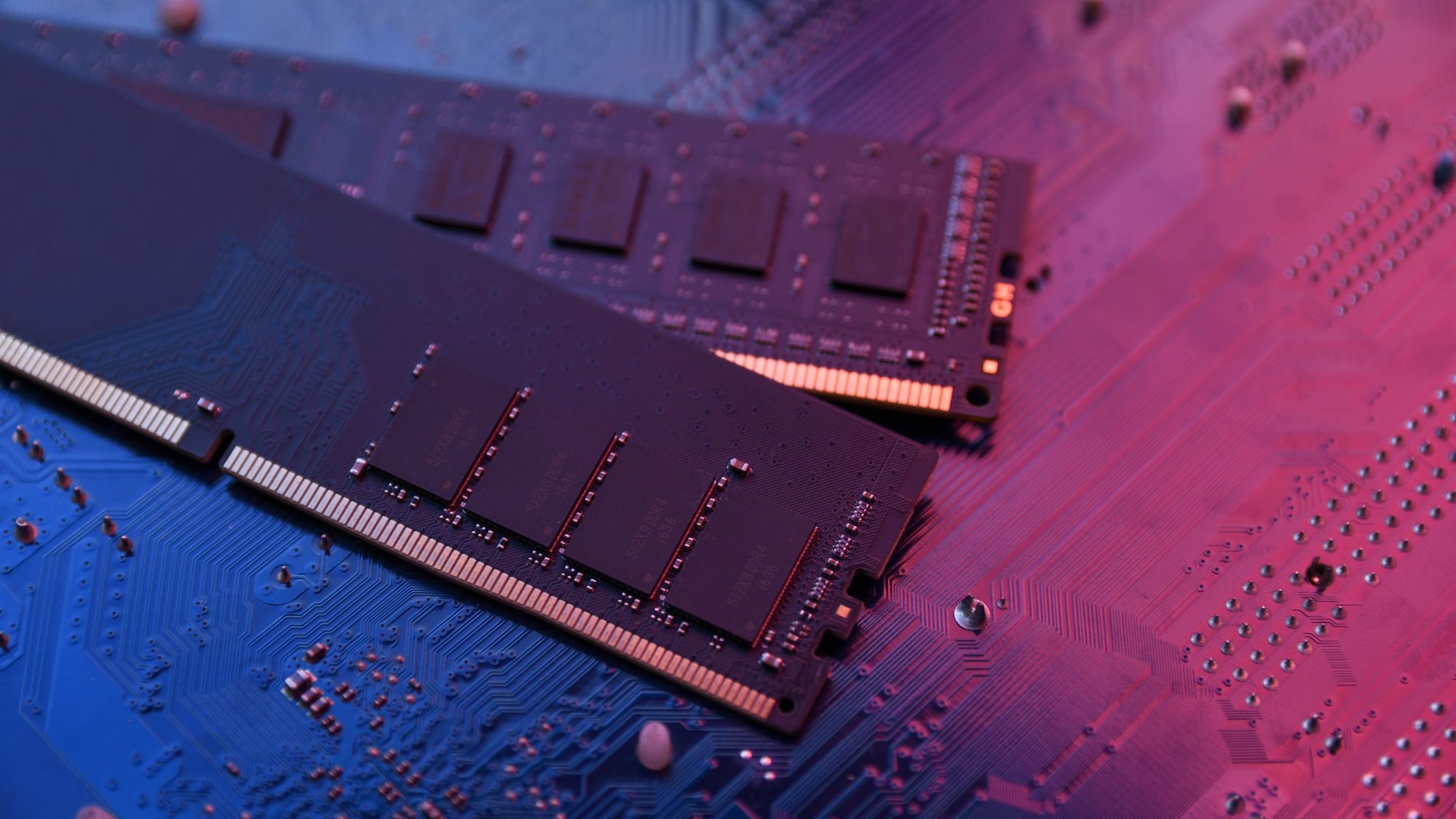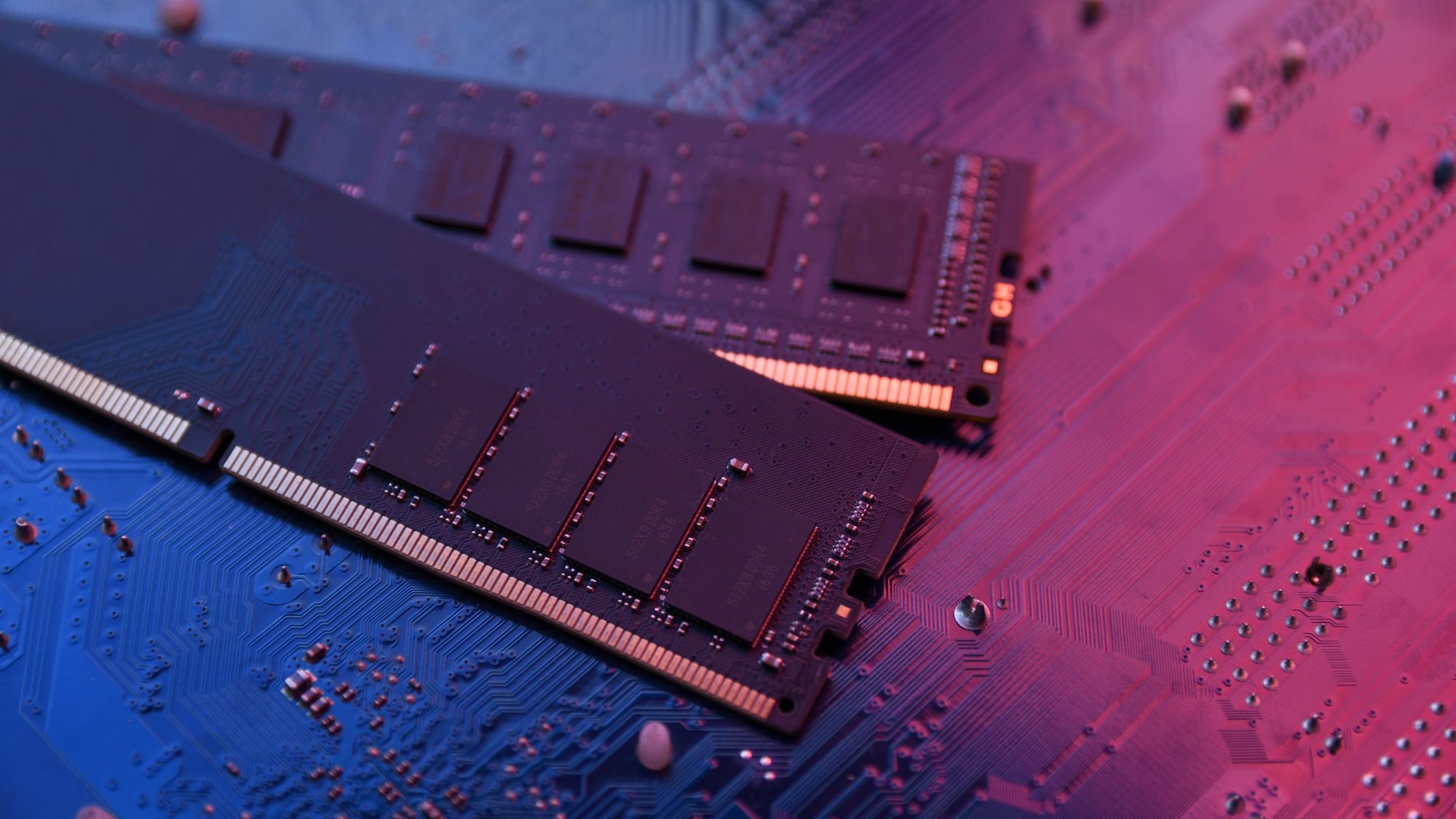
The surge in AI-driven workloads is putting unprecedented pressure on RAM supplies, with industry experts warning of long-term supply shortages and cost instability. Micron's analysis reveals a growing mismatch...








Dell introduces a lineup of high-performance workstations designed for demanding workloads. The new models focus on...
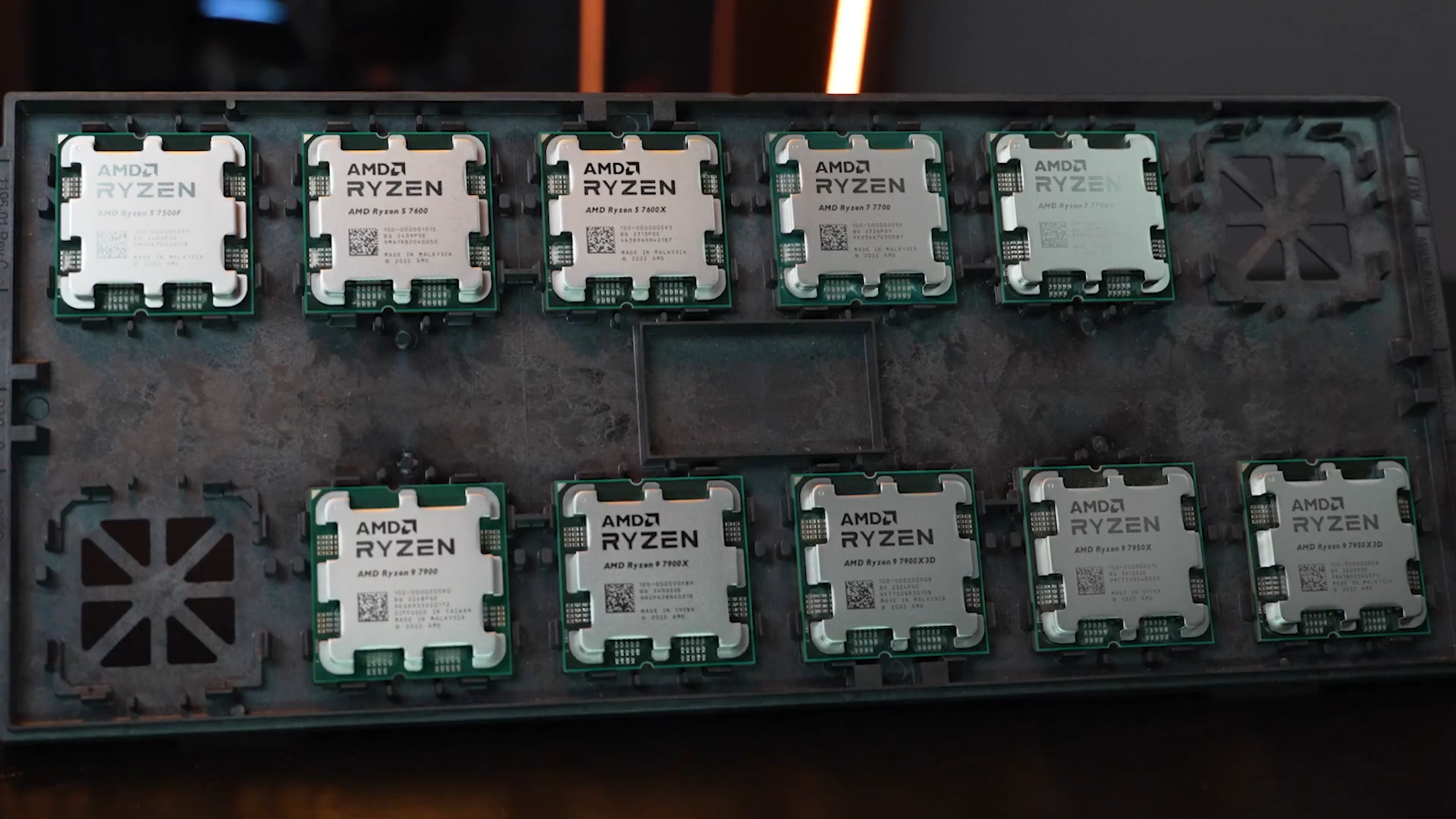
AMD has introduced the Ryzen 9 9950X3D2, a high-end CPU designed for developers and creators. This processor featur...

A new preconfigured bundle featuring the Ryzen 9 9800X3D, ASUS X870 motherboard, and 32GB DDR5 RAM delivers a balan...
The Acer Nitro V gaming laptop stands out by balancing performance and affordability, featuring an RTX 5060 GPU, 32...

Google is accelerating efforts to transition global encryption standards to quantum-resistant algorithms, warning t...

Apple is deepening its commitment to American manufacturing, adding four new supply chain partners as it seeks to o...

A next-generation GPU introduces significant performance gains for AI and data workloads, but its true impact lies...

The new AMD Ryzen 9 9950X3D marks a significant advancement in desktop computing, combining a 16-core Zen 5 archite...

NVIDIA's latest DLSS technology leap, now with frame generation and upscaling, forces a hard look at when to upgrad...

A new keyboard and mouse pair combine ultra-slim profiles with USB-C connectivity, targeting enterprise users who p...