with over 1 million tokens per second, offering...

Dell Technologies has expanded its PowerProtect portfolio to enhance data protection and cyber resilience, introduc...

Chinese memory manufacturers are destroying stockpiled DDR5 modules, signaling a major shift in gaming hardware. Th...

A former Nintendo supply chain executive warns that helium shortages and rising oil prices could significantly incr...

Developers face a critical dilemma as AI workloads demand more computational power, leading to increased heat outpu...
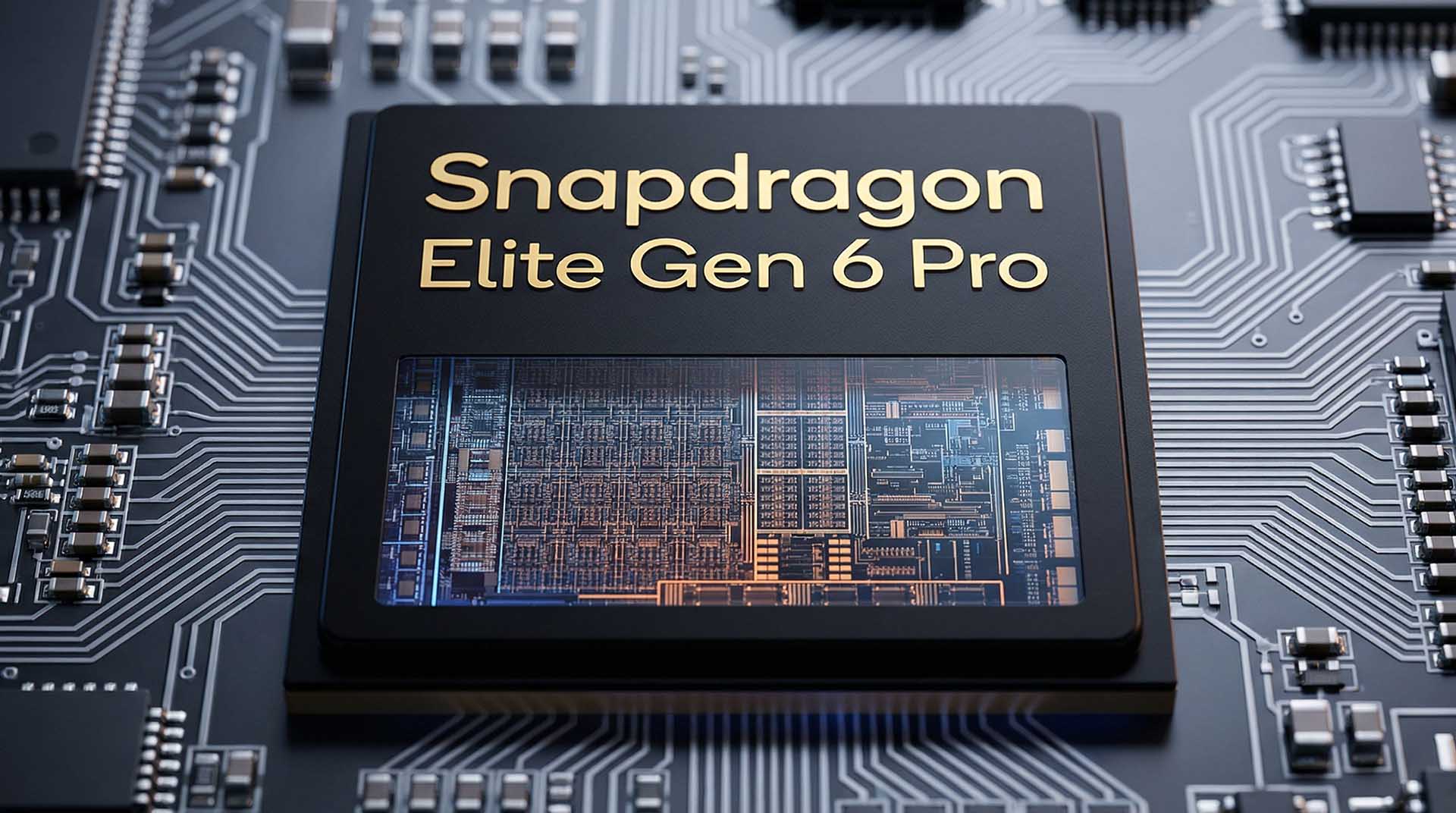
The Snapdragon 8 Elite Gen 6 Pro sets a new benchmark for mobile processors with its record-breaking shared L2 cach...

The new Gigabyte motherboard redefines aesthetics and performance, blending dark wood texture with advanced thermal...

A new generation of handheld gaming is on the horizon, but the Steam Deck 2’s ambitious roadmap faces a growing bot...