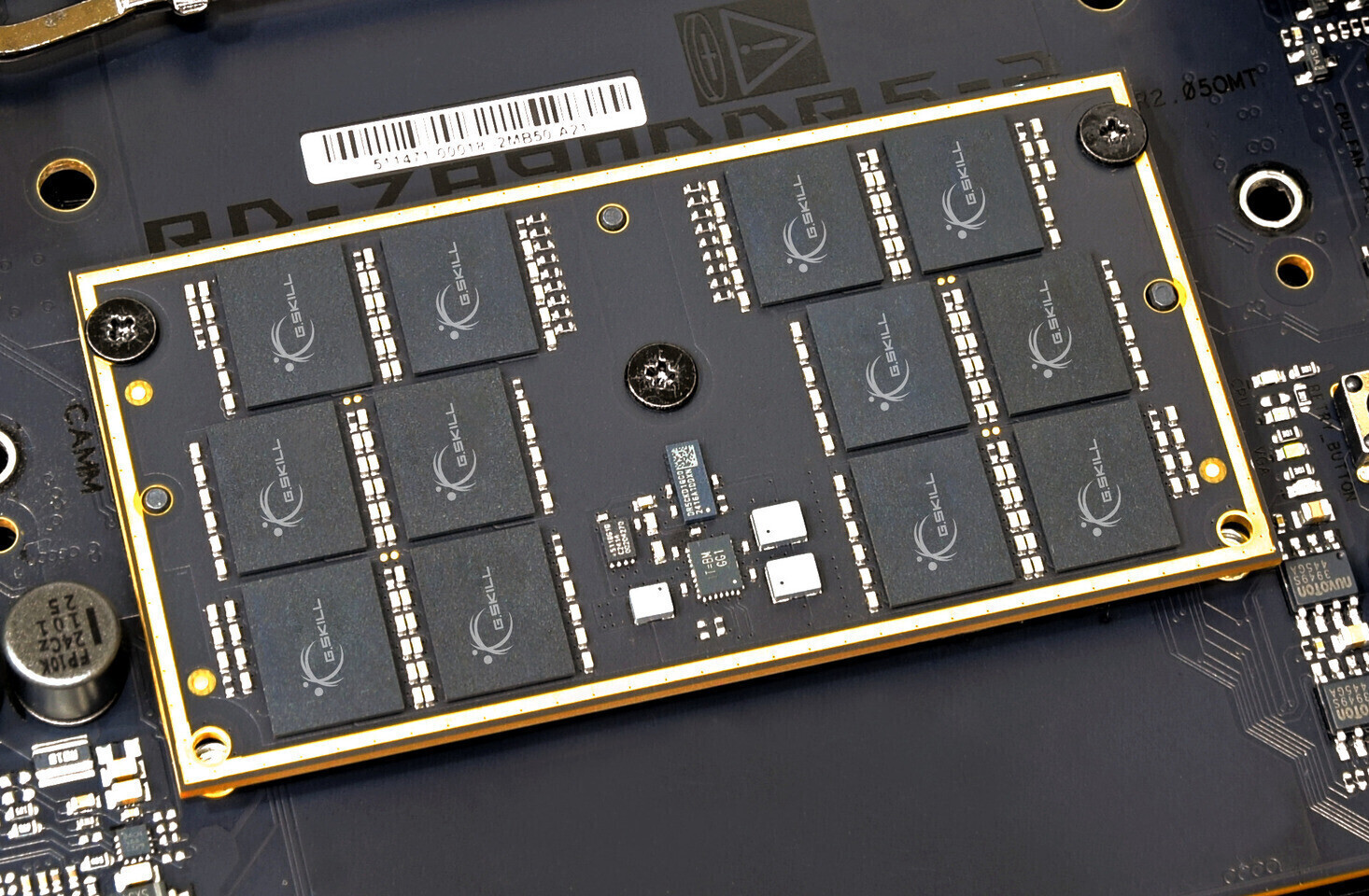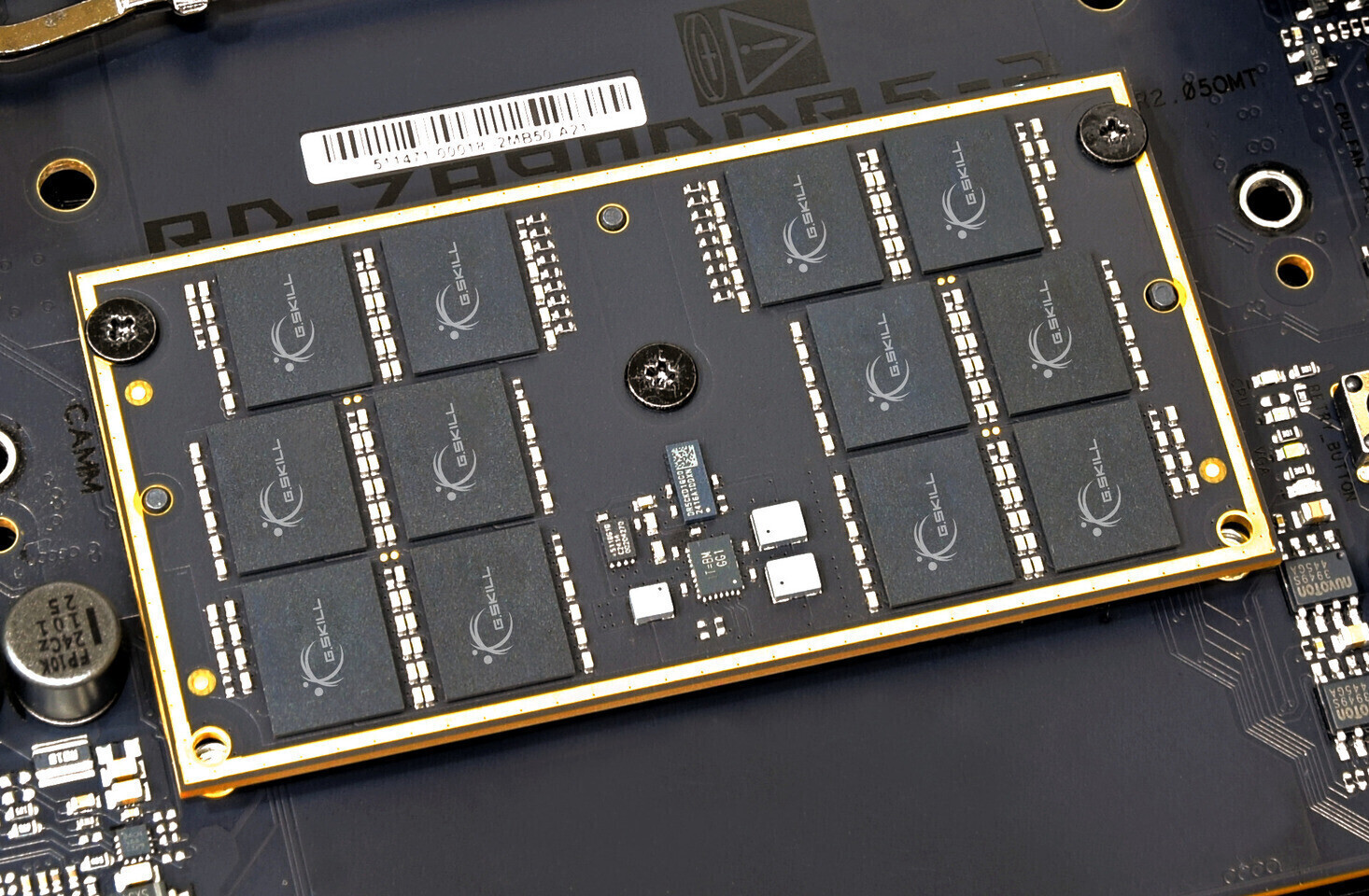
The DDR6 standard is poised to redefine performance benchmarks with speeds up to 17,600 MT/s, but its adoption hinges on overcoming significant engineering challenges. This article explores the tradeoffs behind...









A Munich court’s injunction halts direct purchases of Acer and Asus gaming PCs in Germany, while retailers remain u...

Samsung’s advanced pixel-level privacy display, debuting on the Galaxy S26 Ultra, is poised to arrive in future Mac...

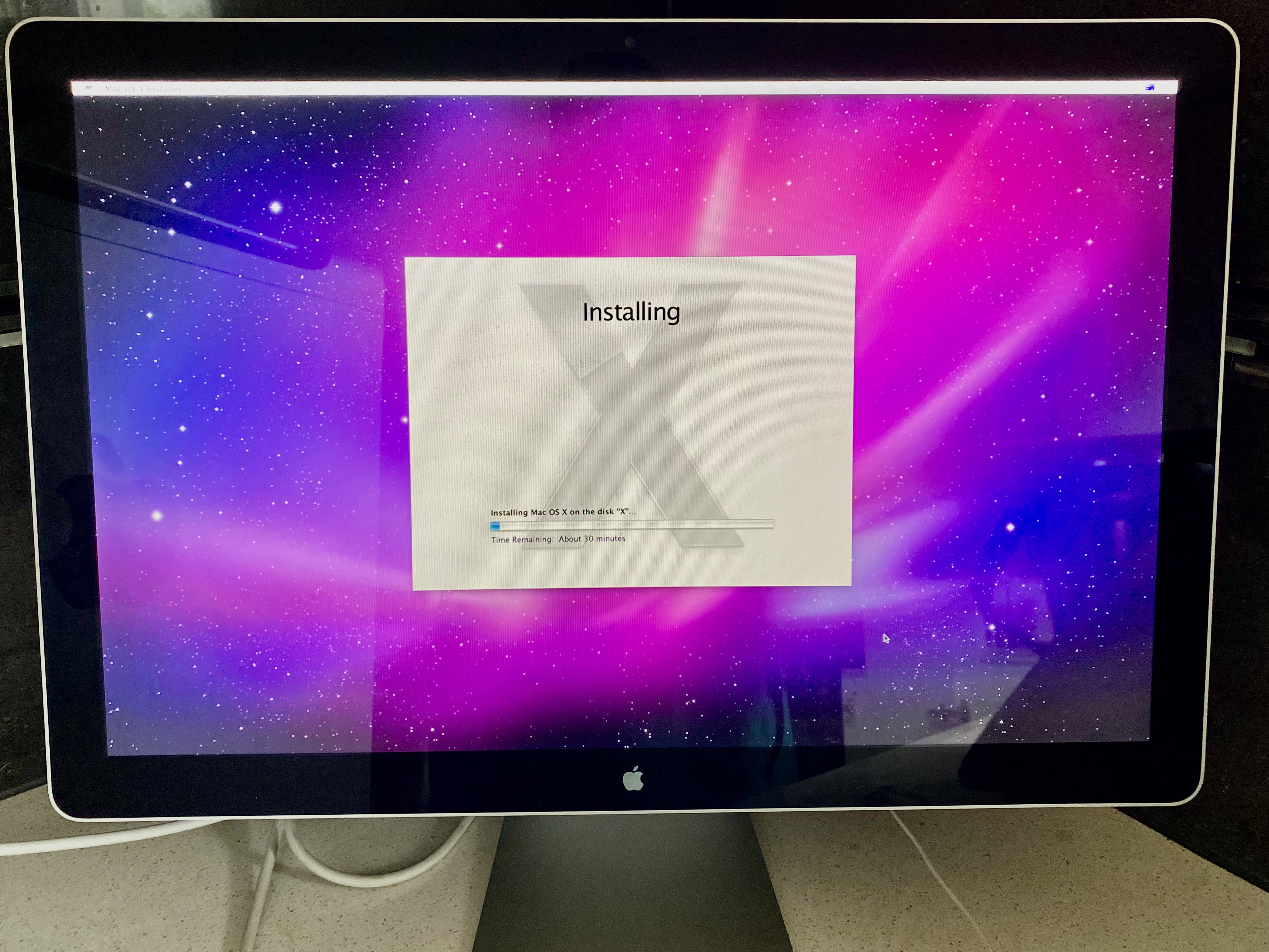
With DDR5 prices at record highs and DDR4 still a viable alternative, PC builders are getting creative. From repurp...

The upcoming release of Dawn of War 4* and Total War: Warhammer 40K marks a rare convergence of strategy games in t...

Backblaze’s latest drive reliability data shows hard drives reaching new durability benchmarks, yet Western Digital...

The Fancy Bow in *Mewgenics* is one of the game’s most cryptic items—given to players early on with no clear purpos...

Just days after cutting half its 2XKO development team, Riot Games has announced two new characters and a focus on...
Four wizards from *Pathfinder 2e*, *Dungeons & Dragons*, *Dungeon Crawl Classics*, and *Vagabond* were dropped into...

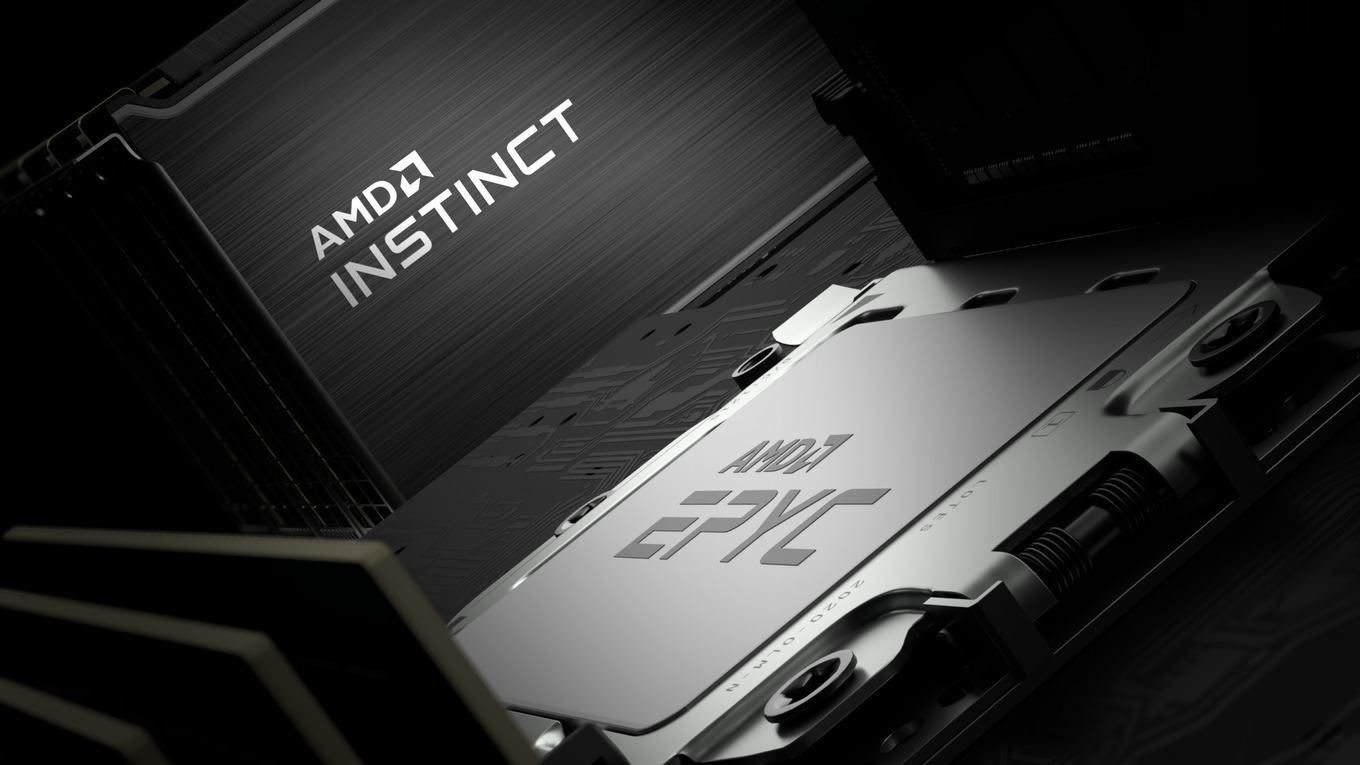
AMD’s new 800-series chipset brings Gen5 NVMe and DDR5 support to mainstream motherboards, and MSI’s latest B850 To...

A life-sized recreation of a 1990s computer speaker—complete with a peeling Goodwill sticker and a working volume k...