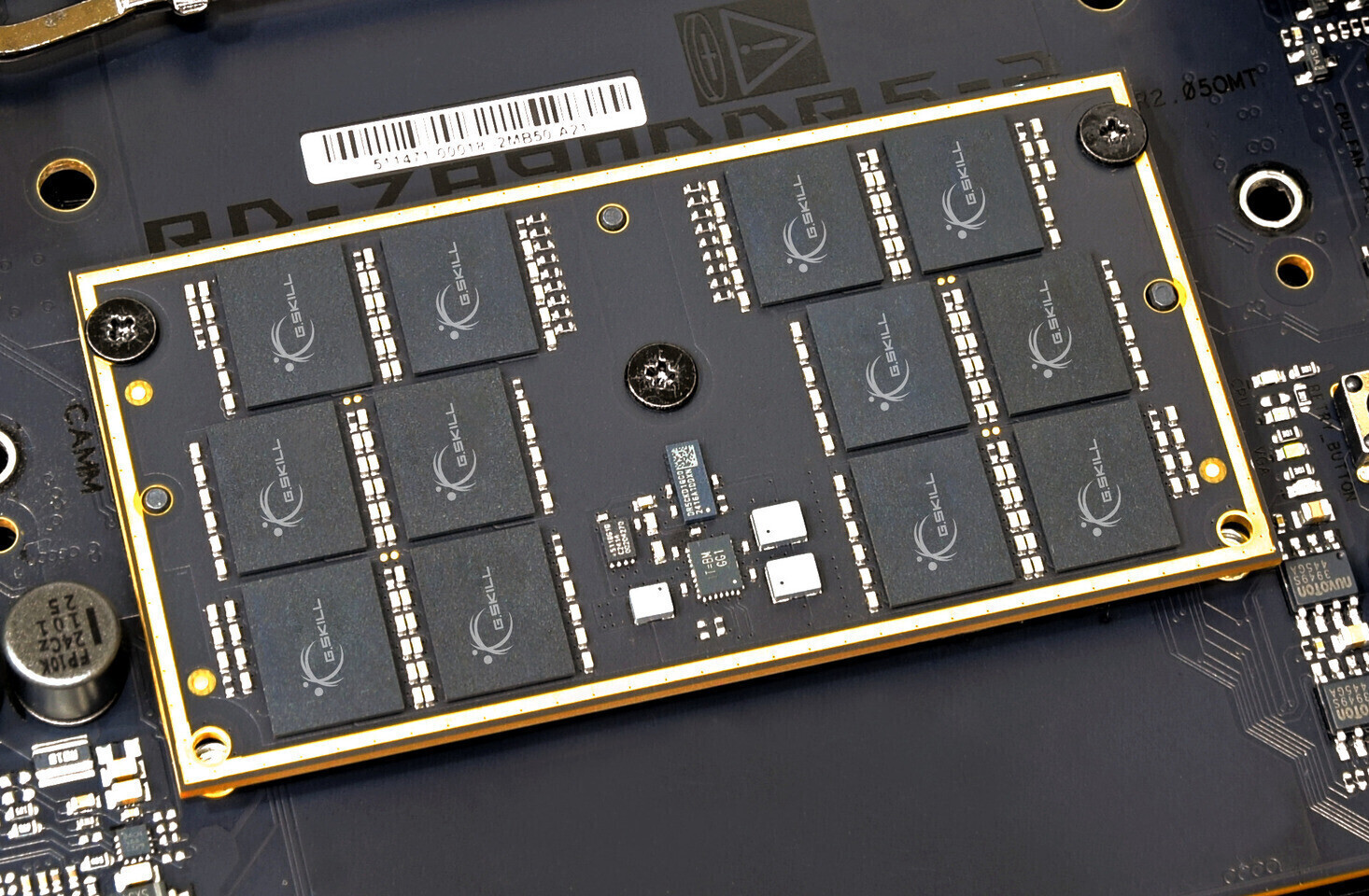
The DDR6 standard is poised to redefine performance benchmarks with speeds up to 17,600 MT/s, but its adoption hinges on overcoming significant engineering challenges. This article explores the tradeoffs behind...










Rebellion delivers the long-awaited return of *Speedball*, a hyper-violent future sport with deep customization, ch...
A new $6 million-funded company is deploying AI-powered formal verification to catch bugs in AI-generated code befo...

Kioxia’s latest UFS 4.1 devices leverage 8th-gen BiCS FLASH with QLC NAND, delivering **25% faster sequential write...

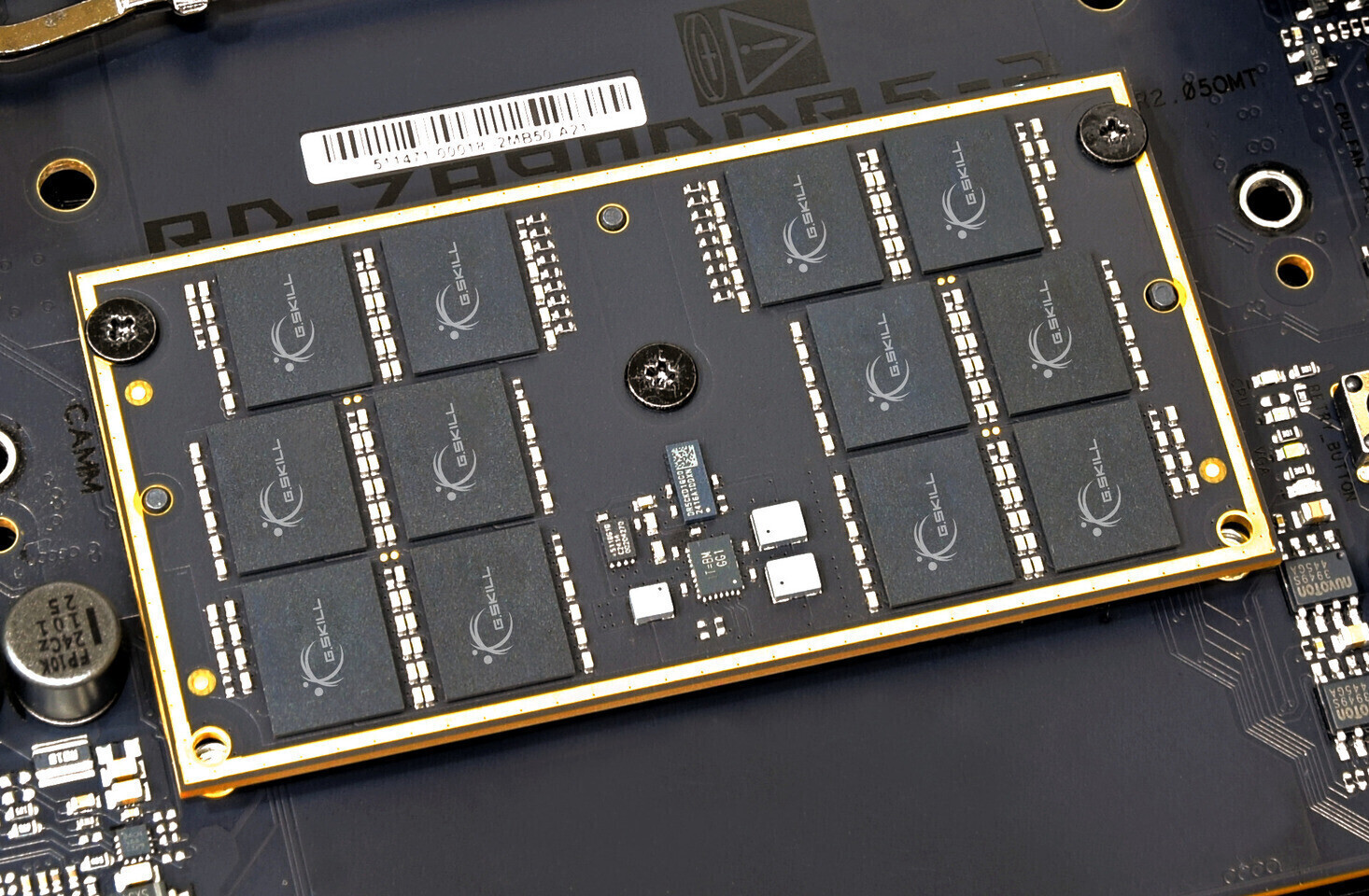
A new partnership between AMD, V-Color, and Cooler Master signals a shift in how high-end PCs are assembled—with pr...

The upcoming demo for *Vampire Crawlers* redefines turn-based combat with a ‘stack-and-execute’ system, letting pla...

From deepfake scams to malware hidden in open-

Early real-world tests show AMD’s latest Ryzen 9850X3D delivering modest frame-rate improvements—up to 6% in *Count...

NVIDIA’s RTX Remix Logic arrives as a game-changer for modders, enabling dynamic effects in classic titles—no

Mozilla has launched a paid initiative to develop open-

The OLED monitor revolution has arrived, with shipments surging **65% in 2025** and projections hitting **15 millio...