A newly discovered Linux vulnerability allows attackers to bypass security checks and gain elevated system access, posing a serious risk to servers and workstations. Experts warn of active exploitation attempts...




The voice acting struggles behind Mass Effect: Andromeda reveal deeper tensions in game development, where open-wor...

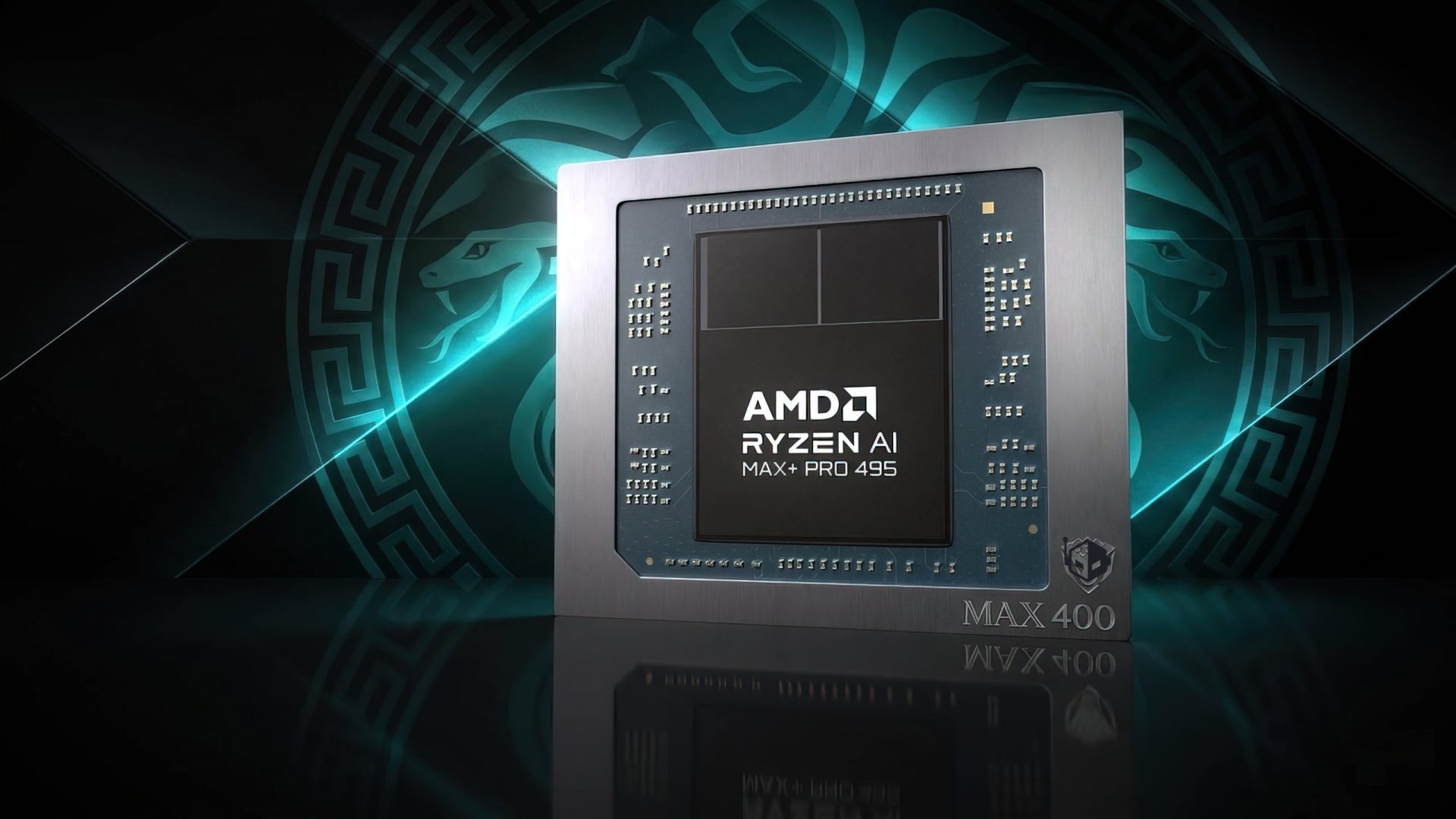
A new data processing platform is redefining the balance between performance and power efficiency in AI workloads,...
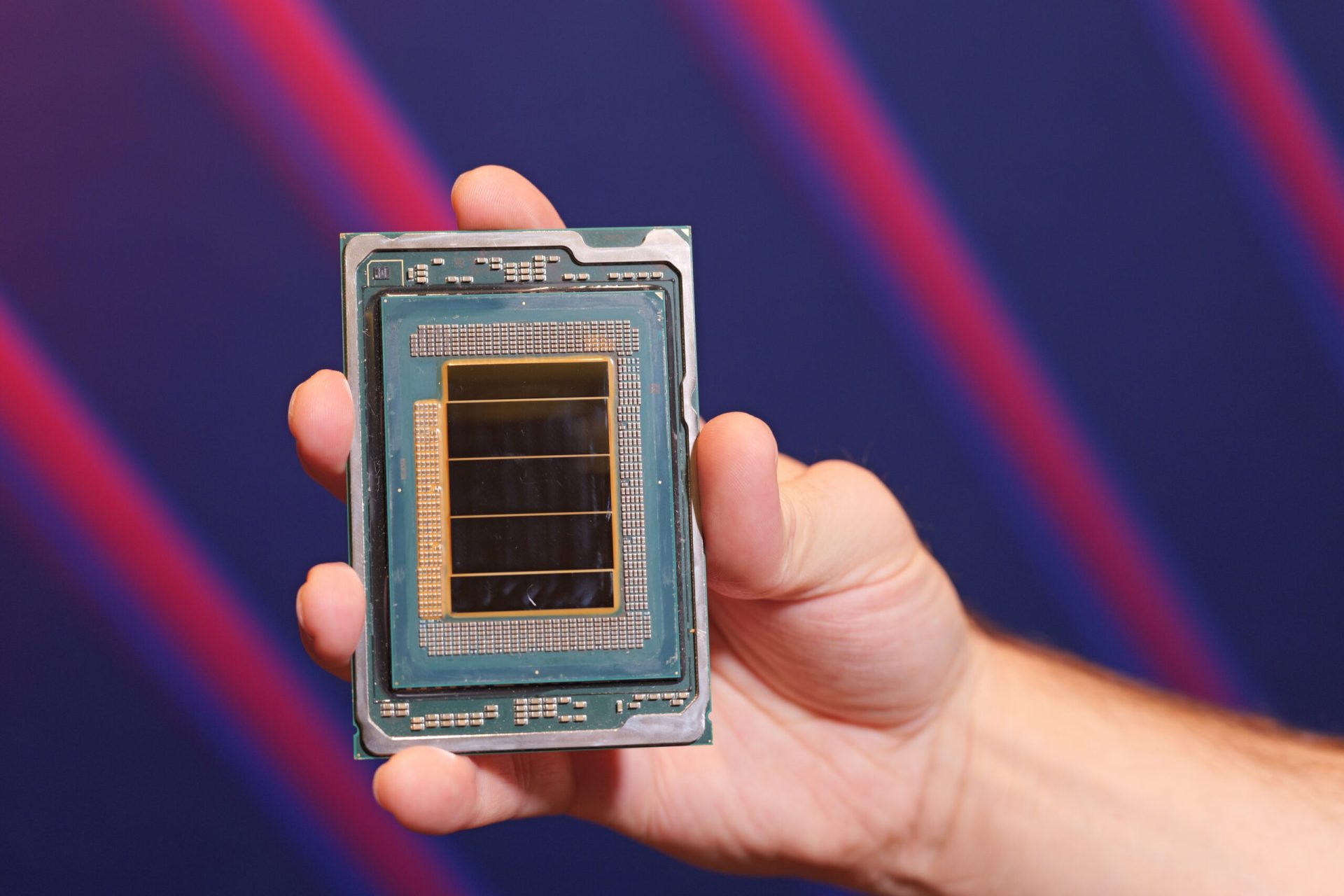
Intel is selling surplus client CPU dies for data center AI workloads, creating a cost-performance dilemma that cha...
A prolonged strike at Samsung is set to reduce output of critical memory components by up to four percent, with rec...

A curated list of free Windows applications that address common pain points, making daily computing more efficient...

A new 2-in-1 laptop promises portability and performance, but real-world benchmarks reveal a machine that can’t kee...

A potential remake of the original Assassin's Creed could reshape the franchise, leaving Black Flag Resynced as a n...

Sony has increased the price of its PS5 consoles and PS Portal remote play device in six additional countries, citi...

The Steam Controller will arrive on May 4 as a standalone device, distinct from the Steam Machine. Its design and t...
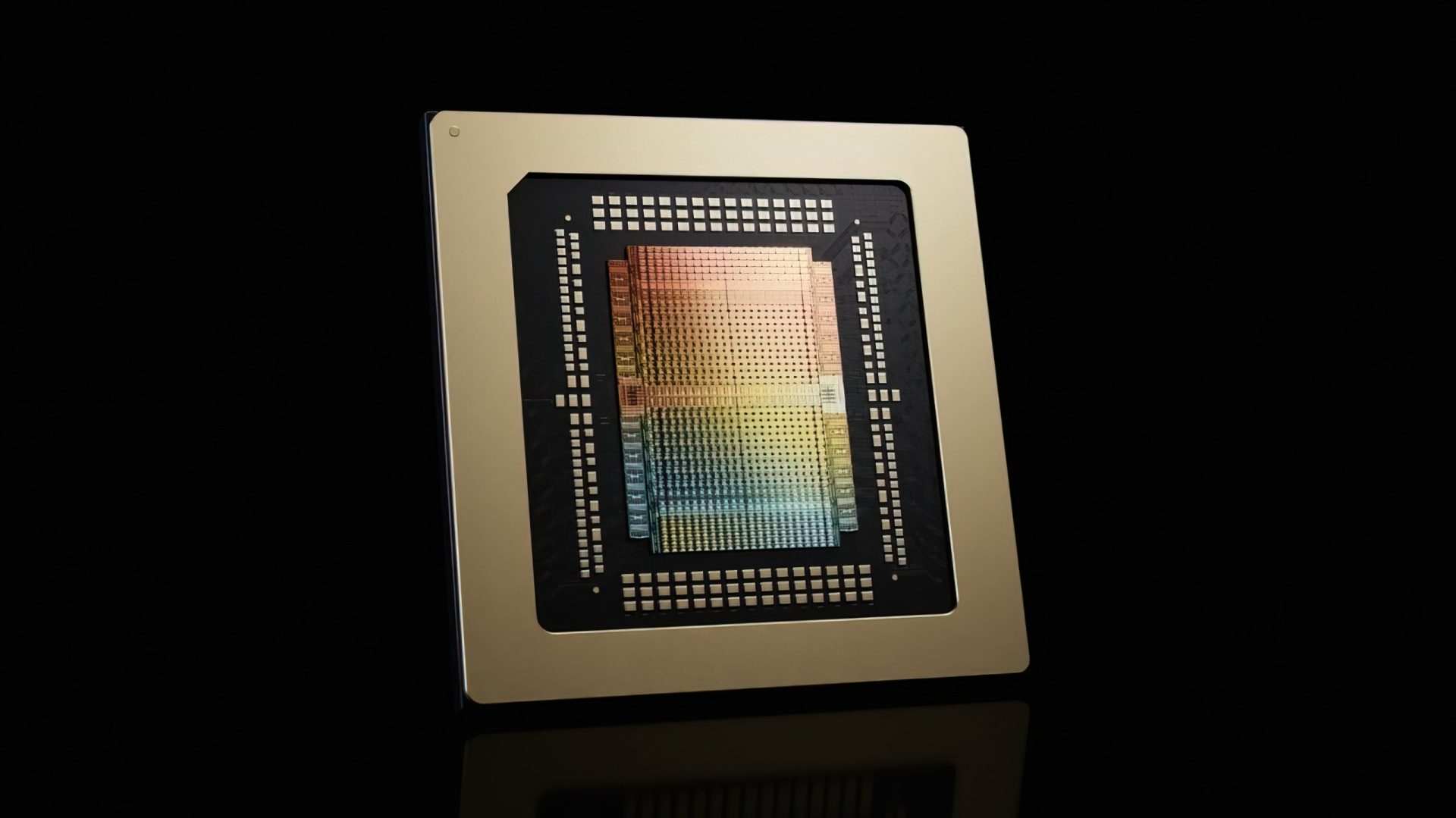
NVIDIA has introduced a significant advancement in AI inferencing, promising a 35x performance boost. This developm...