The DDR6 standard is poised to redefine performance benchmarks with speeds up to 17,600 MT/s, but its adoption hinges on overcoming significant engineering challenges. This article explores the tradeoffs behind...






Microsoft's Xbox division is taking a different path at this year's Summer Game Fest, with its own dedicated showca...

A 40% price cut on Eufy's solar-powered security cameras makes them the most affordable in their category, but buye...

The US PC market is facing cost pressures from surging memory prices, but Apple’s new M4 Air with 16 GB RAM at $999...

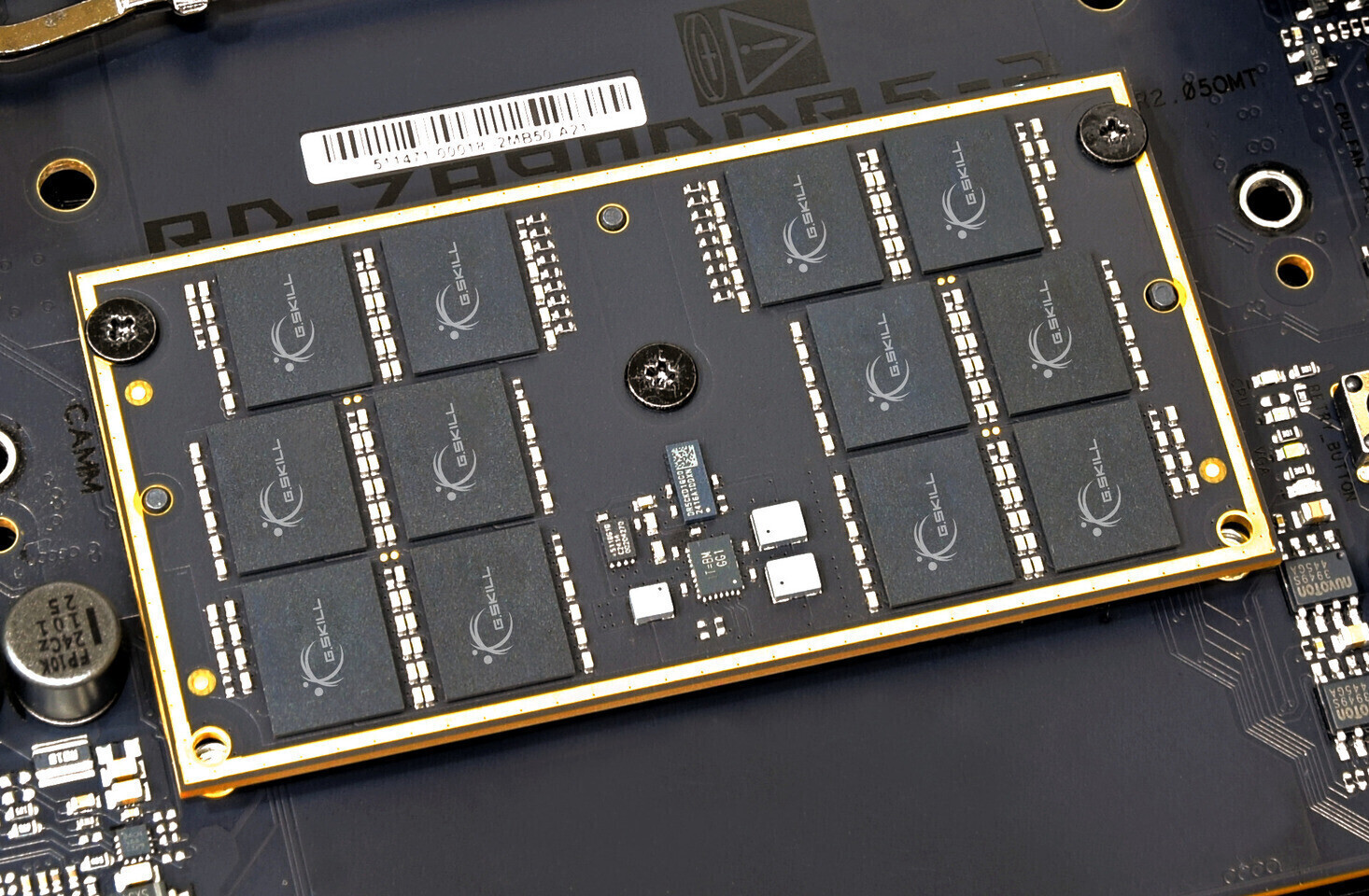
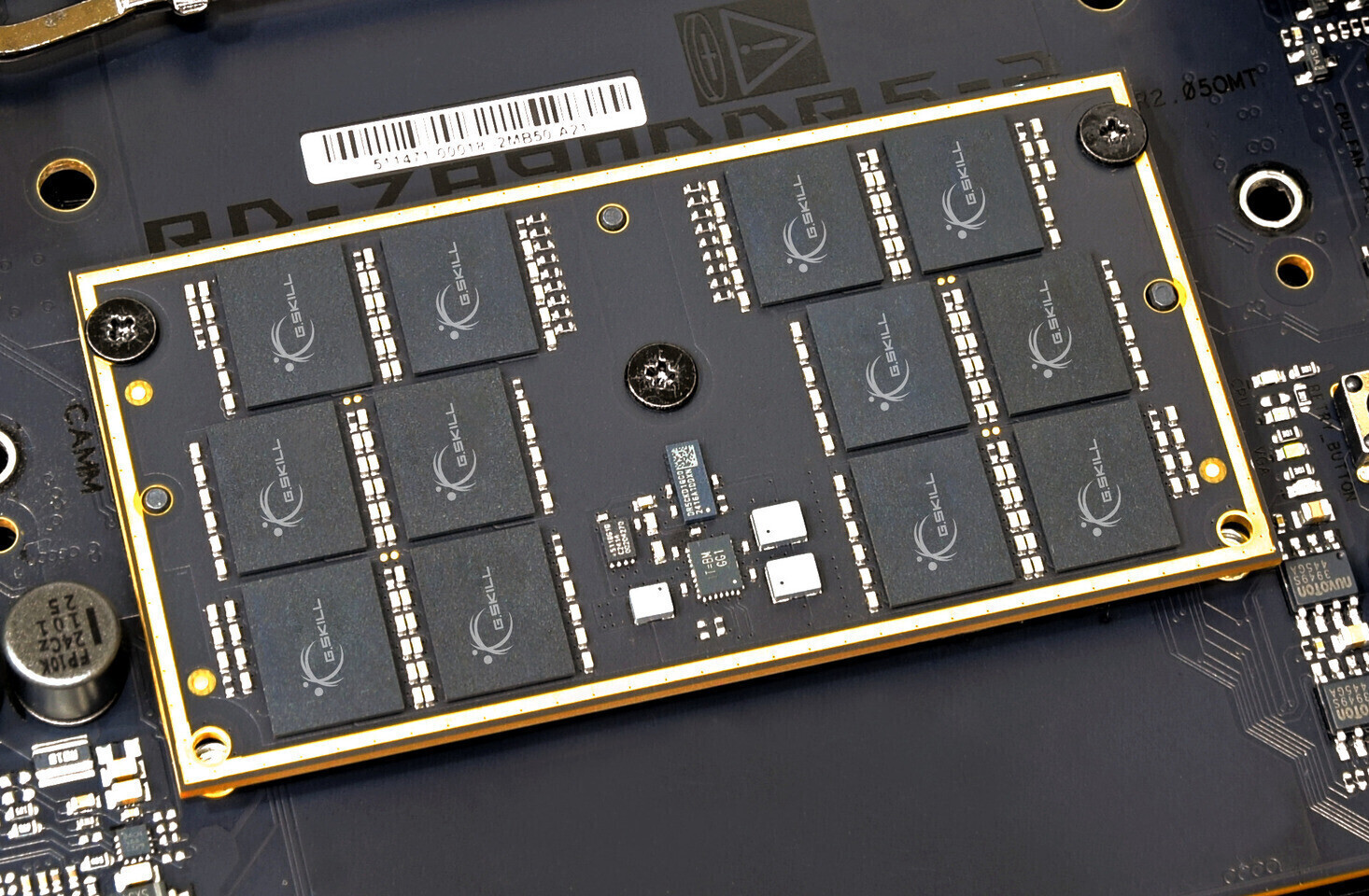
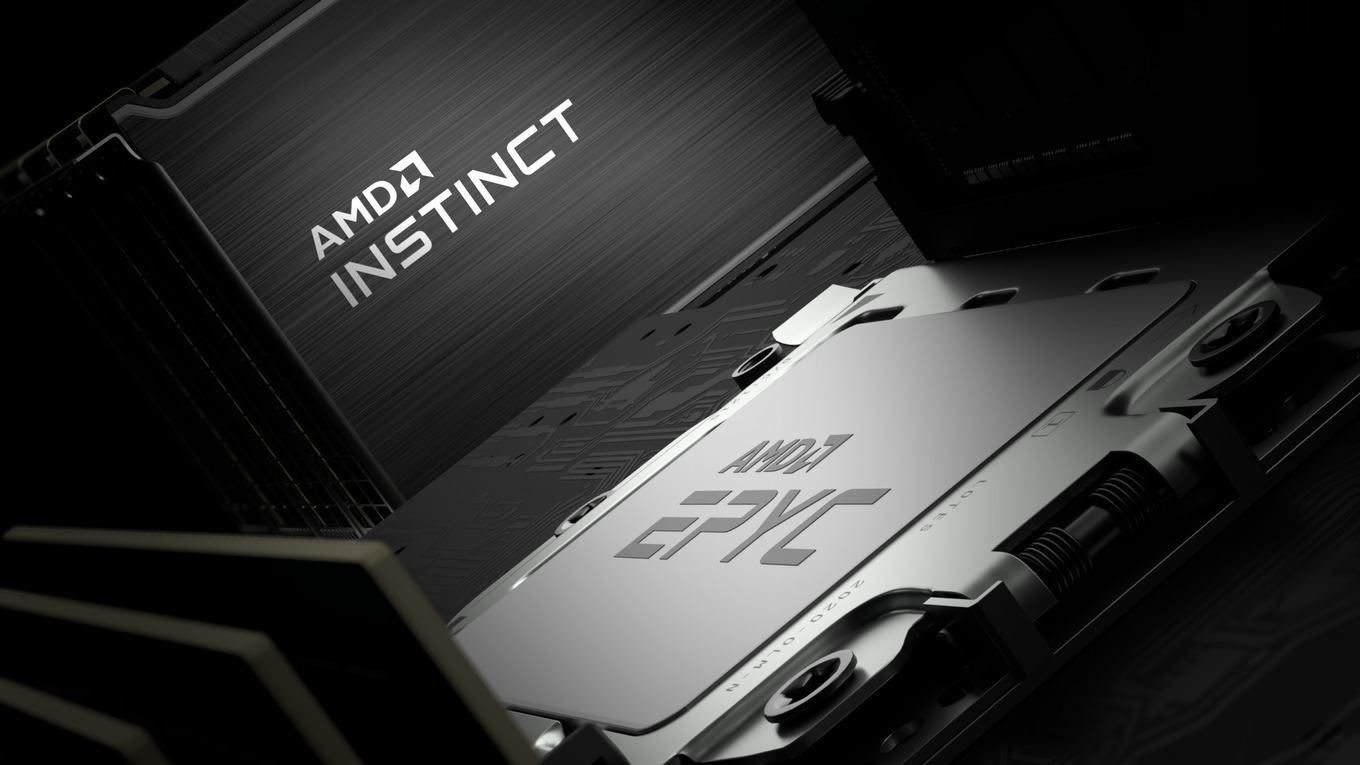
A breakthrough in memory stacking could change how GPUs handle data, but supply chain and cost hurdles remain. Anal...

A new ASRock motherboard is said to be the first to officially support AMD's Ryzen 7 9800X3D, offering users a high...

A fresh web-based platform consolidates nearly 100 essential utilities into a single, ad-free interface. Designed f...

For players navigating Root’s End Ruins, a precise farming method leverages the infinite loop to maximize gear drop...

Nintendo’s rumored Switch 2 limited edition console, tied to the Ocarina of Time remake, could signal a shift in ga...

Dell's latest OLED monitor, the U3226Q, delivers a stunning visual experience with its 4K resolution and HDR suppor...

A closer look at how Windows 11 optimizations balance speed with storage lifespan, revealing the hidden costs of fa...