Rockstar Games is adopting a console-first strategy for its next-generation titles, including the highly anticipated GTA 6. This shift reflects broader industry trends where hardware optimization and platform e...





New data reveals a stark contrast between two long-running extraction shooter games, with ARC Raiders pulling in fi...

A leaked report suggests Xbox's Project Helix could deliver performance akin to a high-end gaming desktop, potentia...
A newly granted patent reveals OpenAI's approach to pushing the boundaries of AI hardware, using a radical architec...

Microsoft is reconsidering Xbox Game Pass's subscription structure, potentially moving away from a fixed tier model...

A new suite of AI-powered tools from Google Cloud is poised to revolutionize game development, promising faster ite...

Bolt Graphics has completed the tape-out of its test chip for the Zeus GPU, signaling a major step toward redefinin...
A new software suite challenges Adobe's dominance in PDF editing with lower prices, faster performance, and a strea...

A new low price for a 15.6-inch IPS portable monitor reflects broader trends in display availability and performanc...

Two new MSI gaming laptops pack Intel’s Core Ultra 200HX and an RTX 5090 into a compact chassis, pushing power effi...
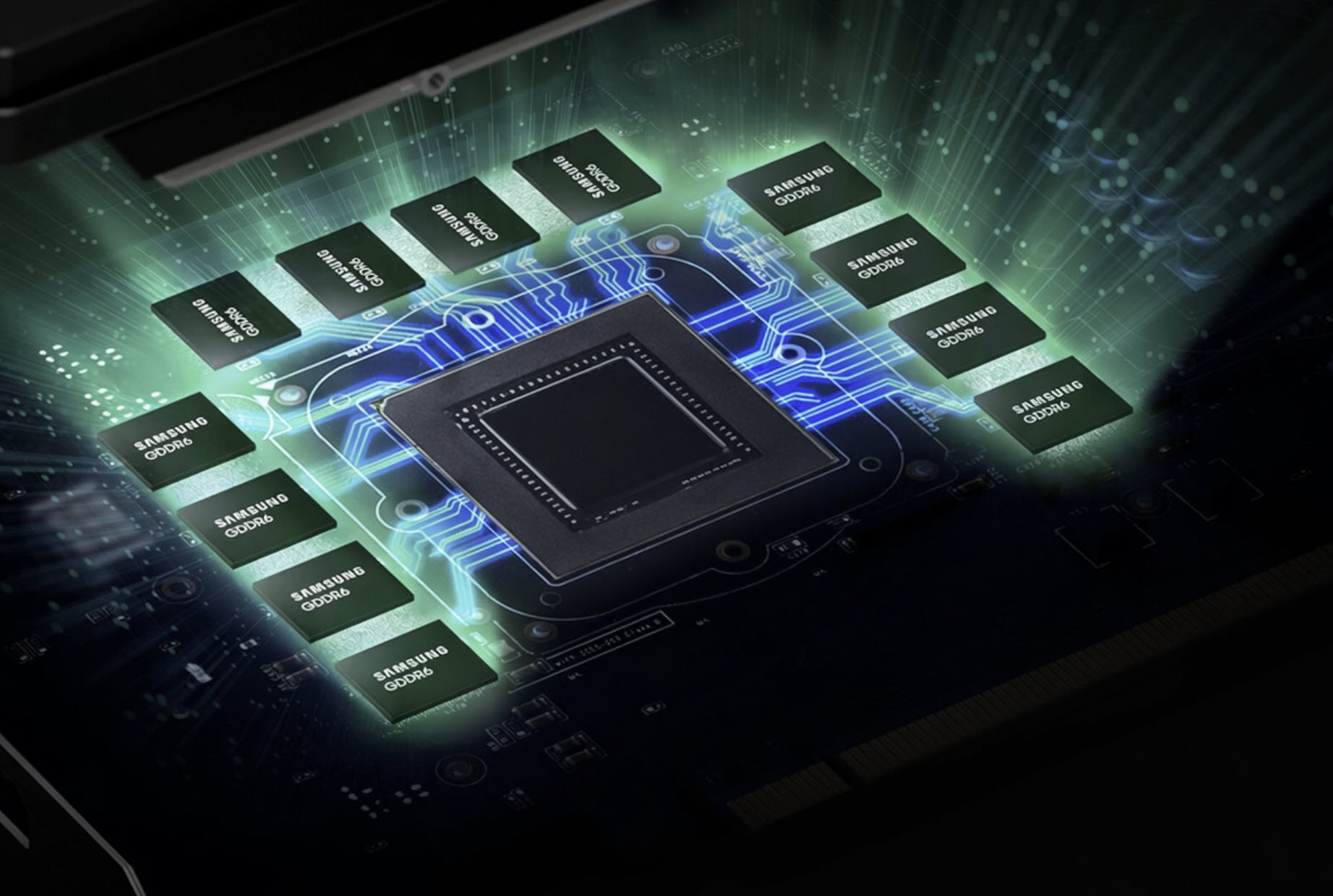
A looming shortage of GDDR6 memory could disrupt Sony's PlayStation 5 and gaming GPUs, raising concerns about suppl...