The Steam Controller, a device designed to bridge the gap between gaming and productivity, vanished almost instantly after its announcement. For creators who rely on dual-function hardware, this raises question...









The Exynos 2700, built on Samsung’s second-gen 2nm SF2P process, is poised to deliver a financial boost to the comp...

The Competition Commission of India has imposed a record penalty on Intel for enforcing a discriminatory warranty p...

The latest Genshin Impact update introduces Varka, a long-awaited Anemo character, alongside a fresh batch of lives...

Konami’s Metal Gear Solid Master Collection Vol. 1* has received its last major update, introducing 4K support for...

Embark Studios’ *Arc Raiders* has caught the attention of neurology researchers, with its chaotic multiplayer dynam...

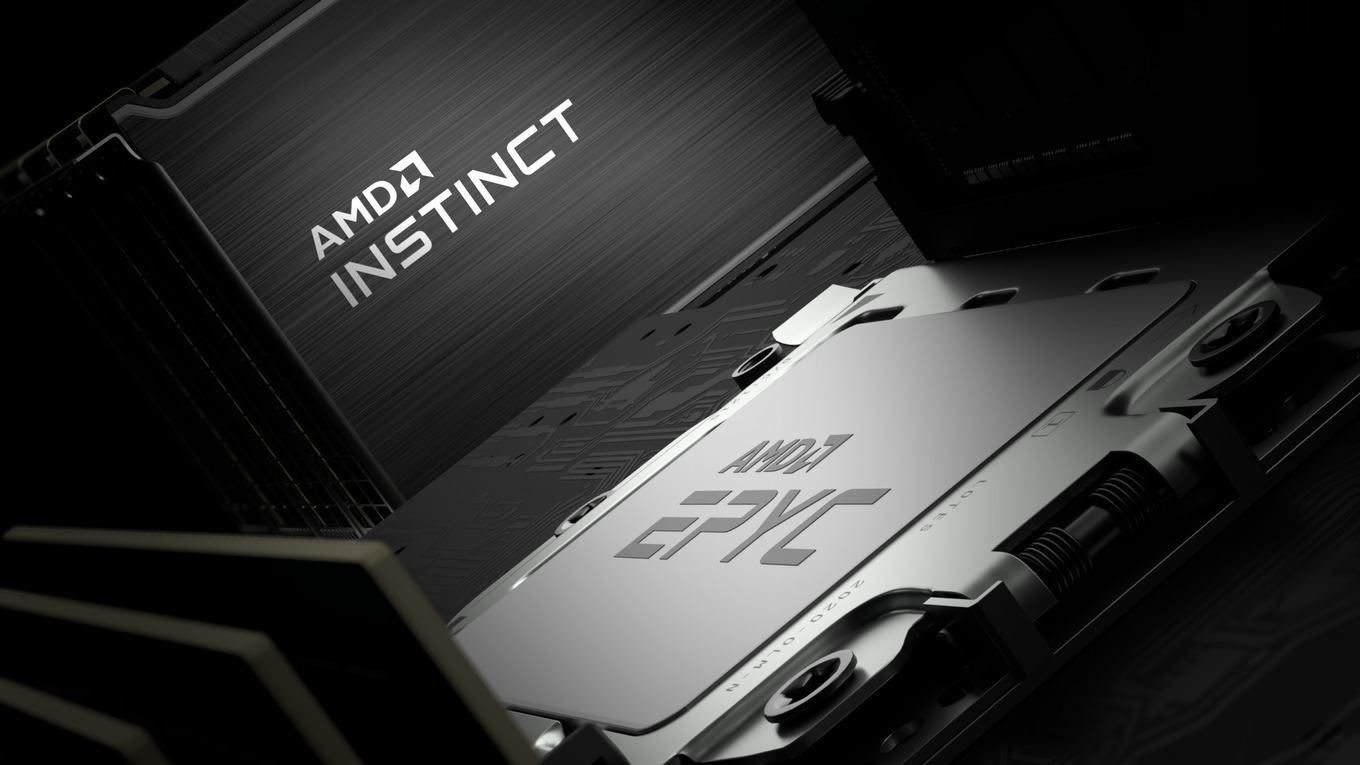
AMD’s x86 CPU market share rose nearly 10% year-over-year in late 2025, but Intel maintains a commanding lead in de...
A two-decade-old rebate program from Microsoft is now more flexible than ever, offering real cash back on purchases...
Intel’s upcoming Nova Lake-S desktop processors are breaking power conventions with a 150W PL1, 496W PL2, and 854W...

KRAFTON Montréal has revealed Project Windless, an ambitious open-world action RPG set 1,500 years before *The Bird...

A professional Valorant player has set a new Guinness World Record using the Logitech G Pro X2 Superstrike, achievi...