A new high availability architecture combines Scality's storage expertise with Veeam's backup solutions, promising enterprise-grade resilience without the complexity. IT teams must weigh performance claims agai...








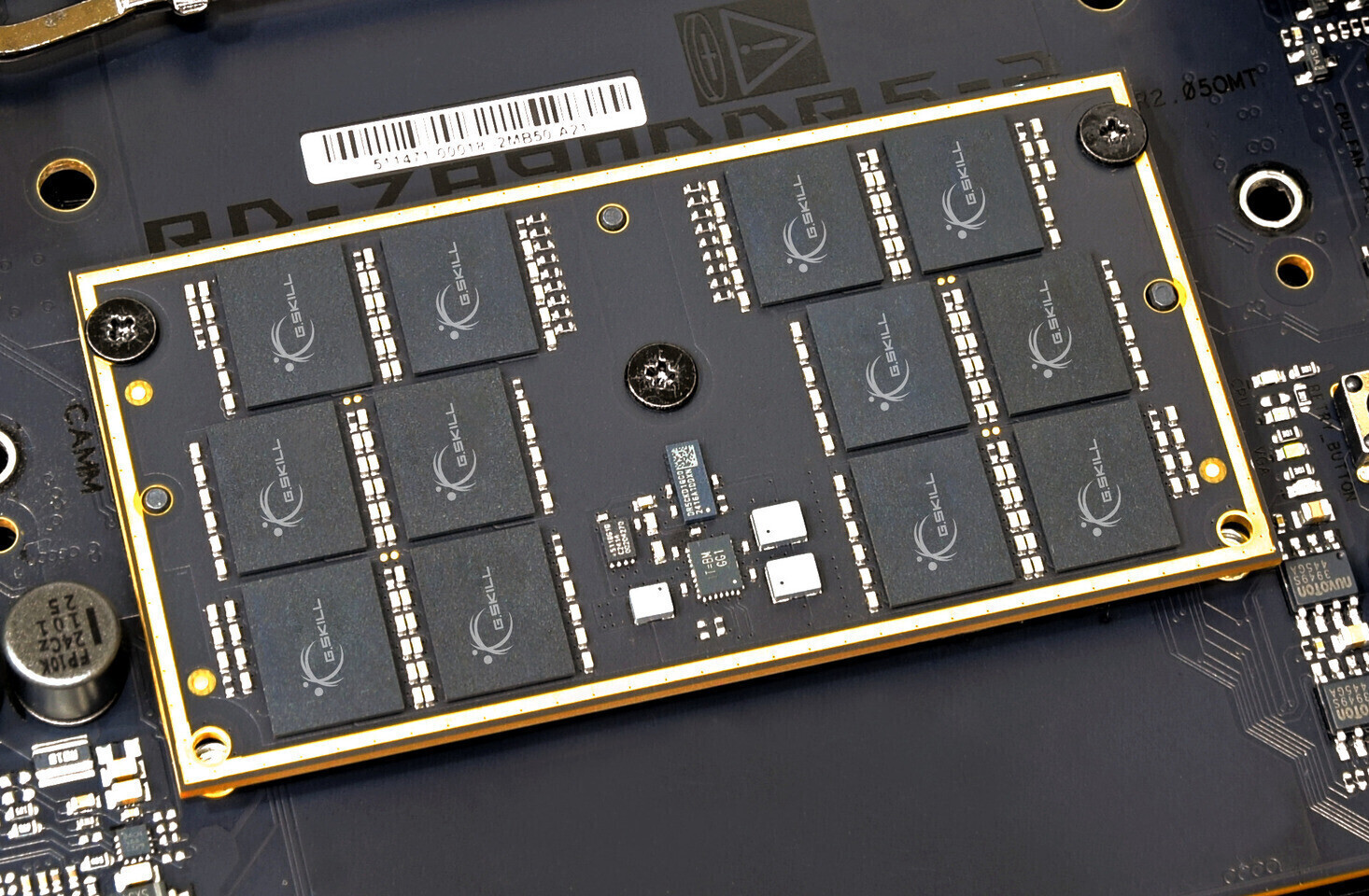
A newly installed MSI GeForce RTX 5090 Trio erupted in flames seconds after a user powered on their system, damagin...

After two decades of neglect, *Serious Sam 2* has received its most substantial refresh yet—introducing Steam achie...

The latest Cult of the Lamb* expansion, Woolhaven*, delivers a final boss who rejects indoctrination entirely. Deve...

The Desert in *Mewgenics* is a gauntlet of exhaustion and attrition, where a single debuff can turn fights into unw...

Intel’s next-gen Core Ultra 4 series, codenamed Nova Lake, will feature a tile-based architecture with 2nm CPU core...
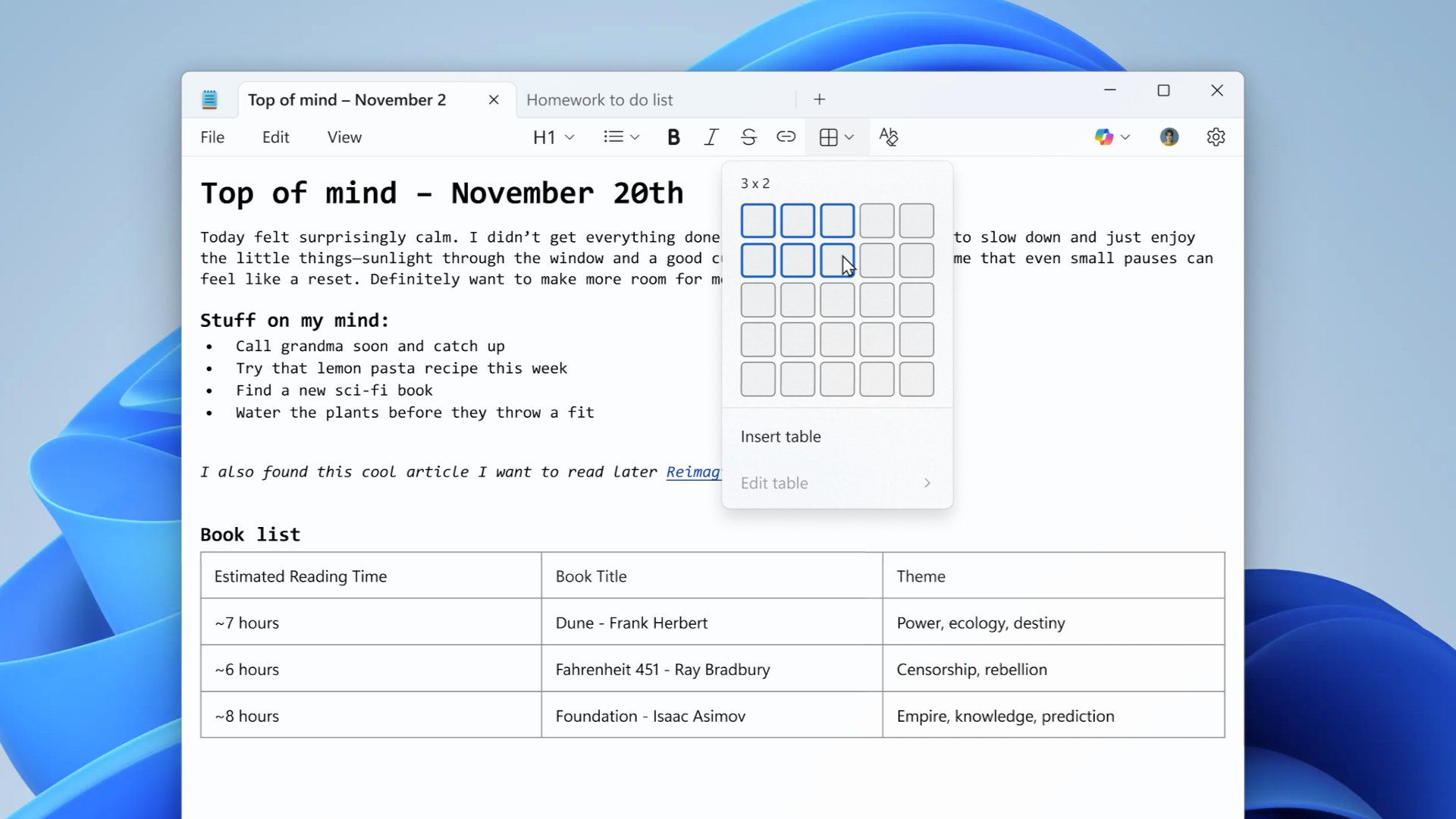
Microsoft’s push to modernize Notepad with formatting, tables, and Markdown support has inadvertently exposed users...

Rising component costs and TSMC’s 2nm manufacturing expenses may force Xiaomi to exclude Qualcomm’s most powerful c...

BenQ’s latest MA Series flagship monitors—MA270S and MA320UG—merge Mac-tuned color accuracy, 120 Hz fluidity, and T...

Blizzard’s latest weapon variant, Crimson Wolf, is now available—but unlocking it requires navigating a system of c...

Marvel’s Wolverine, one of PlayStation’s most anticipated releases, will not take center stage at Sony’s February S...