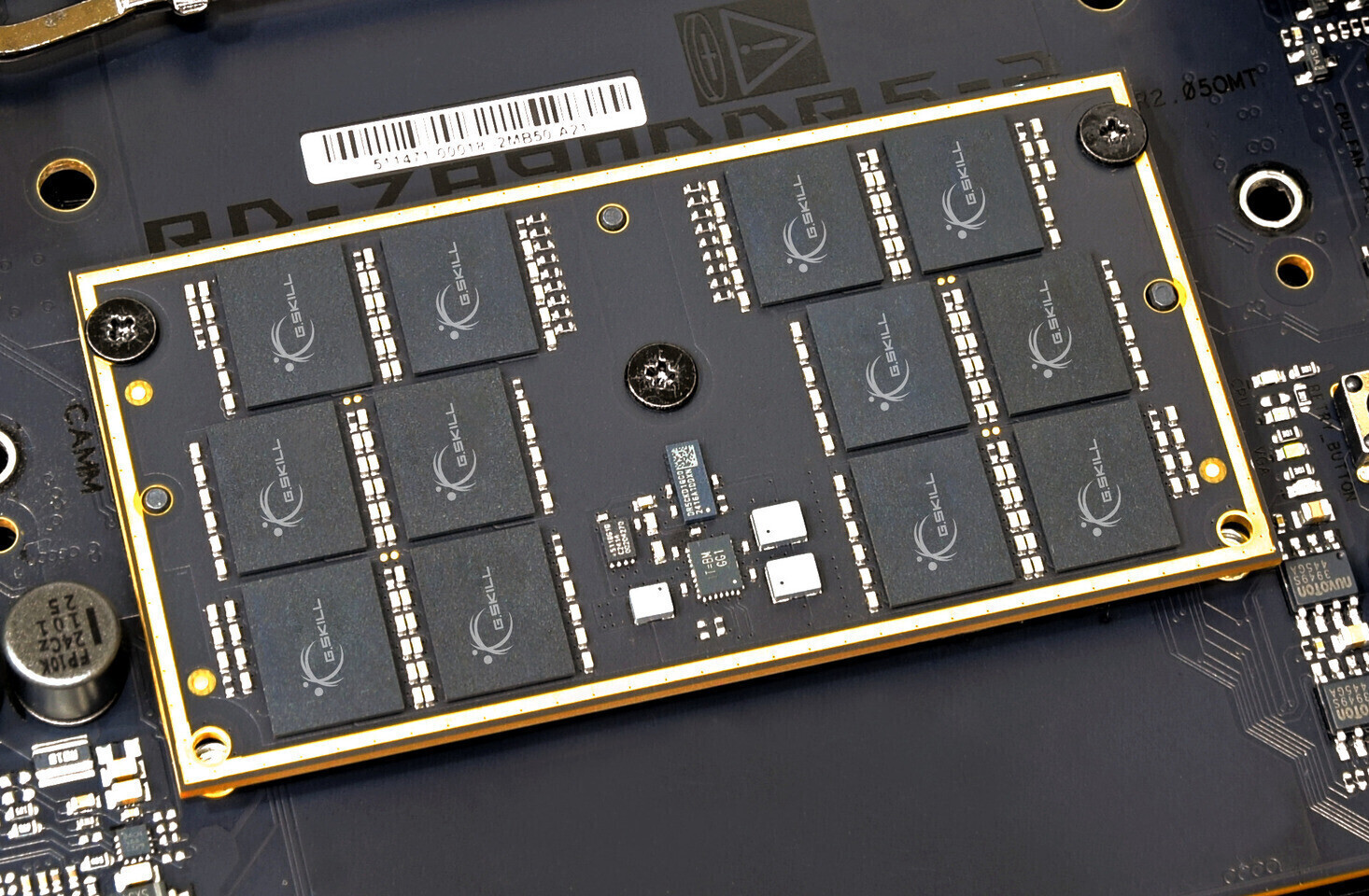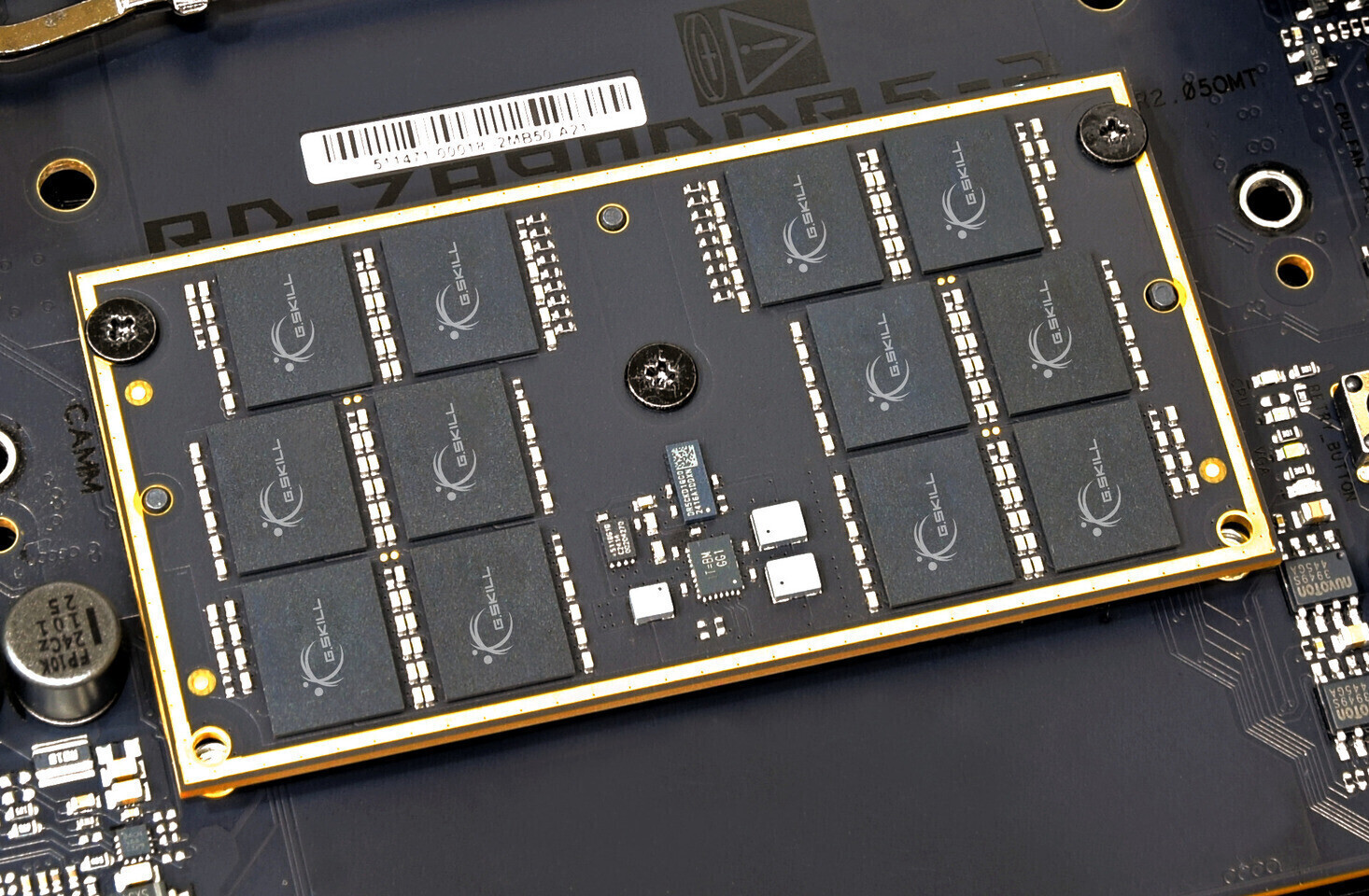
The DDR6 standard is poised to redefine performance benchmarks with speeds up to 17,600 MT/s, but its adoption hinges on overcoming significant engineering challenges. This article explores the tradeoffs behind...





Intel's foundry business is accelerating, with a major partnership announced with Tesla to use Intel's advanced pro...

The latest Ubuntu LTS release, codenamed 'Resolute Raccoon,' introduces significant upgrades to the desktop experie...
Microsoft's latest IDE, Visual Studio Pro 2026, is now available for $34.97—down from its usual $499.99—until May 1...

A new collaboration between Final Fantasy XIV and HYTE introduces a premium PC case designed for fans, blending gam...

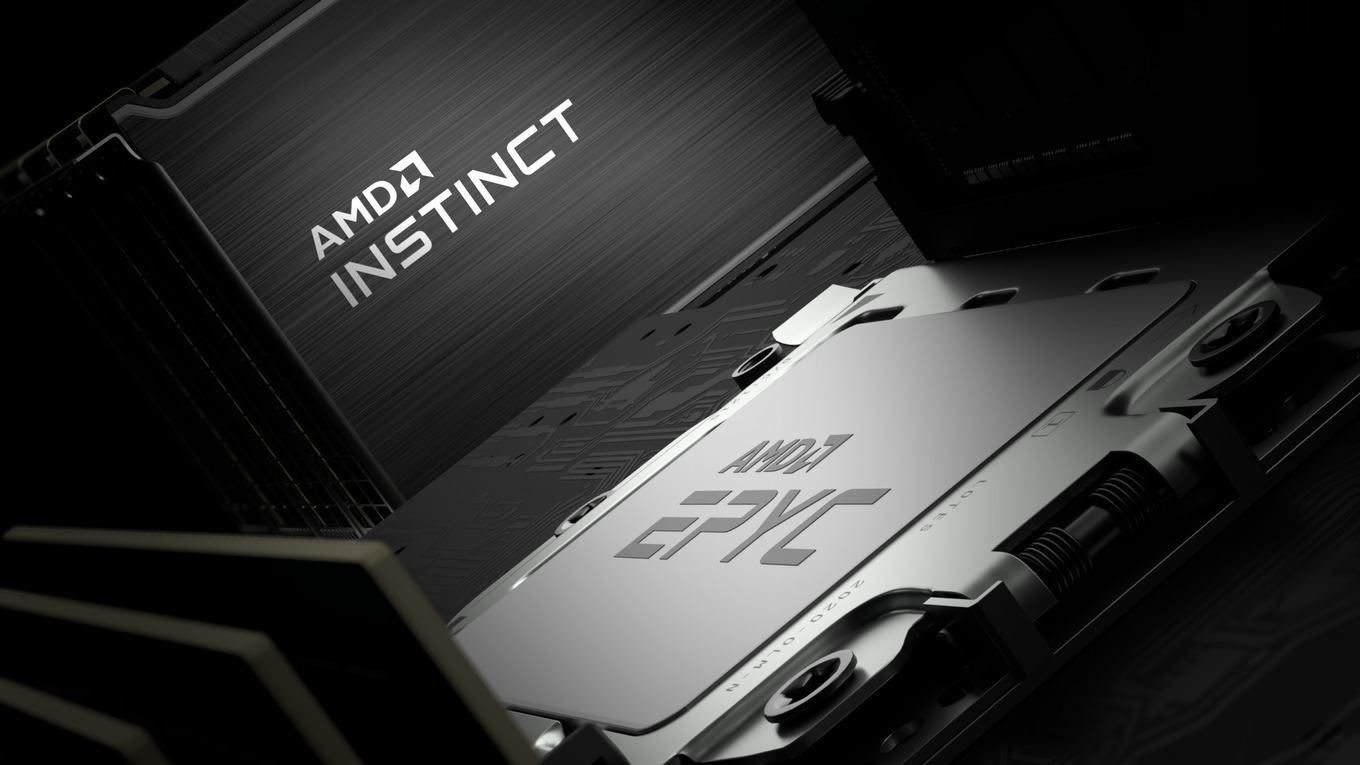
Intel's foundry business is expanding its footprint in AI and workstation segments, but its success hinges on execu...

Forza Horizon 5 on PlayStation 5 has sold over 5 million units, nearly matching its PC sales despite a four-year de...

The HP Envy 16 laptop brings professional-grade performance—32GB RAM, an RTX 4050 GPU, and a 16-inch display—to the...
The new silicone case for Wooting's 60HE v2 keyboard introduces a lighter, more flexible alternative to aluminum, b...

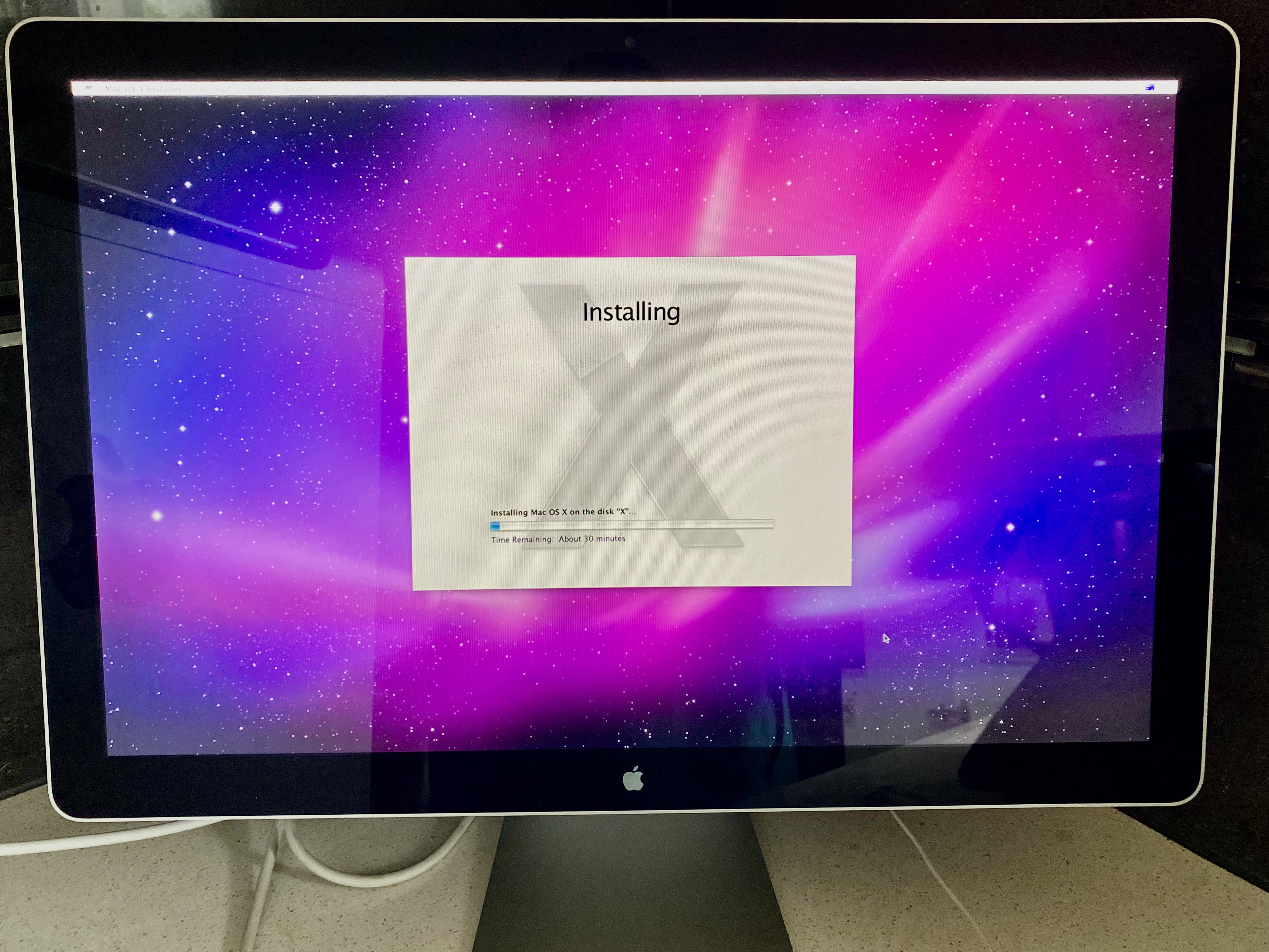
Apple’s MacBook line is expected to see a 21.7% increase in shipments next year, contrasting with industry-wide con...

A $160 price point for a 27-inch 1440p monitor challenges conventional cost-performance trade-offs in enterprise en...