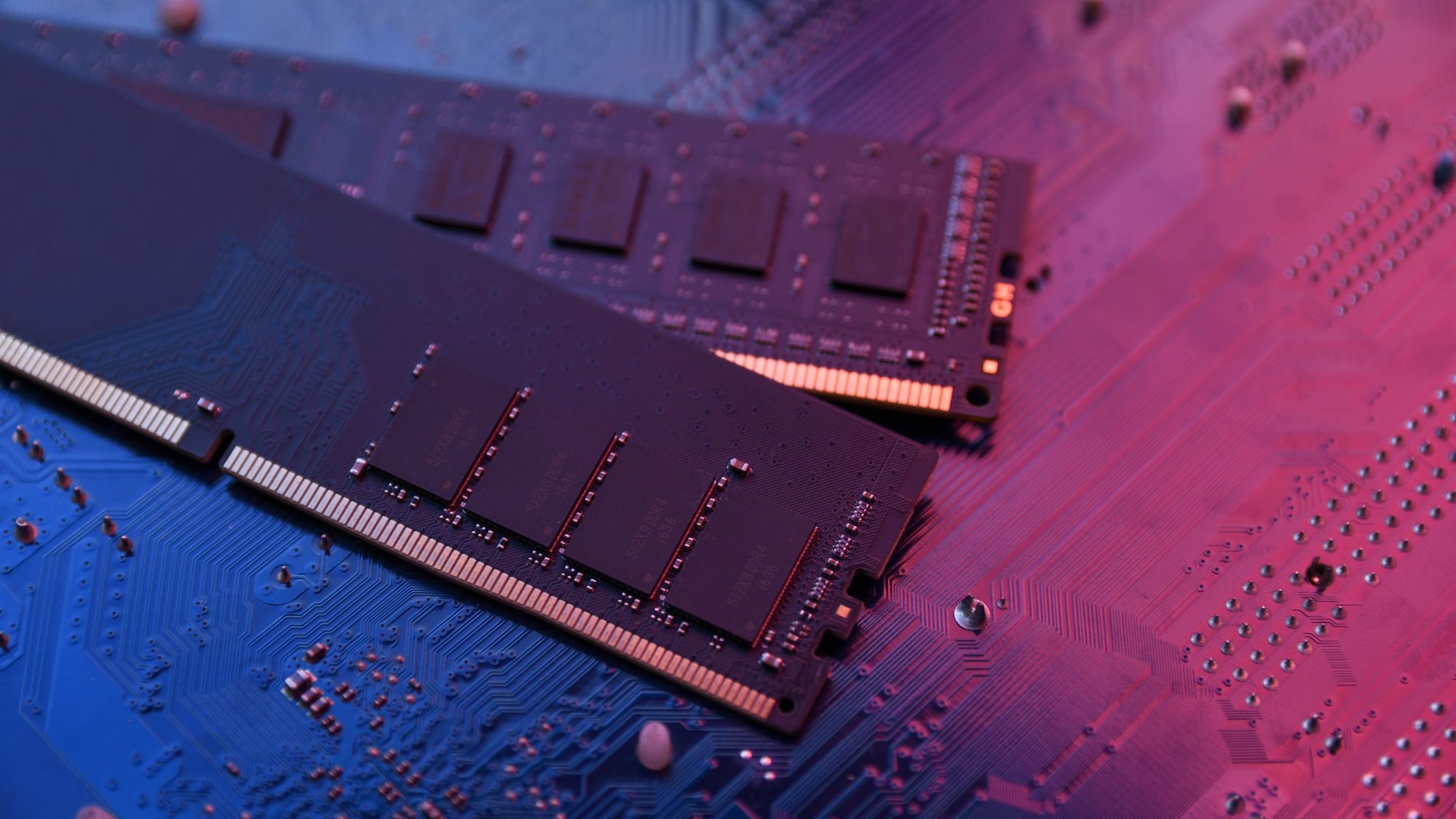
The surge in AI-driven workloads is putting unprecedented pressure on RAM supplies, with industry experts warning of long-term supply shortages and cost instability. Micron's analysis reveals a growing mismatch...









The new Chieftec workstation chassis redefines professional computing with its blend of modern design, robust cooli...

Activision has taken legal steps to halt the activities of a well-known Call of Duty leaker, marking a significant...

A new industrial multimedia PC offers dual 4K display support, fanless operation, and versatile mounting options wh...
ASUS Republic of Gamers (ROG) is celebrating its 20th anniversary with a global campaign that invites fans to share...

A compact, ultra-portable smartphone defies the trend of ever-larger devices, offering a practical alternative for...
A single tool now combines editing, converting, annotating, and securing PDFs for Windows and Mac users at a flat $...

A quiet shift in Sony’s approach to PC ports could reshape the gaming landscape. Industry insiders suggest Valve’s...

A fresh take on D&D mechanics, Esoteric Ebb blends humor and depth in a reactive world where choices ripple through...

A global campaign invites gamers to engage with ASUS ROG’s legacy, offering prizes worth over $20,000 in a blend of...

A new generation of live-service games is crashing, but the lessons from Highguard and others reveal a troubling tr...