A newly discovered Linux vulnerability allows attackers to bypass security checks and gain elevated system access, posing a serious risk to servers and workstations. Experts warn of active exploitation attempts...




A new collaboration between Final Fantasy XIV and HYTE introduces a premium PC case designed for fans, blending gam...

Intel's foundry business is expanding its footprint in AI and workstation segments, but its success hinges on execu...

Forza Horizon 5 on PlayStation 5 has sold over 5 million units, nearly matching its PC sales despite a four-year de...

The HP Envy 16 laptop brings professional-grade performance—32GB RAM, an RTX 4050 GPU, and a 16-inch display—to the...
The new silicone case for Wooting's 60HE v2 keyboard introduces a lighter, more flexible alternative to aluminum, b...

Apple’s MacBook line is expected to see a 21.7% increase in shipments next year, contrasting with industry-wide con...

A $160 price point for a 27-inch 1440p monitor challenges conventional cost-performance trade-offs in enterprise en...
Microsoft’s Xbox division is overhauling its approach to Game Pass, exclusivity, and cloud gaming, aiming to addres...

Seagate’s latest storage solutions eliminate external power while delivering professional-grade speeds, catering to...
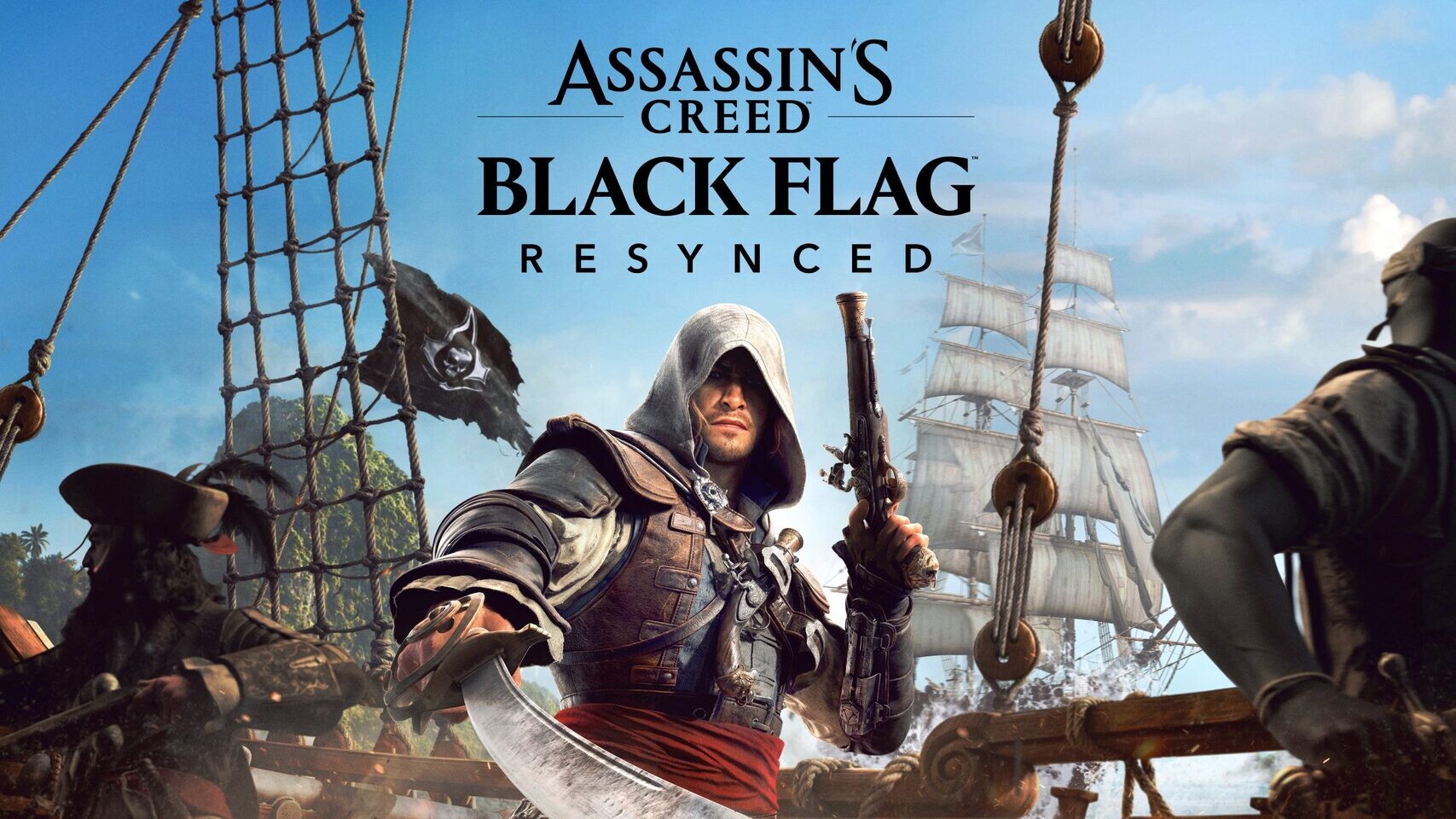
The refreshed version of the 2013 classic arrives with updated visuals, ray-traced lighting, and optimized performa...