The DDR6 standard is poised to redefine performance benchmarks with speeds up to 17,600 MT/s, but its adoption hinges on overcoming significant engineering challenges. This article explores the tradeoffs behind...








Memory and storage now dominate HP’s hardware costs, pushing prices higher for consumers. The company’s financial s...

Dell’s new PowerEdge XR9700 is a sealed, liquid-cooled server built for extreme outdoor deployments—from utility po...

The latest patch for *Arc Raiders* introduces five major content additions—but the real game-changers are the subtl...

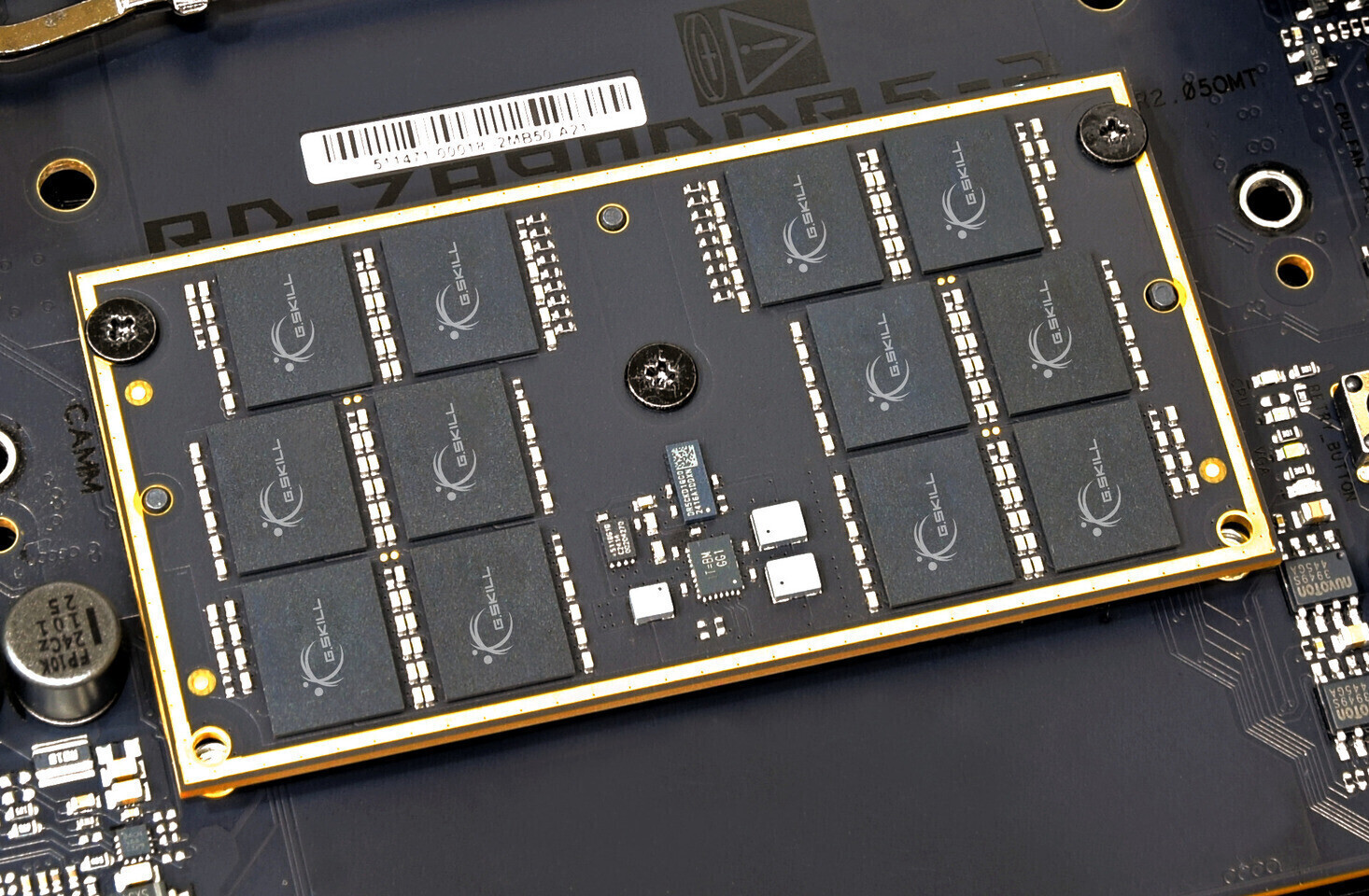
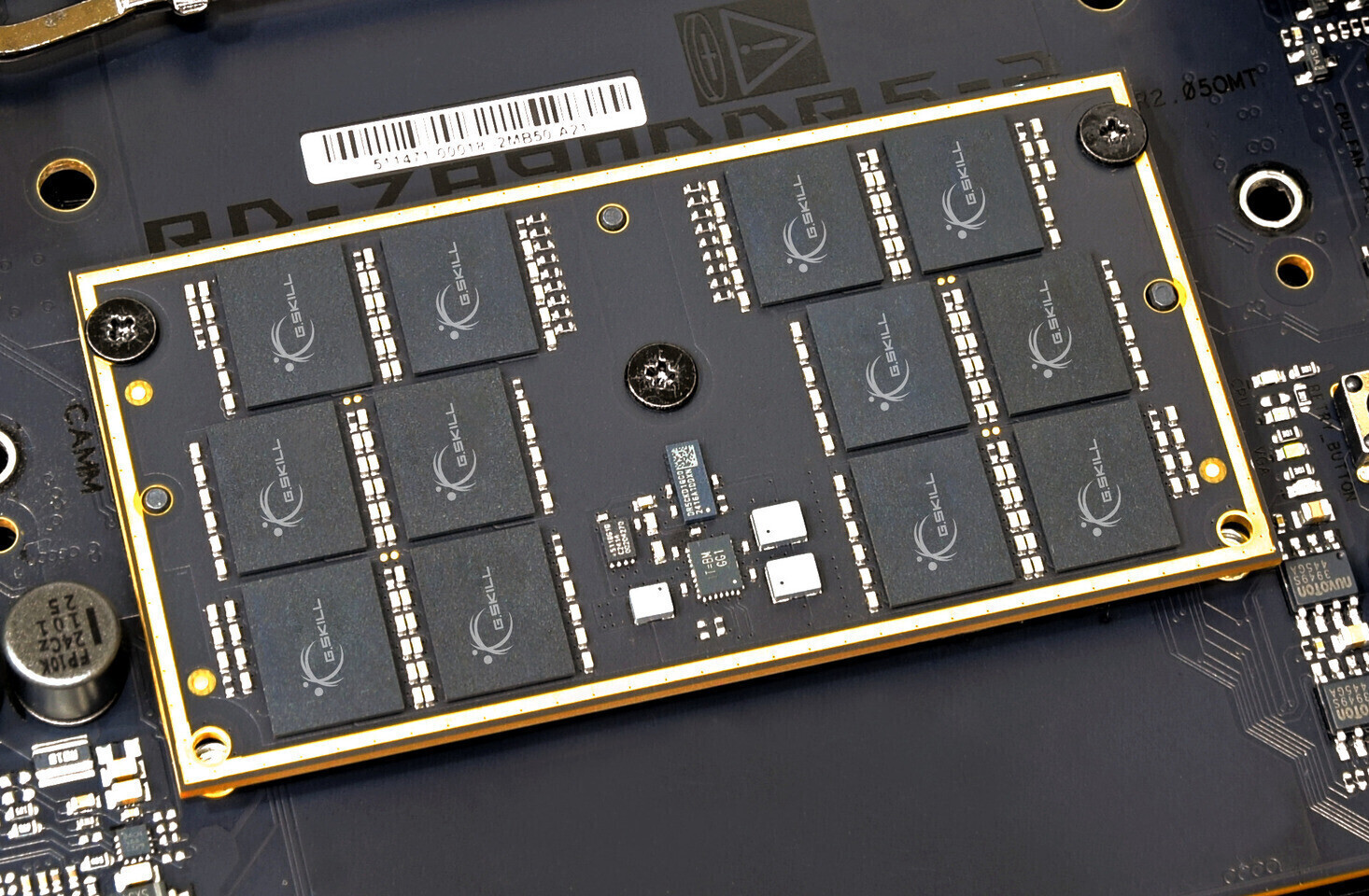
Micron’s new GDDR7 chips—capable of 36 Gbps bandwidth—could enable graphics cards with up to 96GB VRAM, but the tec...

After facing intense backlash over its controversial age verification plans, Discord has abandoned its original tim...
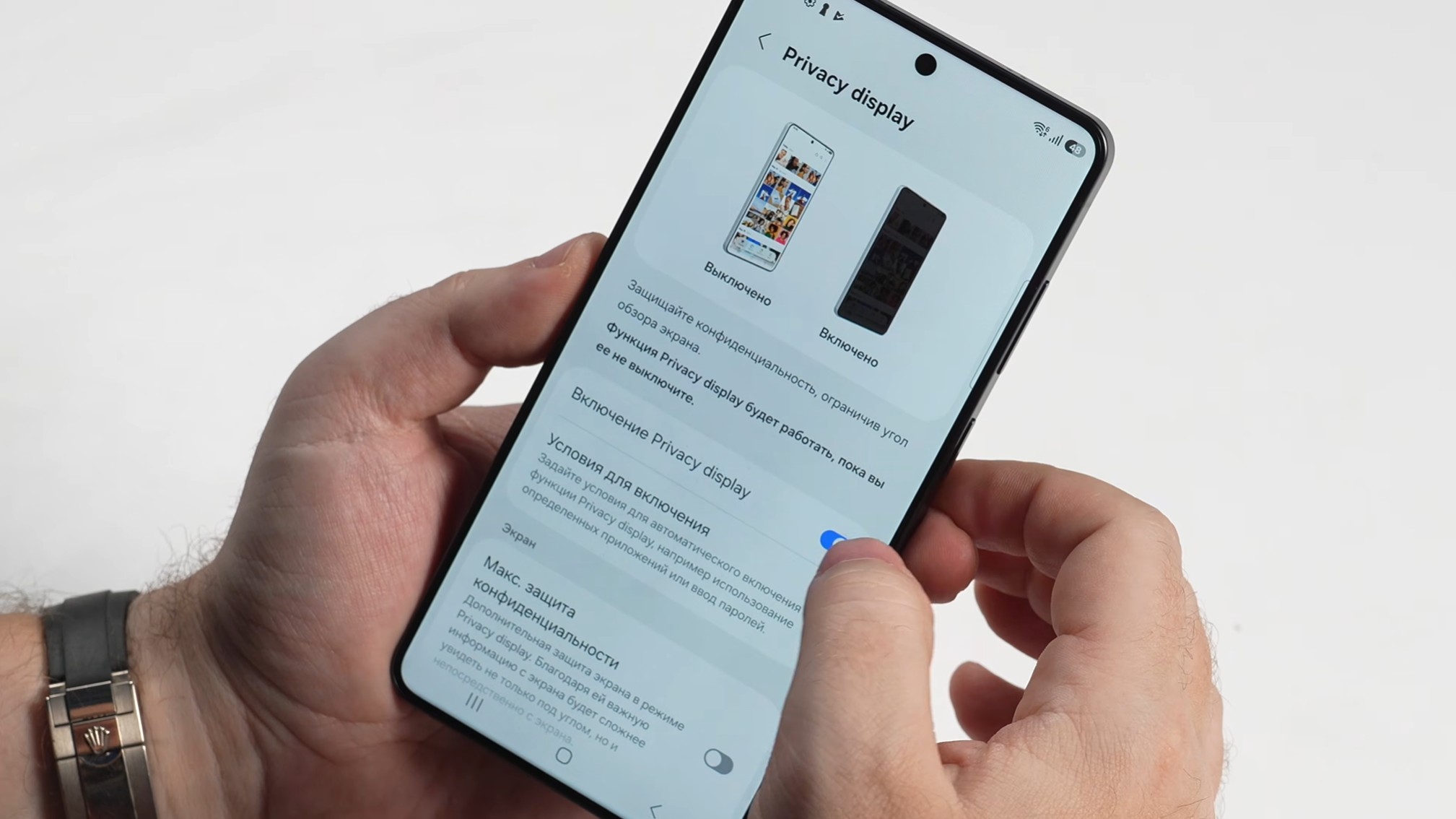
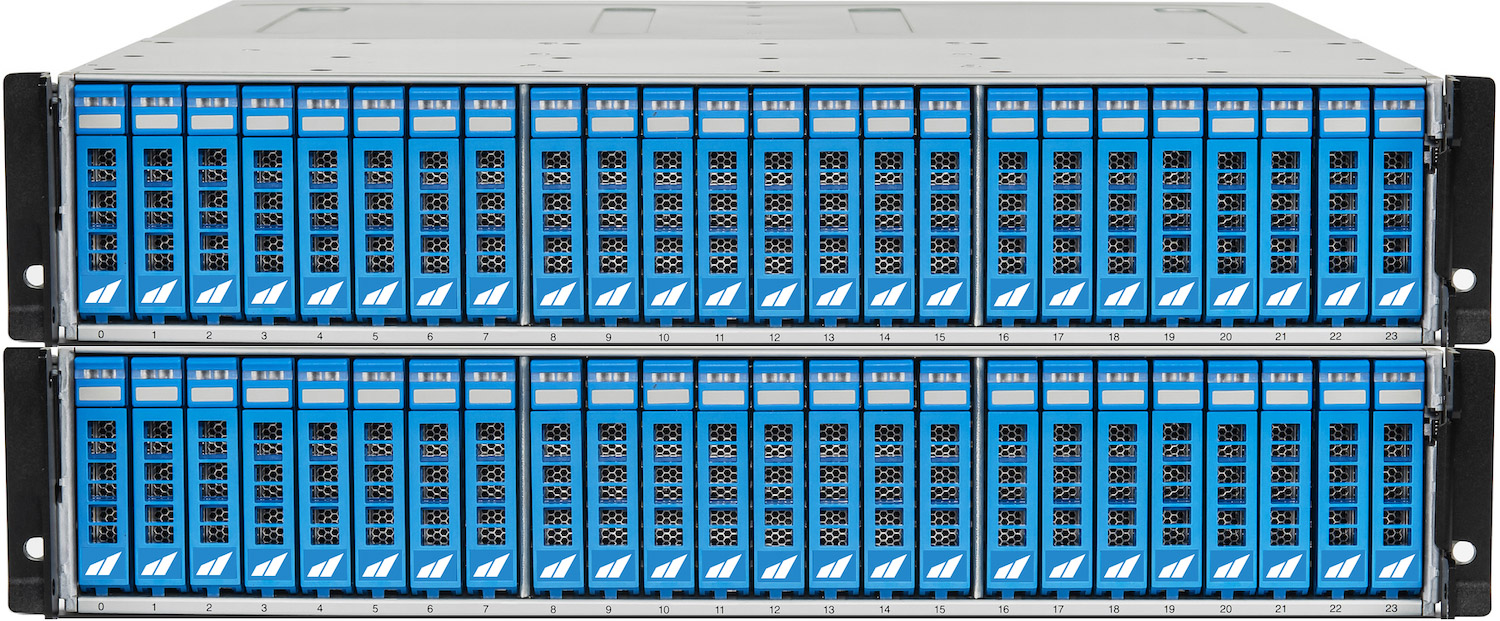
The CP152-1 merges rear-accessible drive bays with built-in RAID 1, eliminating cables and simplifying high-density...

A new restaurant sim strips away customer service stress by hiding diners behind shutters—but does that mean gamepl...

A detailed technical breakdown of how Resident Evil Requiem performs across a spectrum of hardware, from portable g...

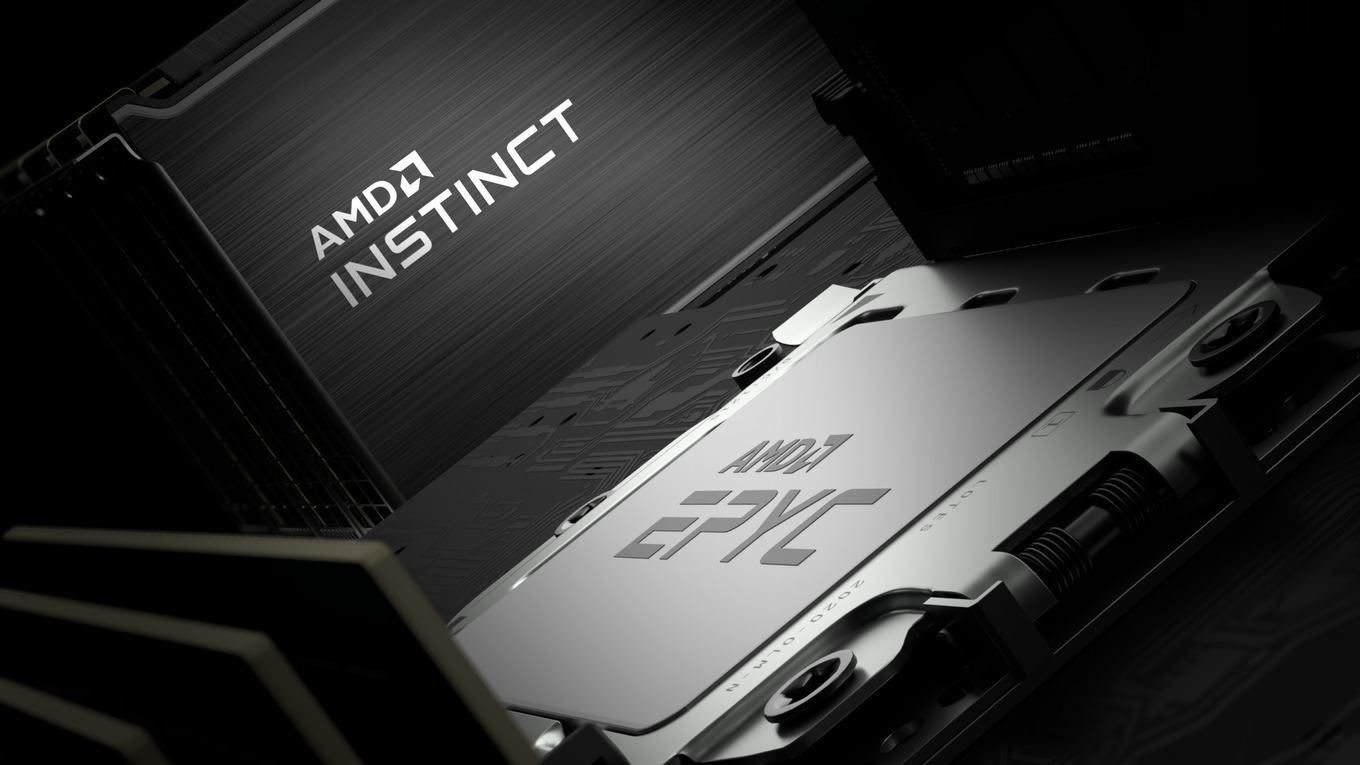
AMD’s new EPYC 8005 series bridges the gap between its high-end EPYC 9005 and lower-tier EPYC 4005 chips, offering...

A single-monitor arm from Huanuo is now just $33.23—26% off—offering an affordable way to eliminate neck strain and...