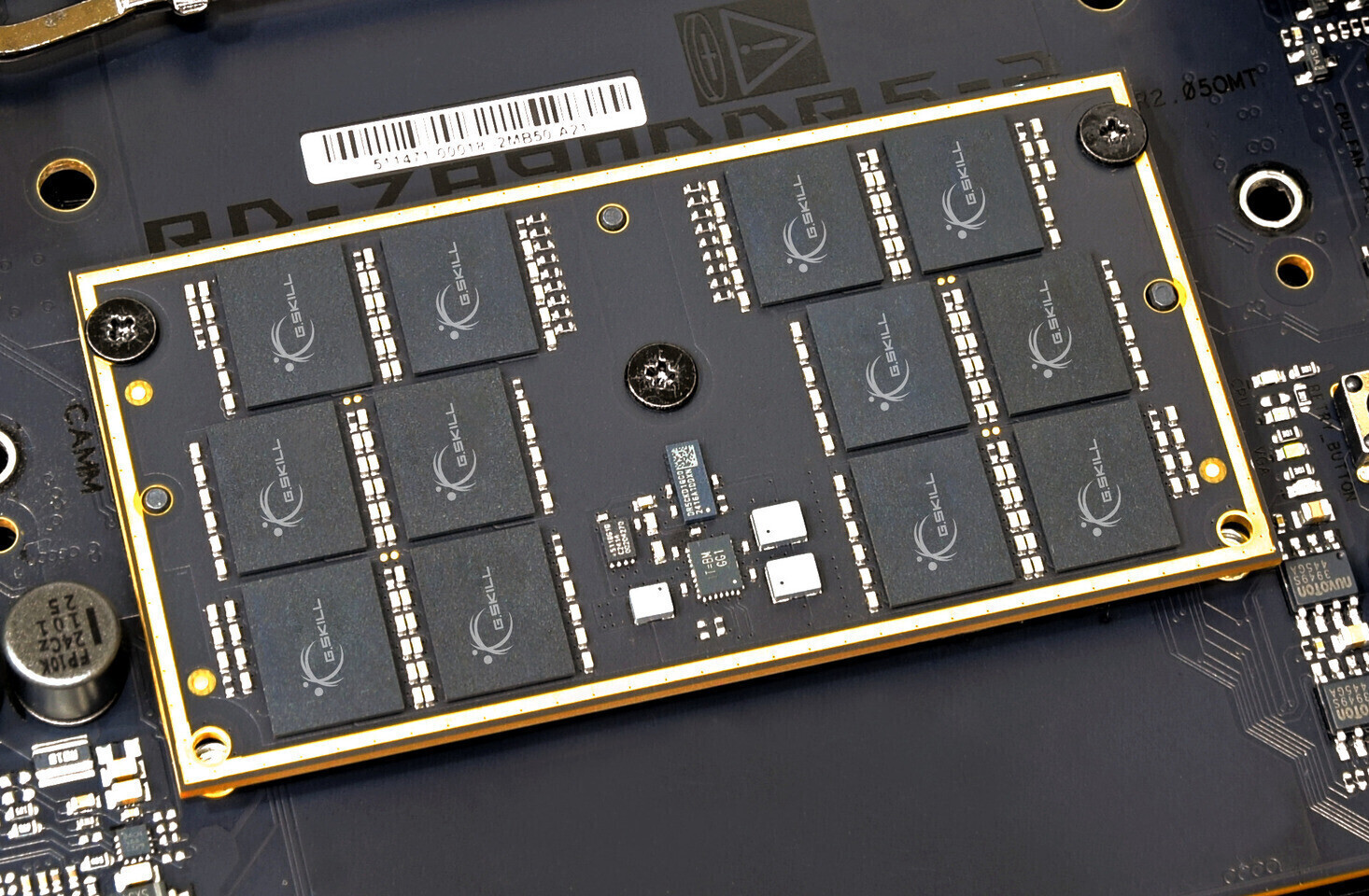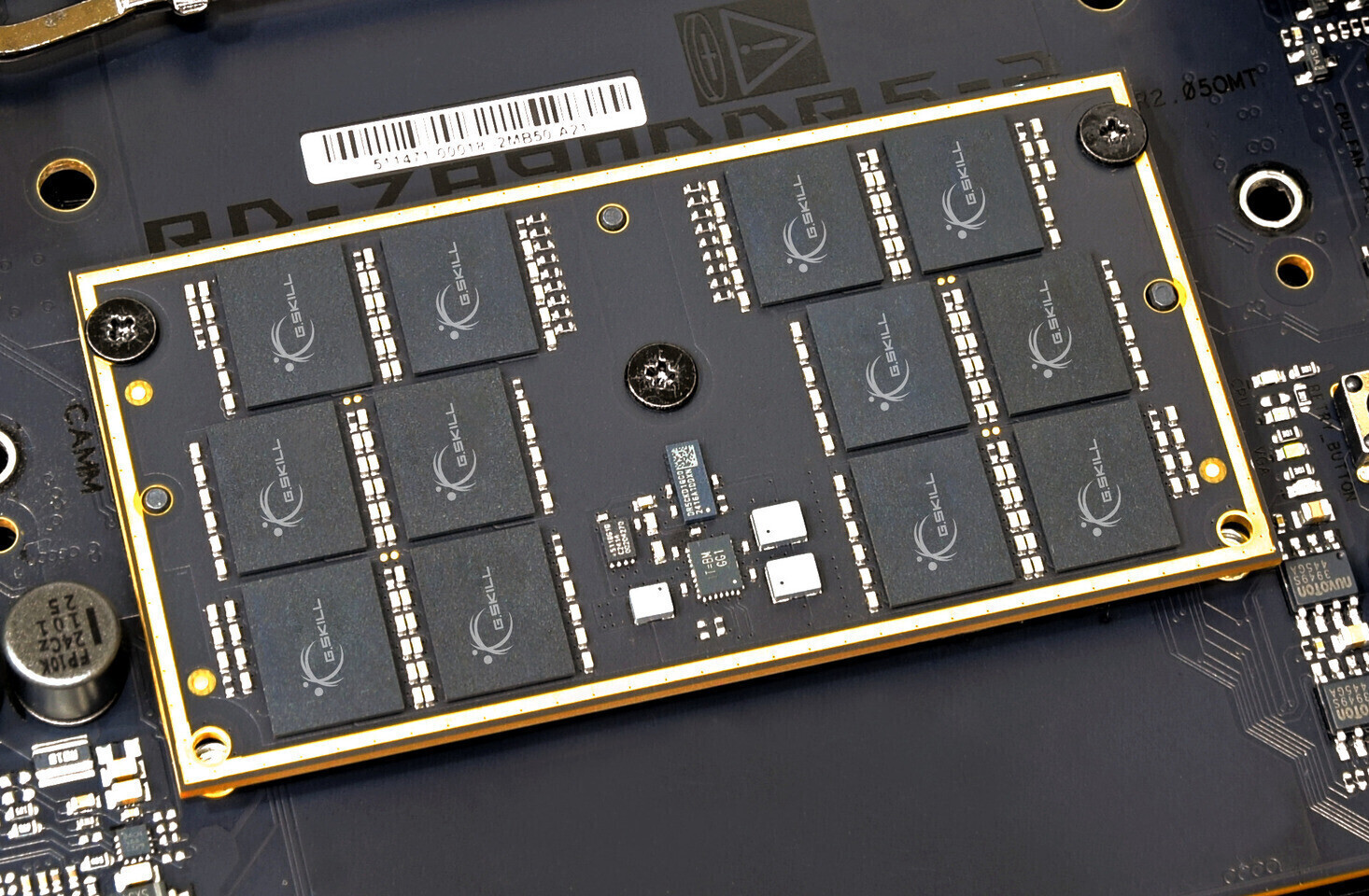
The DDR6 standard is poised to redefine performance benchmarks with speeds up to 17,600 MT/s, but its adoption hinges on overcoming significant engineering challenges. This article explores the tradeoffs behind...






Microsoft has introduced a new image generator that pushes the boundaries of synthetic media, achieving strong perf...

The latest FSR 4.1 update from AMD introduces refined details, smoother camera motion, and improved performance for...

A compact, plug-and-play smart light switch compatible with Matter is now available for $20 for two units, offering...

Intel's upcoming Arc Pro B70 and B65 workstation GPUs are set to launch with significant specifications, including...

The RTX 50 series delivers significant performance-per-watt improvements, but its efficiency gains introduce new ch...

The new Intel Core Ultra 5 250KF Plus CPU delivers a notable 25% performance boost over its predecessor, positionin...

A $1,000 pre-built desktop combines an eight-core Ryzen 9 8000X3D CPU with an RTX 5070 GPU, delivering strong perfo...

Crimson Desert has shattered expectations with over 2 million copies sold in its first day, establishing a new benc...
Acer's latest OLED gaming monitors deliver high refresh rates, low input lag, and competitive pricing. Experts weig...

A developing solution aims to resolve the blurry graphics issue affecting PlayStation 5 players in Crimson Desert,...