A newly discovered Linux vulnerability allows attackers to bypass security checks and gain elevated system access, posing a serious risk to servers and workstations. Experts warn of active exploitation attempts...




The RTX 50-series 'Blackwell' architecture introduces optimized precision formats that cut memory usage by 60% and...

A new trailer for Nekome: Nazi Hunter reveals a third-person stealth-action game where players take on the role of...

The latest installment in the series introduces a darker narrative and deeper conservation mechanics, challenging p...

A fresh sci-fi action-adventure game from Capcom has surged in popularity, with over two million demo downloads and...

A fresh Yoshi adventure is coming to the Nintendo Switch 2 in late spring, blending classic gameplay with new mecha...

NVIDIA's latest DLSS 4.5 Dynamic introduces adaptive frame generation, dynamically adjusting between no frame gener...
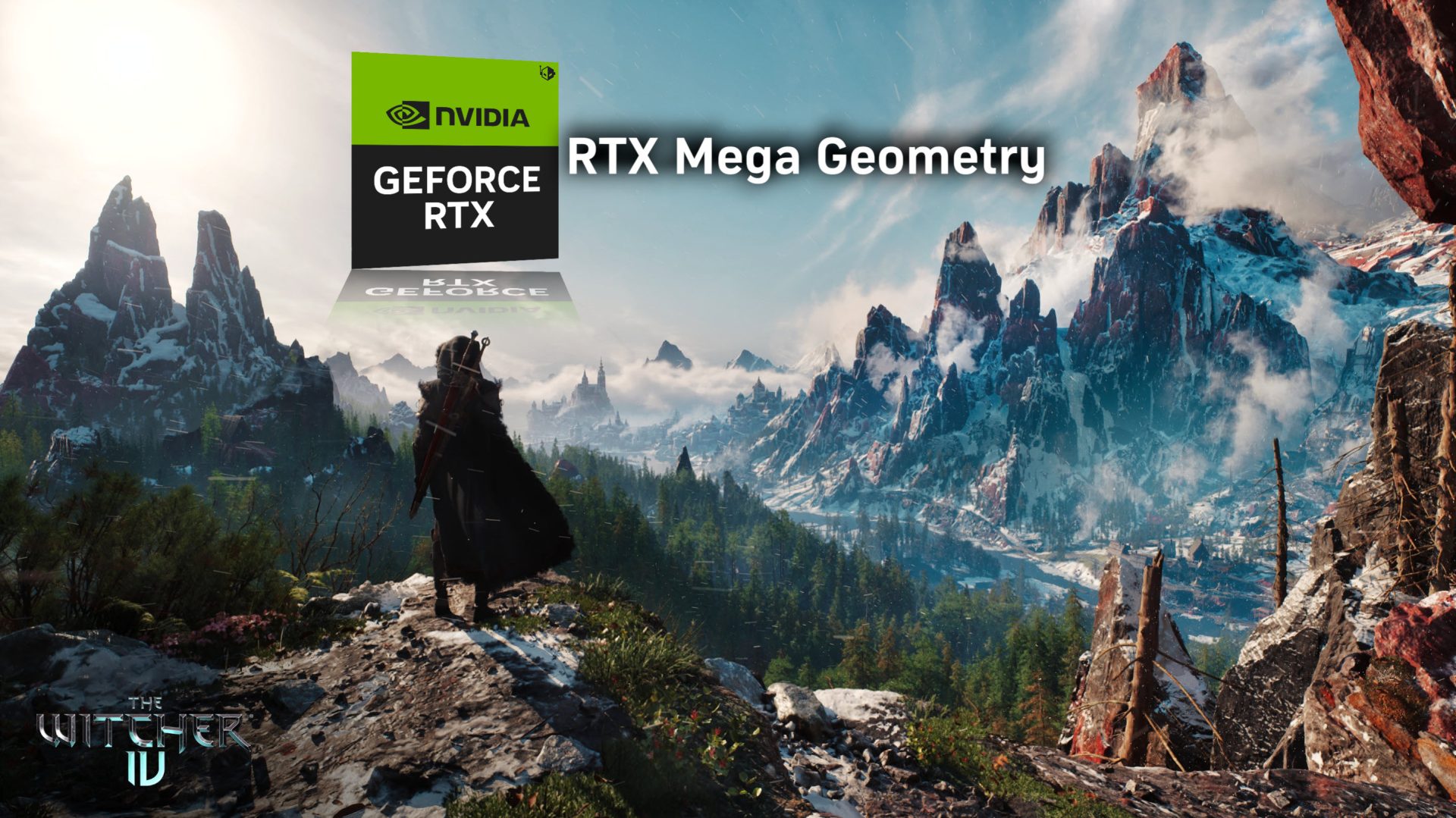
The Witcher 4 will integrate an updated version of NVIDIA's RTX Mega Geometry, promising smoother frame rates and r...

A new lineup of Beelink mini PCs brings OpenClaw pre-installed options, including Lobster Red editions and SSD upgr...

A trusted insider suggests the troubled Star Wars: Knights of the Old Republic remake is taking a more promising di...

A new partnership between Applied Materials and Micron is set to redefine memory efficiency in AI systems, but the...