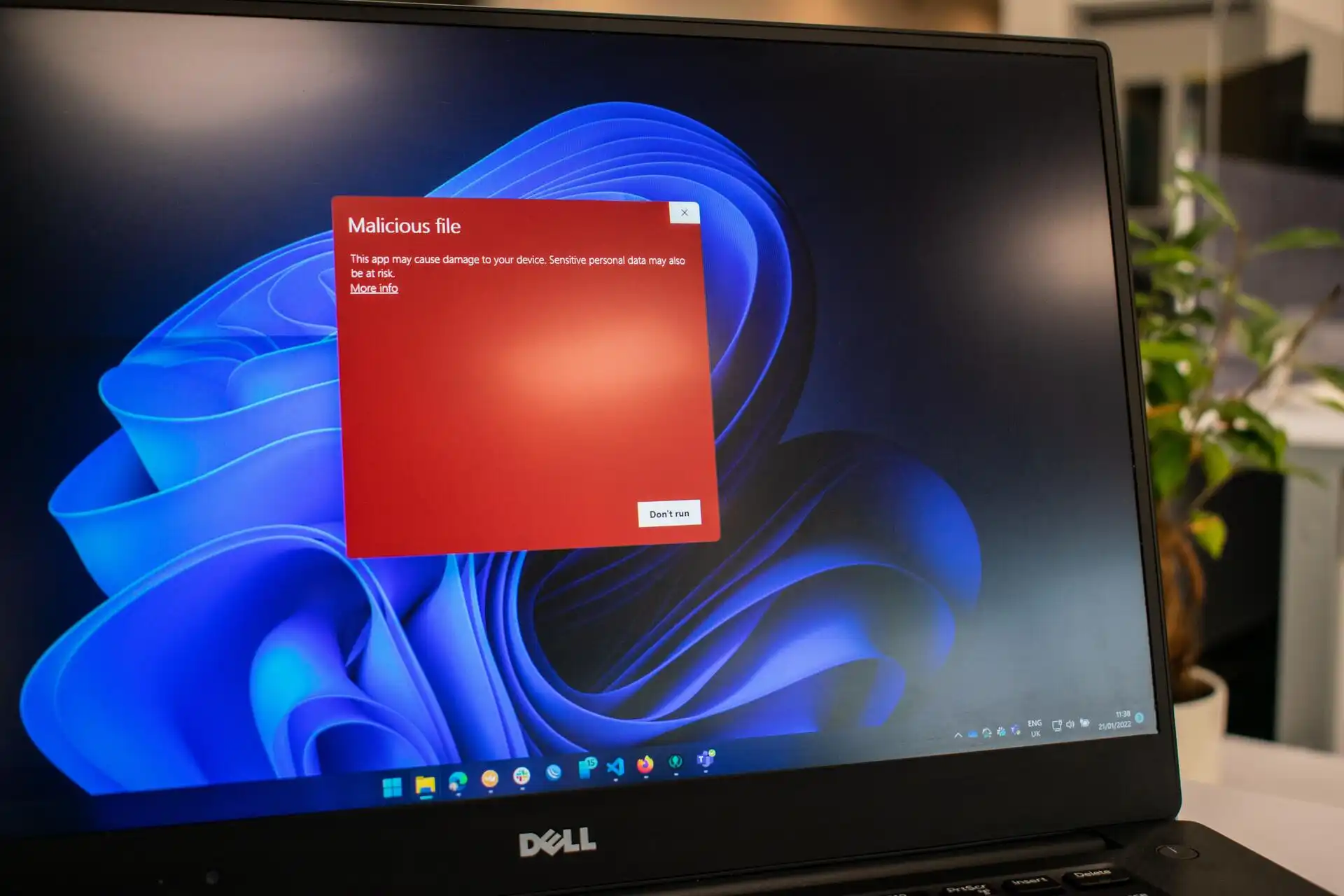
Enterprises relying on Windows 11 are facing an unintended complication: a new security measure in the latest April update can prevent legitimate users from logging into their systems. The change, designed to enhance device protection, now forces affected users to reset their PCs through recovery options—a process that wipes all data unless they have a local backup.
This shift marks a departure from previous Windows behavior, where hardware-based security features could be bypassed with administrative tools or group policies. Now, even IT administrators find themselves limited by the update’s strict enforcement, creating a scenario where platform lock-in becomes a practical constraint rather than just a theoretical concern.
Why it matters
The update’s new requirement stems from an expanded use of Trusted Platform Module (TPM) 2.0 checks and Secure Boot validation. While these features were already part of Windows 11, the April patch tightens their application, effectively treating non-compliant devices as untrusted—even if they meet hardware specifications. For businesses with mixed or legacy hardware, this means some machines are now inaccessible without a full reset.
Key implications
- Users must perform a clean install or recovery to regain access, losing unsaved data unless backed up elsewhere.
- IT departments can no longer rely on traditional troubleshooting steps like Safe Mode or system restore.
- The change applies broadly, including devices that previously passed TPM and Secure Boot checks without issue.
The update’s rollout was initially framed as a security improvement, but its side effects reveal a tradeoff: stronger protection comes at the cost of user flexibility. For enterprises, this raises questions about long-term platform dependency and whether such changes should be more gradually introduced or clearly communicated in advance.
At its core, the issue highlights how operating system updates can reshape user expectations without immediate visibility. What was once a minor security layer now acts as an access barrier, forcing organizations to rethink their hardware standards and backup strategies. The lesson is clear: platform lock-in isn’t just about vendor control—it’s also about how updates redraw the boundaries of what users can do on their own devices.