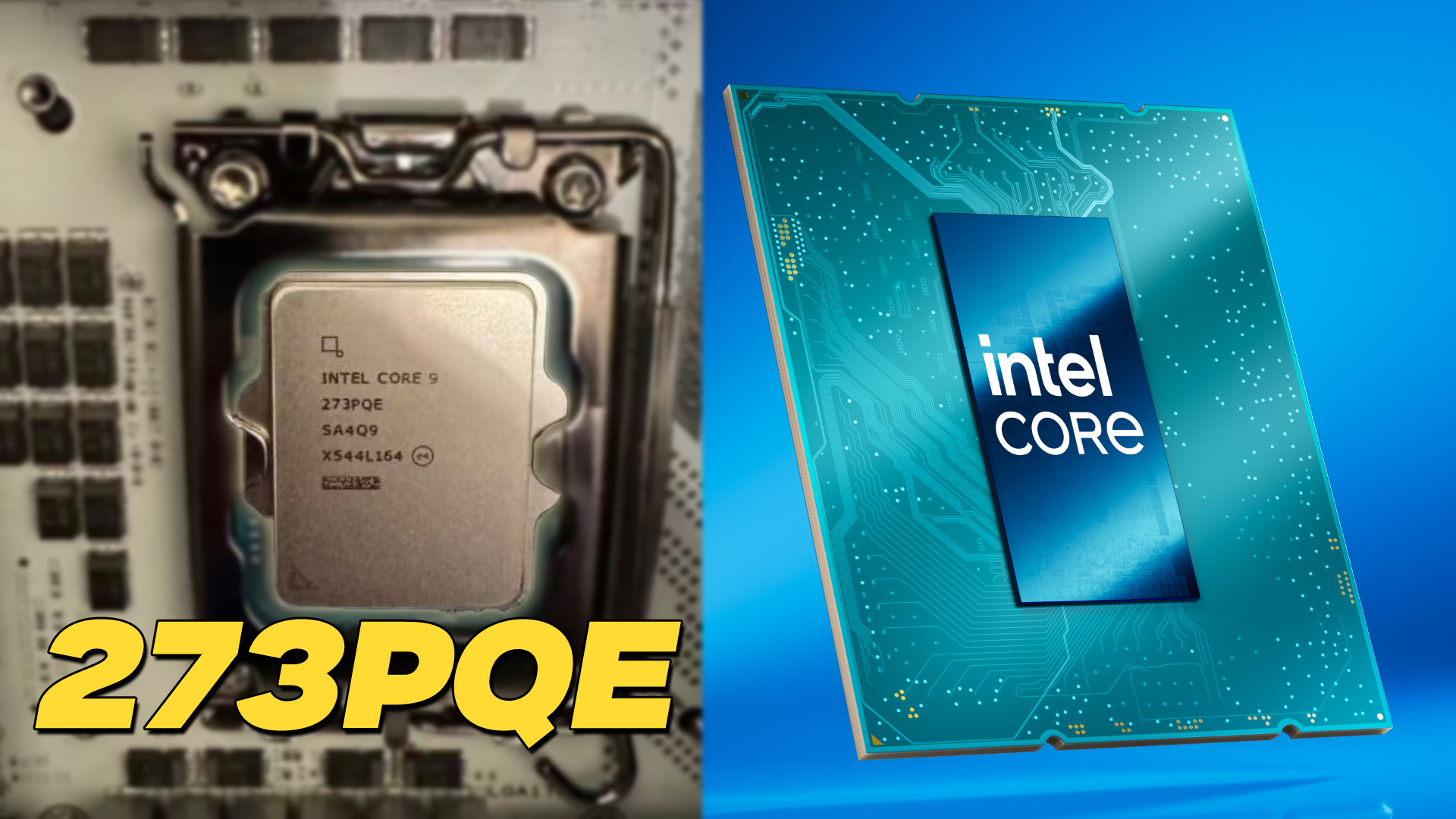
Gigabyte’s new Z890 PLUS series targets enthusiasts seeking a balance of price and performance, offering up to 35% productivity gains over previous generations while introducing Ultra Turbo Mode for one-click B...








A new tool from Intel promises to optimize x86 binaries, but its effectiveness remains unproven. The industry watch...

AMD has issued a firm statement condemning Chuwi's unauthorized rebranding of Ryzen processors, marking a significa...

A new wave of temporary email services is simplifying digital privacy for users without requiring long-term commitm...

The Intel Arc B770 delivers solid performance in 144 MB of VRAM, but its future hinges on Arrow Lake. Here’s what y...

Samsung is offering a slight discount to customers who commit to five-year contracts, aiming to extend the memory b...

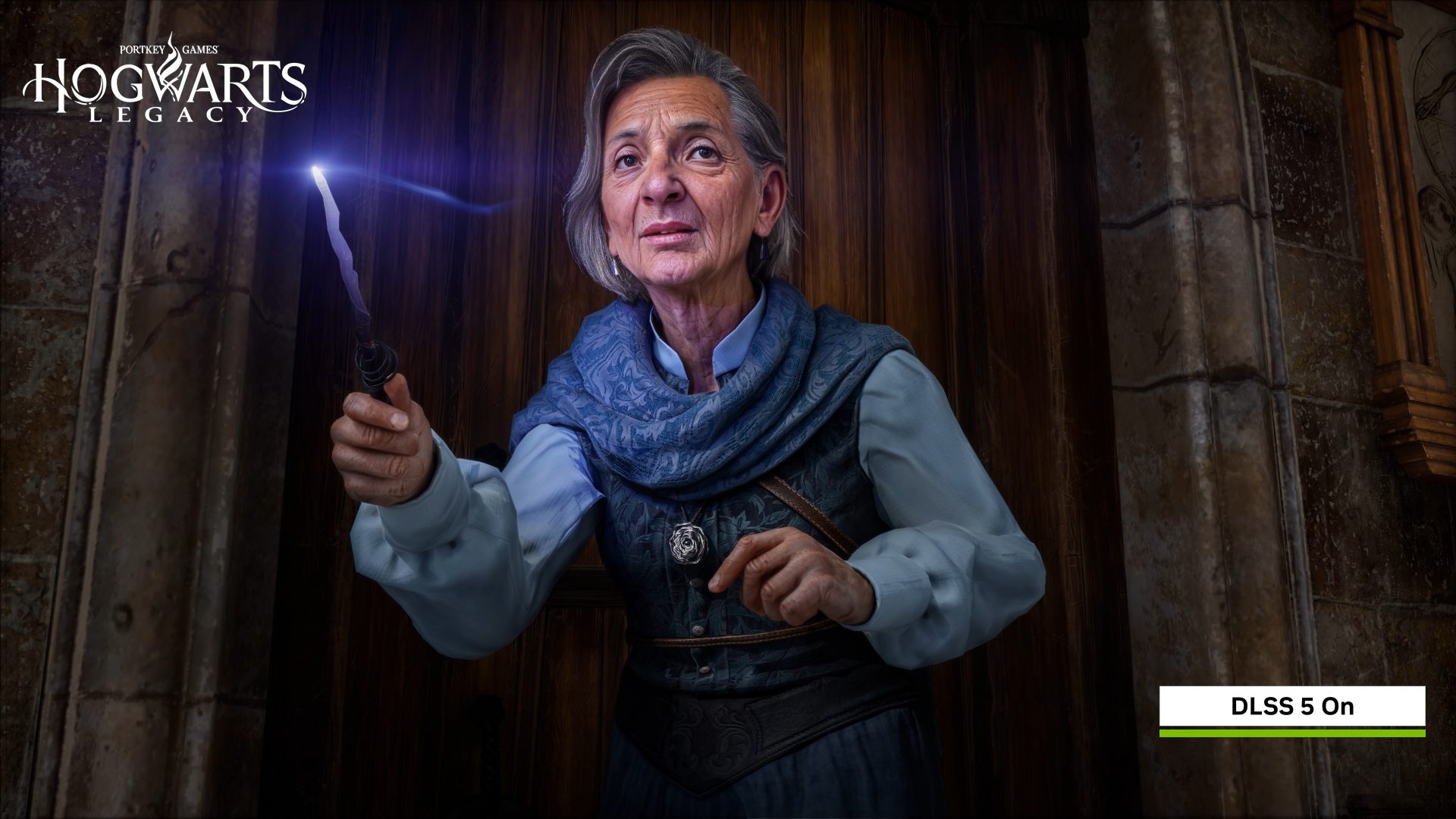
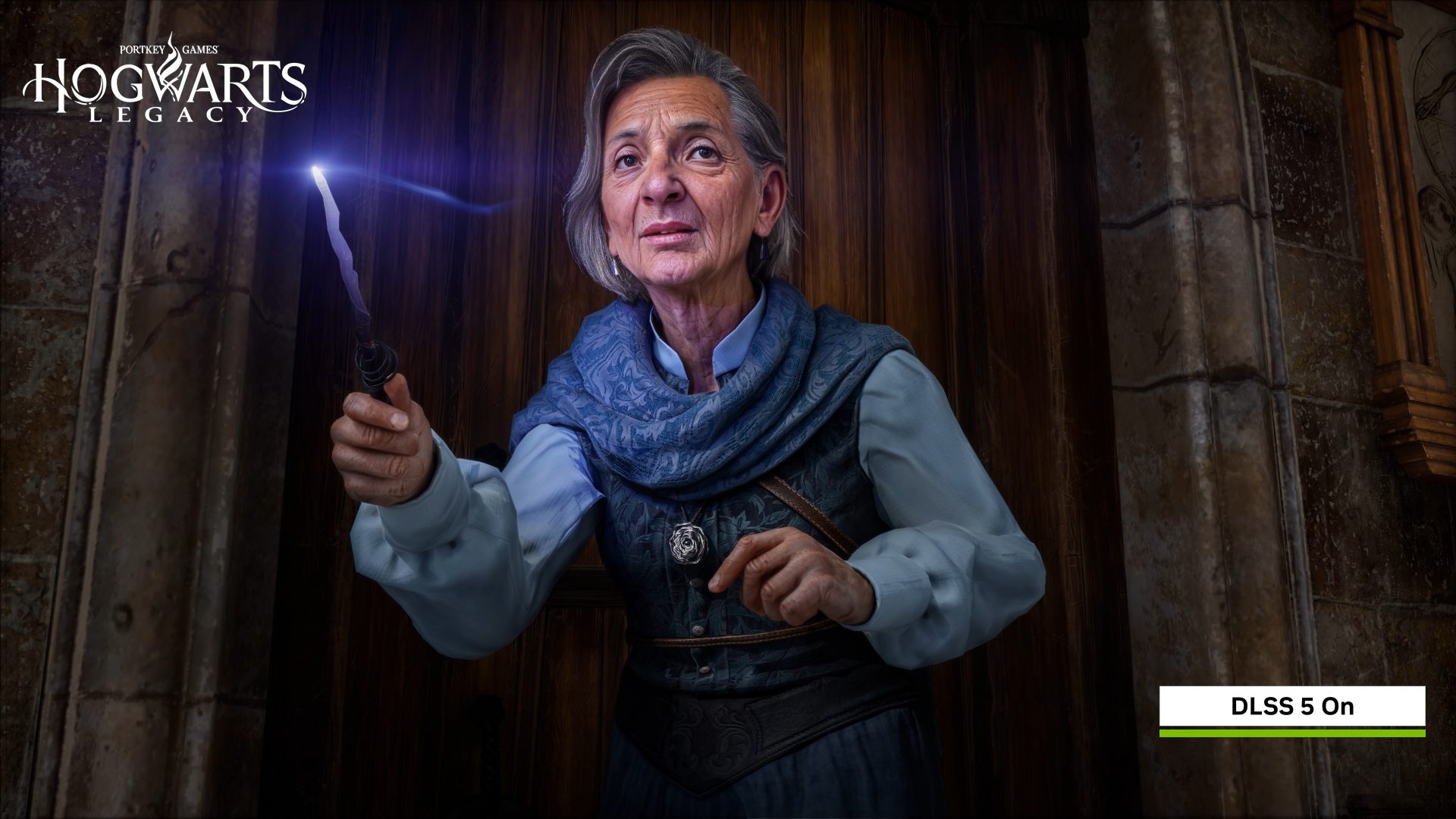
Nvidia’s DLSS 5 abandons traditional FPS scaling in favor of power efficiency, signaling a potential industry shift...

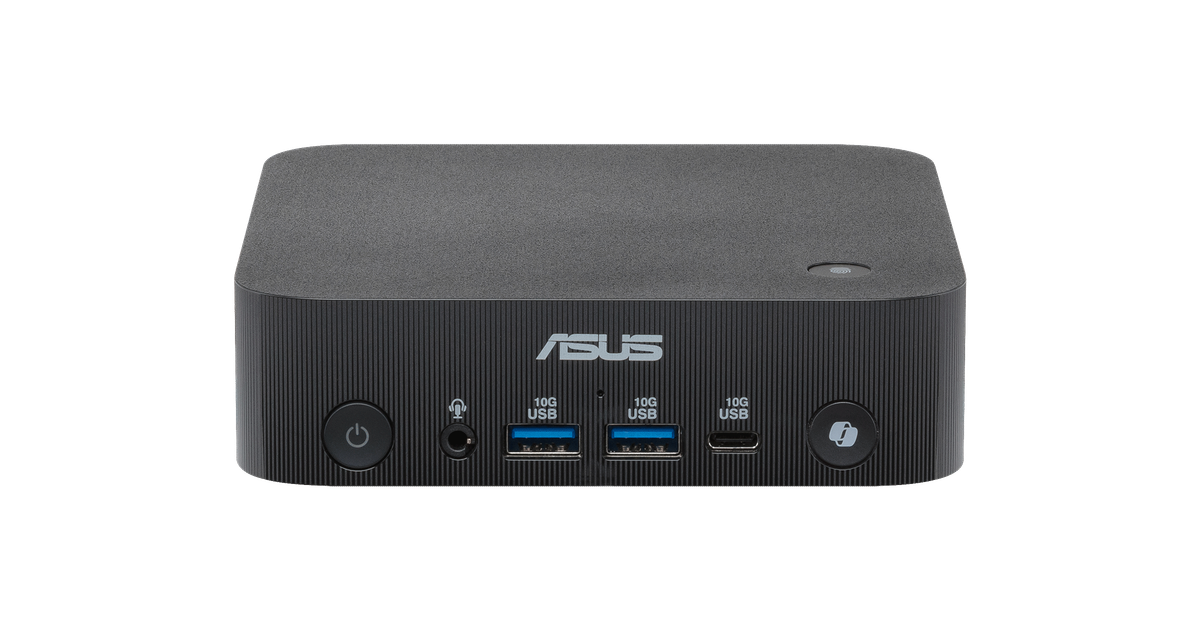
The ASUS AIoT Gateway integrates edge computing, AI inference, and multi-sensor data processing to enable real-time...

NVIDIA's long-standing production hurdles in China appear resolved as the H200 GPU resumes manufacturing. Simultane...
A recent analysis reveals that leading deepfake detection tools often fail to identify manipulated media, highlight...

The Intel Core Ultra 3 205T offers a cost-effective alternative to higher-end processors, delivering strong single-...