Gigabyte’s new Z890 PLUS series targets enthusiasts seeking a balance of price and performance, offering up to 35% productivity gains over previous generations while introducing Ultra Turbo Mode for one-click B...







The upcoming Forza Horizon 6 introduces a transformative musical experience, blending exclusive collaborations from...
AMD is seeing an 80% year-over-year increase in server CPU revenue, a sharp rise that highlights how AI is driving...

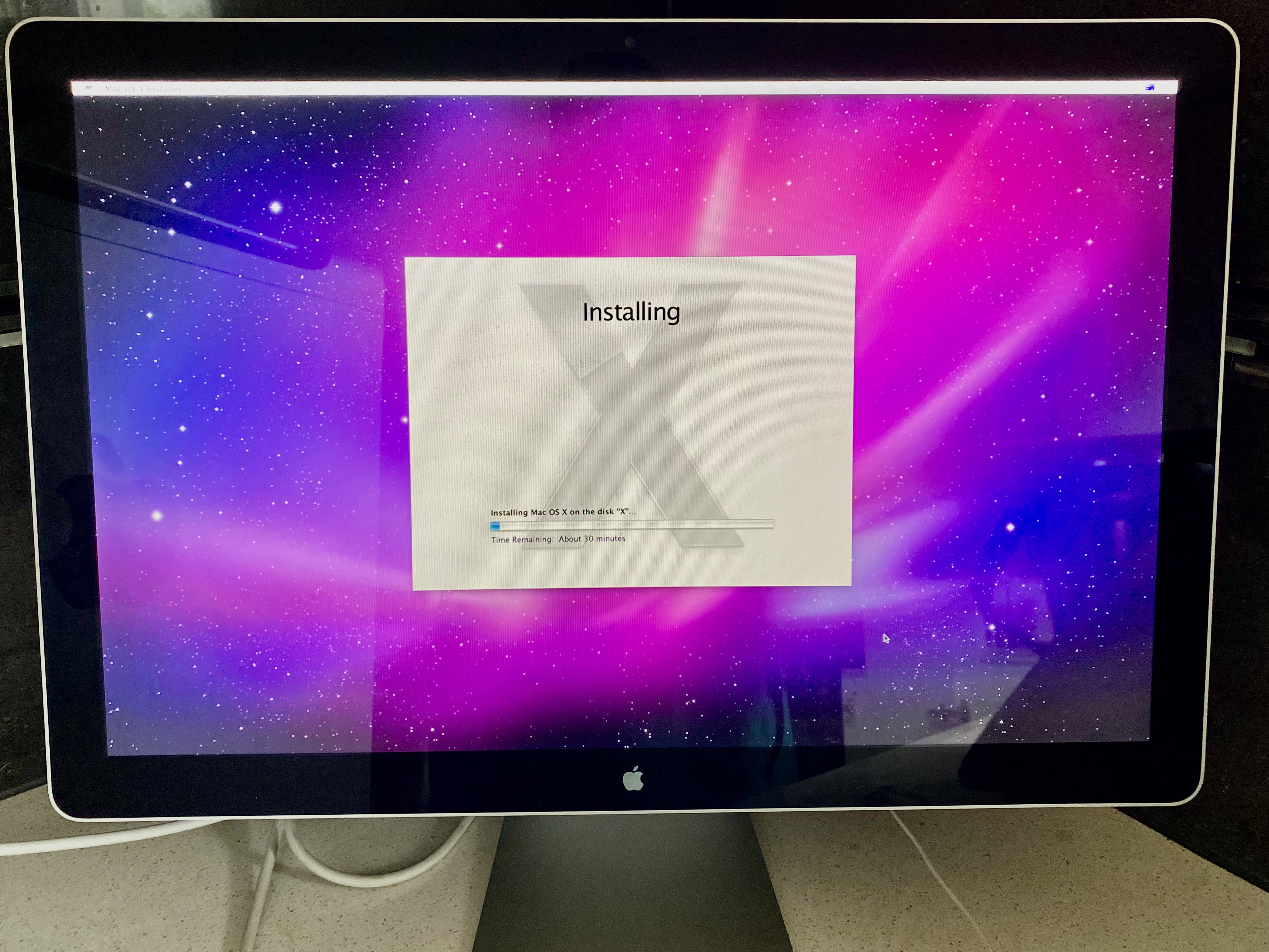
A newly discovered Linux vulnerability allows attackers to bypass security checks and gain elevated system access,...
Bungie's upcoming multi-year story update for Marathon signals a strategic bet on long-term investment in niche fra...

NVIDIA's new Feynman architecture introduces a radical approach to GPU power management, integrating up to 17 times...

The mobile DRAM market is set for a dramatic price increase, with LPDDR5x prices expected to rise by nearly 100% qu...
A new AI companion, Codex, blends playful behavior and real-time learning to create an engaging user experience. It...

Intel appoints two key leaders to steer its client computing and physical AI initiatives, signaling a strategic piv...

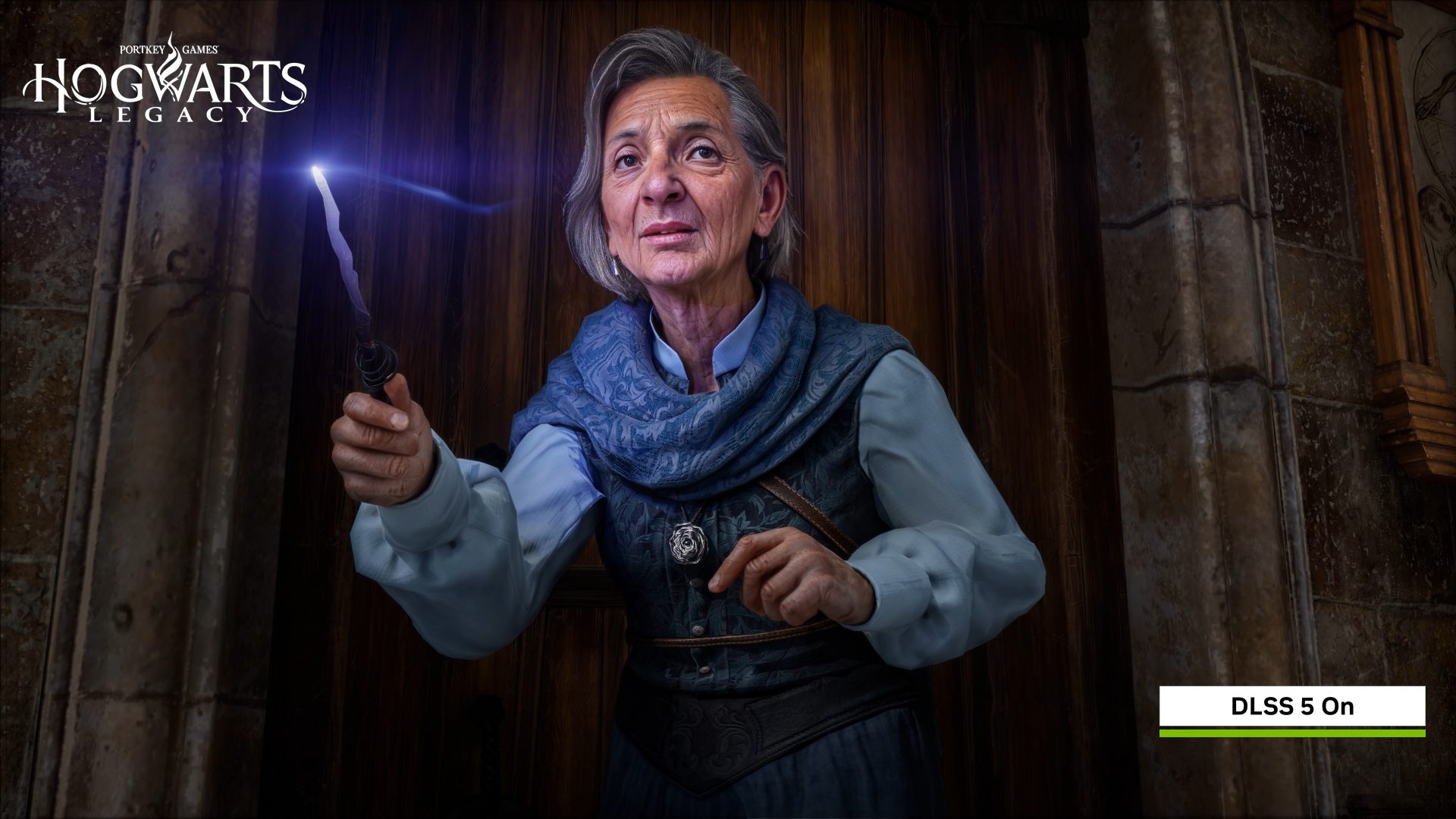
A new upscaling technology aims to challenge NVIDIA's dominance, but its current implementation leaves handheld gam...

A major financial institution proposes a $80 price tag for the next installment in Rockstar’s iconic series, signal...