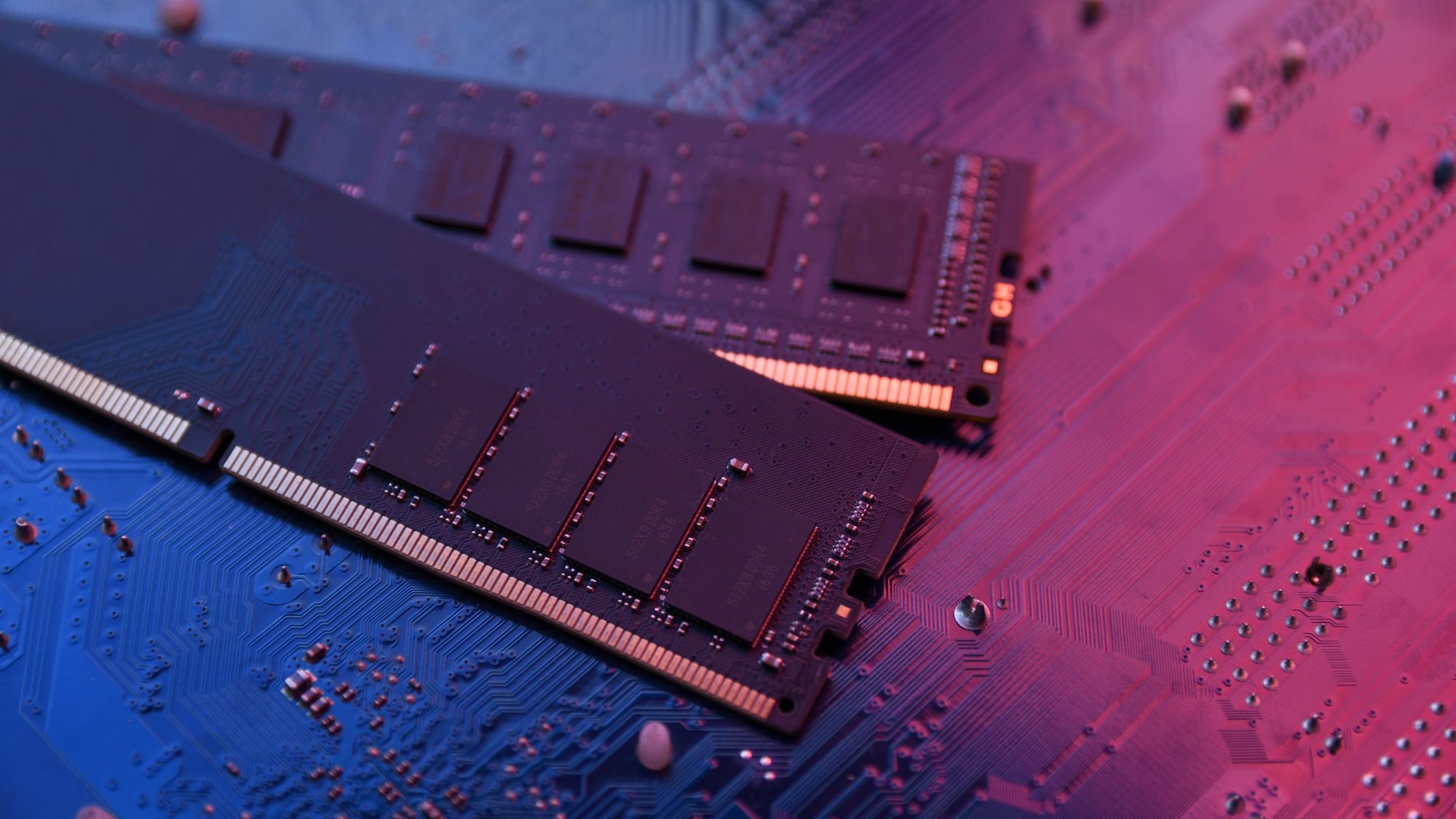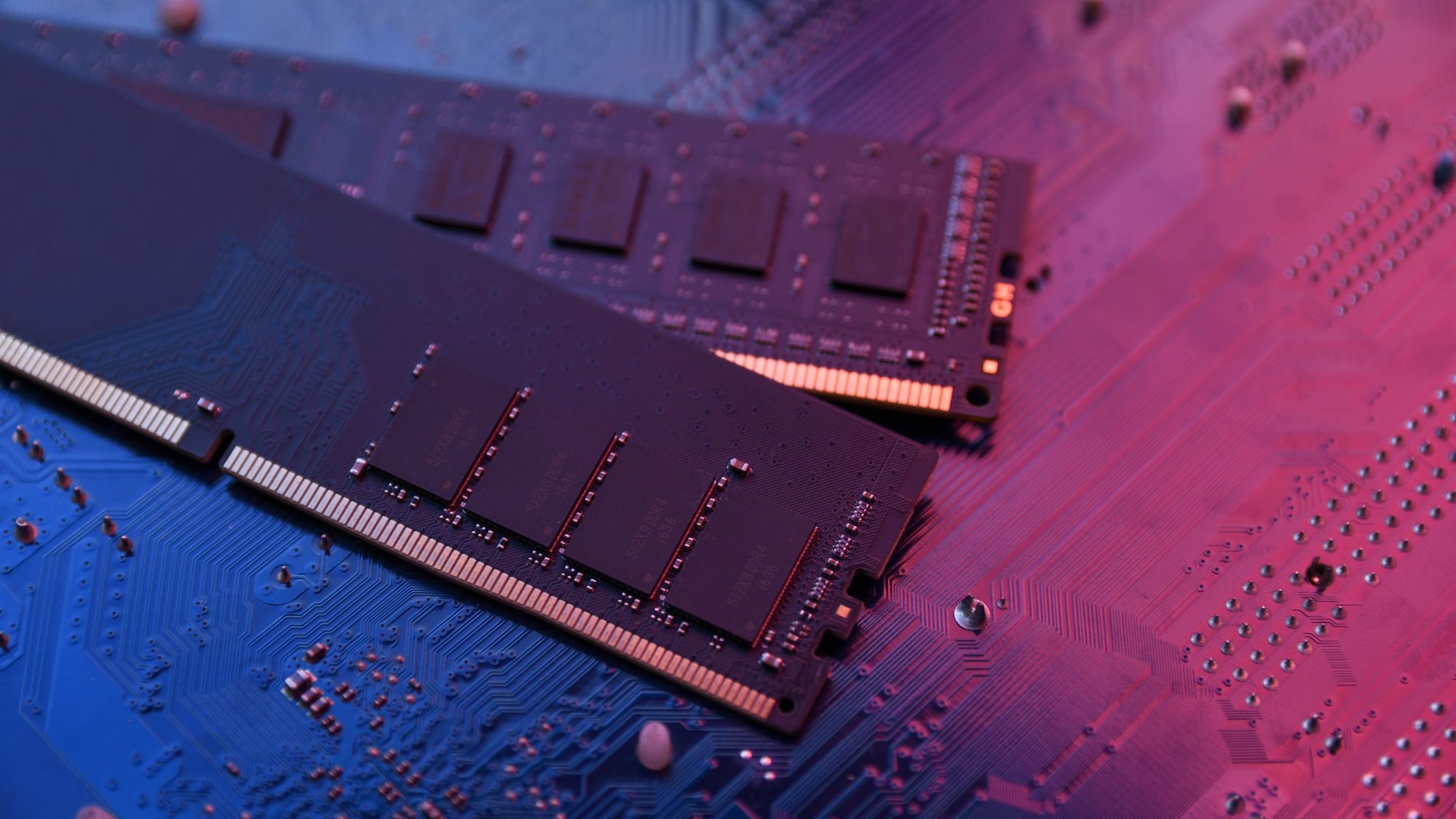
The surge in AI-driven workloads is putting unprecedented pressure on RAM supplies, with industry experts warning of long-term supply shortages and cost instability. Micron's analysis reveals a growing mismatch...









The Crimson Desert sequel is moving into development with a strong focus on single-player gameplay, potentially sid...

The Acer Chromebook Spin 714 offers a high-end design and performance for less than $100, making it a standout in t...

The latest update introduces player crafting for weapons and armor, along with a multi-stage co-op mission that tas...

A major software retailer is slashing prices on genuine Windows and Office licenses, offering lifetime upgrades for...

A potential price adjustment across Sony's PlayStation hardware could reshape the console ecosystem, tightening mem...

A new game in the V Rising universe promises deeper mechanics, greater danger, and a shift beyond traditional survi...
The RTX 50 series, including the RTX 5060 and RTX 5090, is facing production challenges as AI demand reshapes GPU s...

Apple has unveiled the Mac Studio, a high-performance desktop designed to replace the discontinued Mac Pro tower. T...

The M.A.P.P. mouse, a relic from 2002 with roots in Ghost in the Shell lore, is back as a limited-edition model, bl...

Four WOLFBOX portable air blowers are now discounted up to 40 percent on Amazon, including the MF200 which offers a...