A newly discovered Linux vulnerability allows attackers to bypass security checks and gain elevated system access, posing a serious risk to servers and workstations. Experts warn of active exploitation attempts...



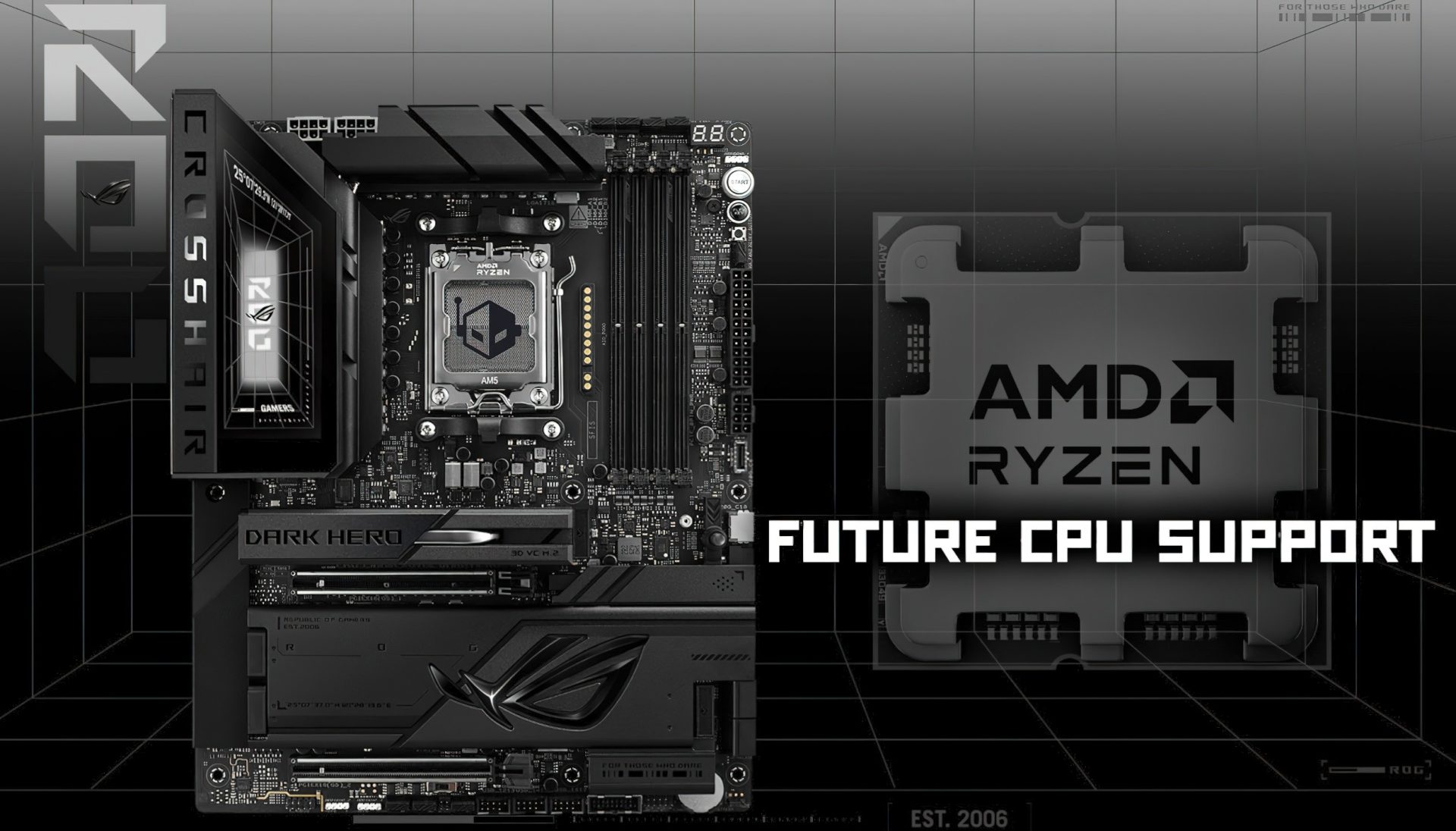
A new beta BIOS update for ASUS X870 motherboards introduces support for a future AMD Ryzen CPU, potentially unlock...

The RTX 5090 and RX 5000 series GPUs represent two distinct approaches to high-end graphics. While the RTX 5090 pus...

A new low-profile mechanical keyboard delivers a near-full-size layout, including a number pad, in just 23 mm of he...

The 2026 BLAST Premier season will see ASUS Republic of Gamers (ROG) deliver a suite of high-performance hardware,...
The MacBook Neo’s base storage performance trails other Apple notebooks by a wide margin, with read and write speed...

A new mini-desktop pairing combines Intel's Arc A380 GPU with a 65W CPU, delivering 1080p gaming at sub-$600 prices...

A mockup at Embedded World 2026 reveals Intel's Nova Lake S CPUs will support DDR5-8000 out of the box, a significa...

ASUS acknowledges the disruption caused by Apple's $599 MacBook Neo, calling it a 'content consumption' device due...

A landmark lawsuit accuses Sony of exploiting its market dominance through the PlayStation Store, seeking restituti...

Two new speakers from Sonos aim to strengthen its ecosystem, offering portable sound and easy expansion without sac...