Rockstar Games is adopting a console-first strategy for its next-generation titles, including the highly anticipated GTA 6. This shift reflects broader industry trends where hardware optimization and platform e...





Apple has unveiled the Mac Studio, a high-performance desktop designed to replace the discontinued Mac Pro tower. T...

The M.A.P.P. mouse, a relic from 2002 with roots in Ghost in the Shell lore, is back as a limited-edition model, bl...

Four WOLFBOX portable air blowers are now discounted up to 40 percent on Amazon, including the MF200 which offers a...
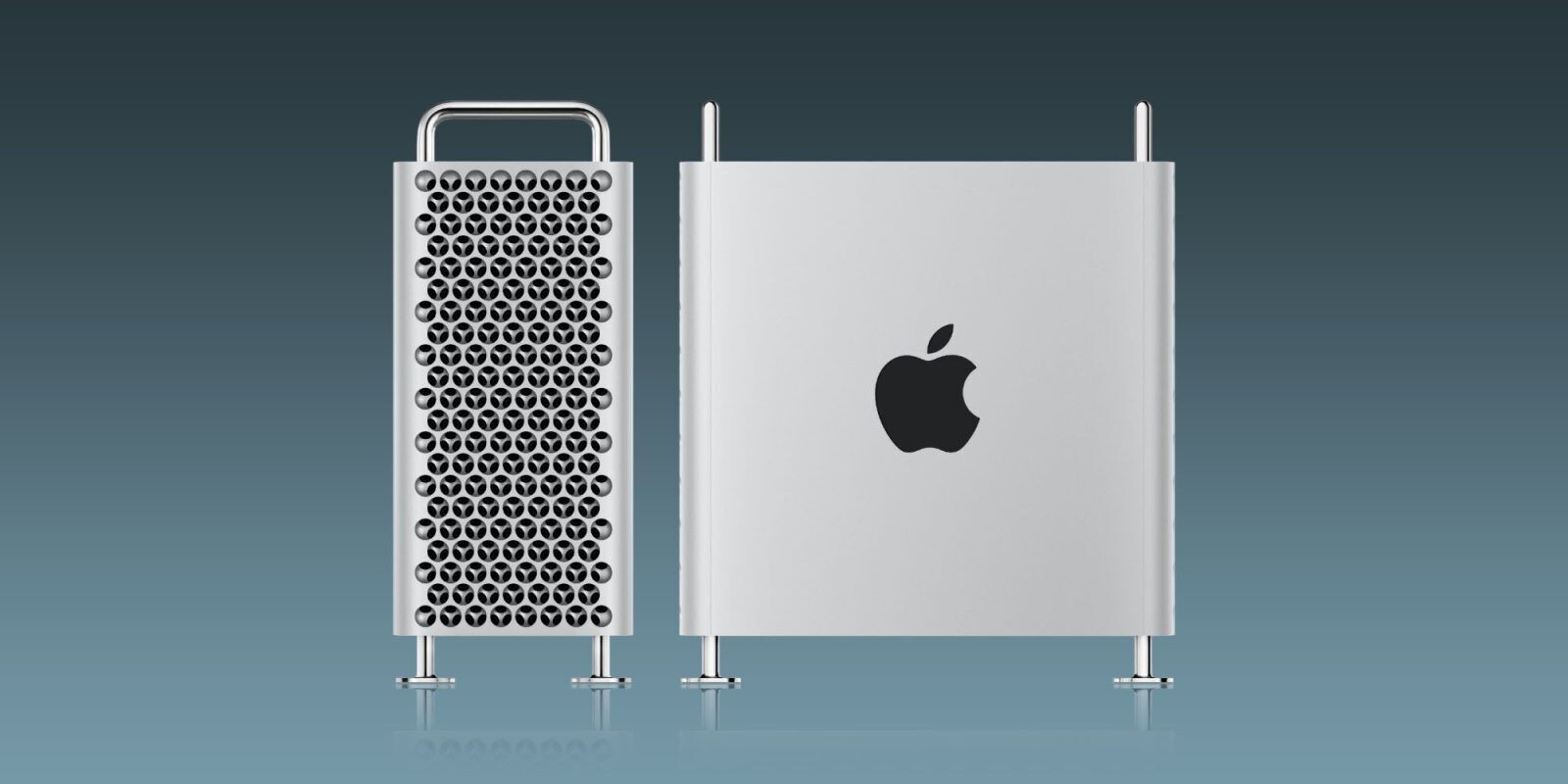
Apple’s Mac Studio now offers 256 GB of unified memory, a figure that challenges traditional workstation designs. T...
The long-awaited sequel to Hades arrives on Xbox Series X|S and PlayStation 5, delivering a performance-driven over...

Netflix has increased its subscription costs yet again, but the impact on small businesses—and whether they can aff...

Apple's iPhone Fold is reportedly not launching alongside the iPhone 18 Pro Duo, signaling a potential shift in the...

The latest iteration of Intel's Core Ultra series, the 200S Plus line, brings significant performance gains and eff...
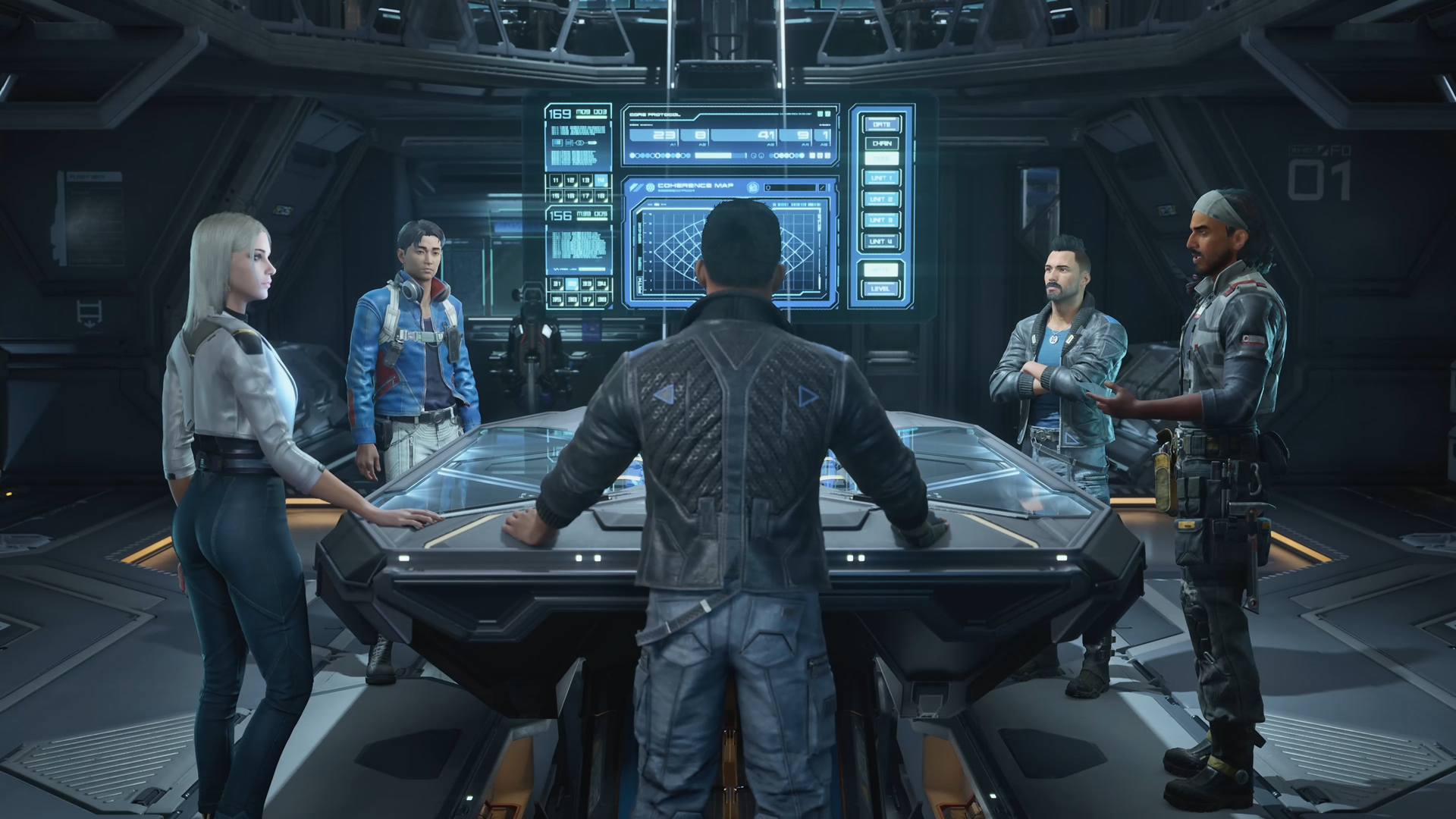
Owlcat Studios reveals it uses generative AI to speed up the final version of The Expanse: Osiris Reborn, but insis...

iOS 27 is set to introduce a multi-agent Siri system, blending multiple AI personas for complex tasks. This shift c...