
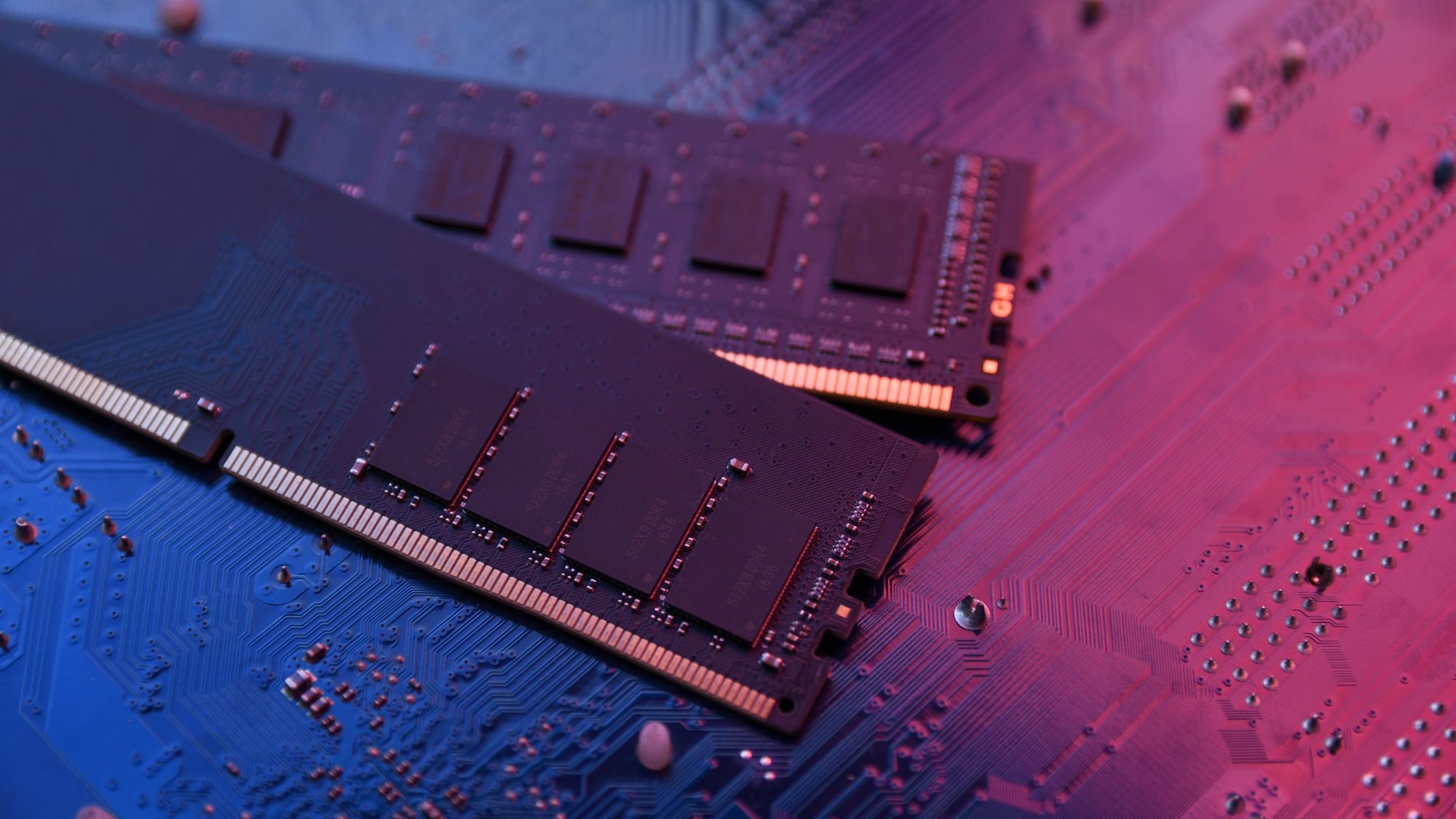
The surge in AI-driven workloads is putting unprecedented pressure on RAM supplies, with industry experts warning of long-term supply shortages and cost instability. Micron's analysis reveals a growing mismatch...









The EP200 2026 chair from Boulies redefines ergonomic seating with a focus on breathability, durability, and adapta...
After years of volatility and skepticism, Intel’s stock has rebounded sharply, reaching a peak not seen since its 2...

Acer's refurbished Aspire 3 laptop, now priced below half its retail cost, offers a rare combination of 16GB DDR5 R...

Players adapting to World of Warcraft's updated combat interface report a surprising sense of calm, though some cus...
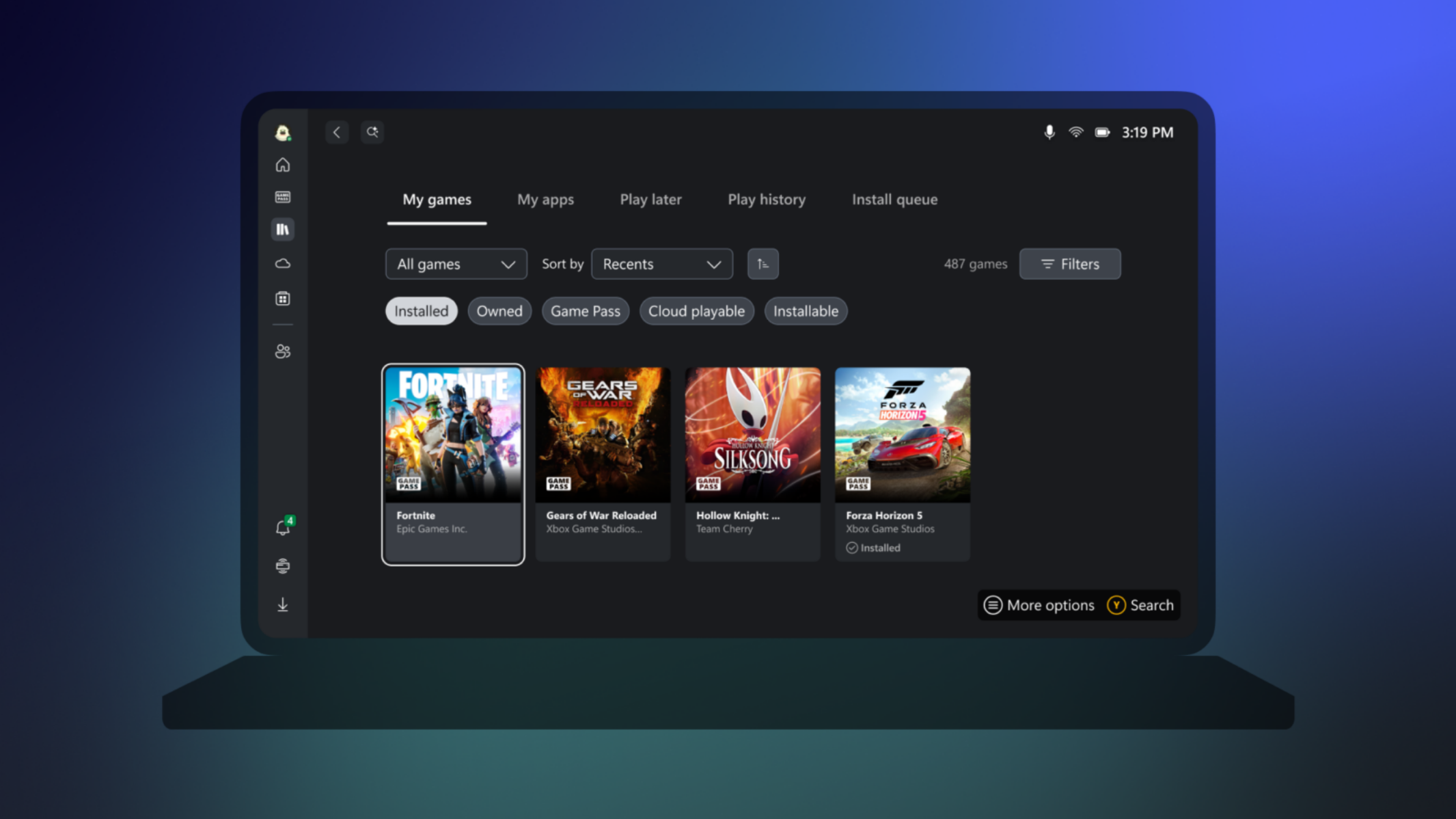
The Xbox app is now available on all ARM-based Windows 11 devices, expanding cloud gaming options and local playabi...

Marathon, Bungie’s latest extraction shooter, is set to redefine the genre with a deeper narrative focus and an evo...

The Razer Thunderbolt 5 Dock delivers extreme performance with 80 Gbps bandwidth and PCIe 4.0 NVMe support, but its...

As memory prices are projected to surge in 2026, Nintendo faces a critical juncture in its pricing strategy. The co...

A small indie studio based in Brazil introduces Mechborn, a roguelike deckbuilder that redefines combat strategy th...
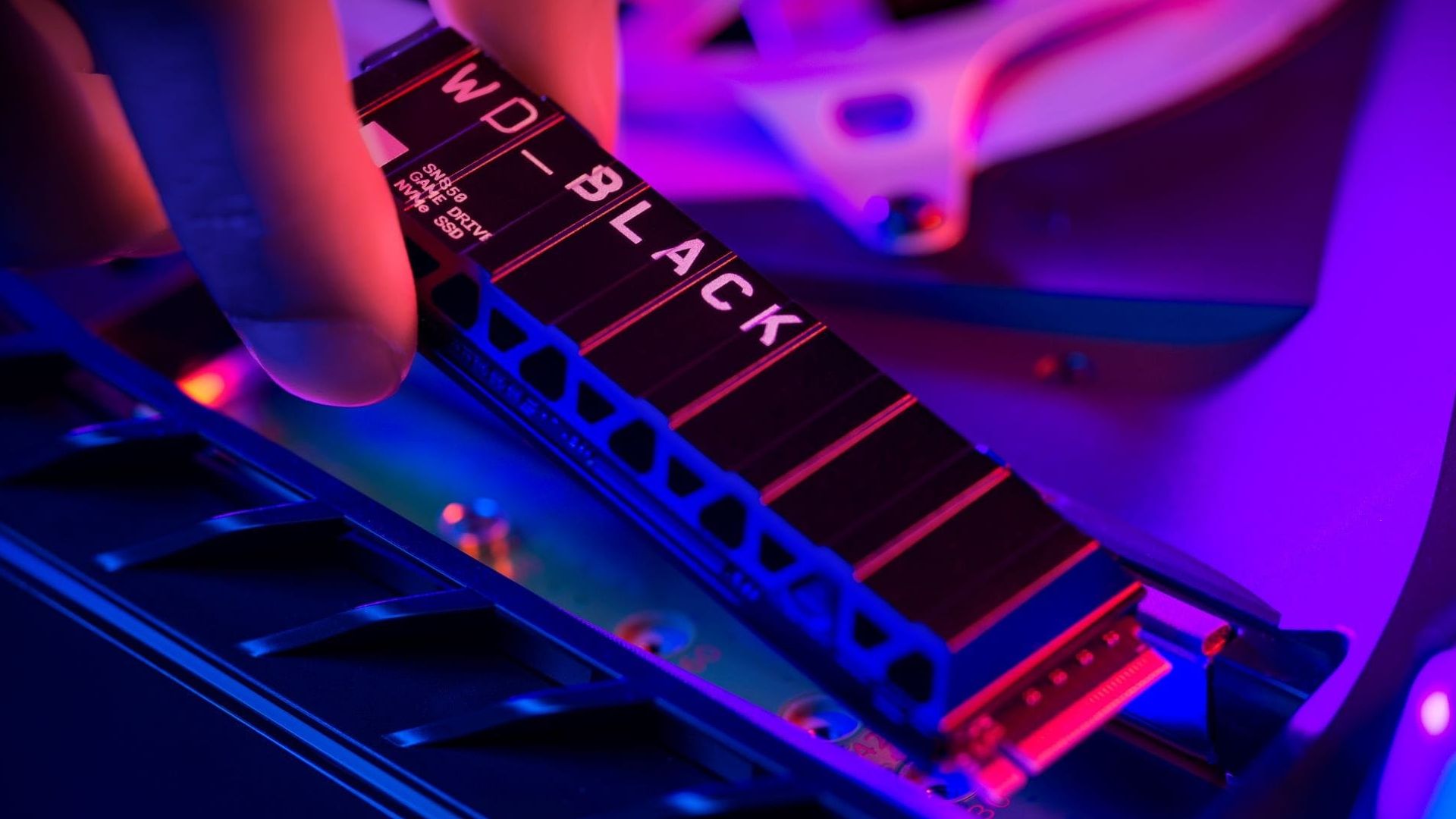
Prices for budget-friendly 1TB SSDs have surged in recent months, signaling a shift that could leave consumers payi...





