A newly discovered Linux vulnerability allows attackers to bypass security checks and gain elevated system access, posing a serious risk to servers and workstations. Experts warn of active exploitation attempts...








Micron’s new GDDR7 chips—capable of 36 Gbps bandwidth—could enable graphics cards with up to 96GB VRAM, but the tec...

After facing intense backlash over its controversial age verification plans, Discord has abandoned its original tim...
The CP152-1 merges rear-accessible drive bays with built-in RAID 1, eliminating cables and simplifying high-density...

A new restaurant sim strips away customer service stress by hiding diners behind shutters—but does that mean gamepl...

A detailed technical breakdown of how Resident Evil Requiem performs across a spectrum of hardware, from portable g...

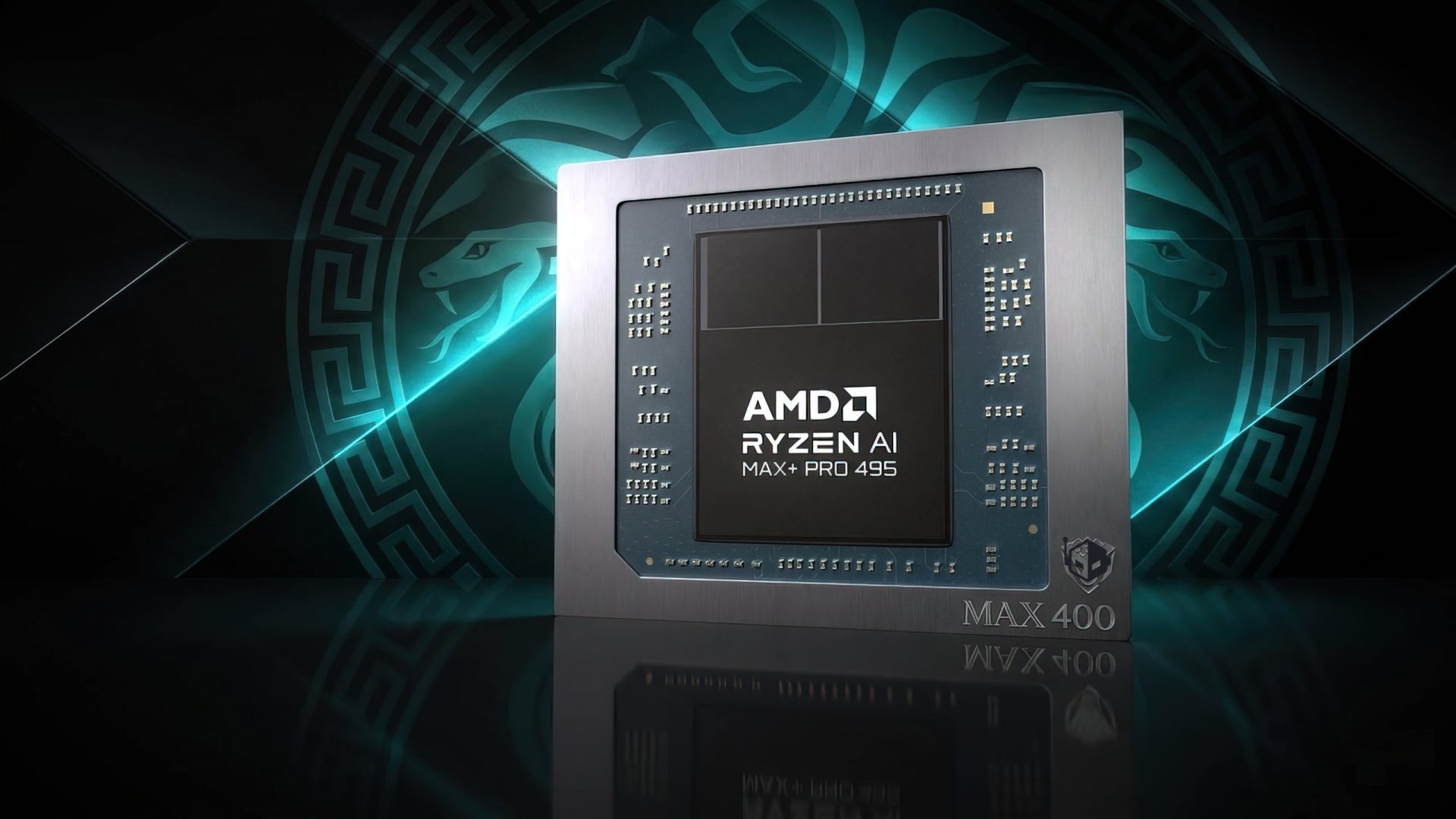
AMD’s new EPYC 8005 series bridges the gap between its high-end EPYC 9005 and lower-tier EPYC 4005 chips, offering...

A single-monitor arm from Huanuo is now just $33.23—26% off—offering an affordable way to eliminate neck strain and...

NVIDIA’s Vera Rubin supercomputer combines six custom chips, HBM4 memory, and a liquid-cooled NVLink 6 spine to del...

The latest iteration of the Bloodborne Remaster Project refines visual fidelity, restores classic art direction, an...

Two new technical roles at Nvidia reveal a surprising focus on Linux gaming—particularly Vulkan and Proton—marking...