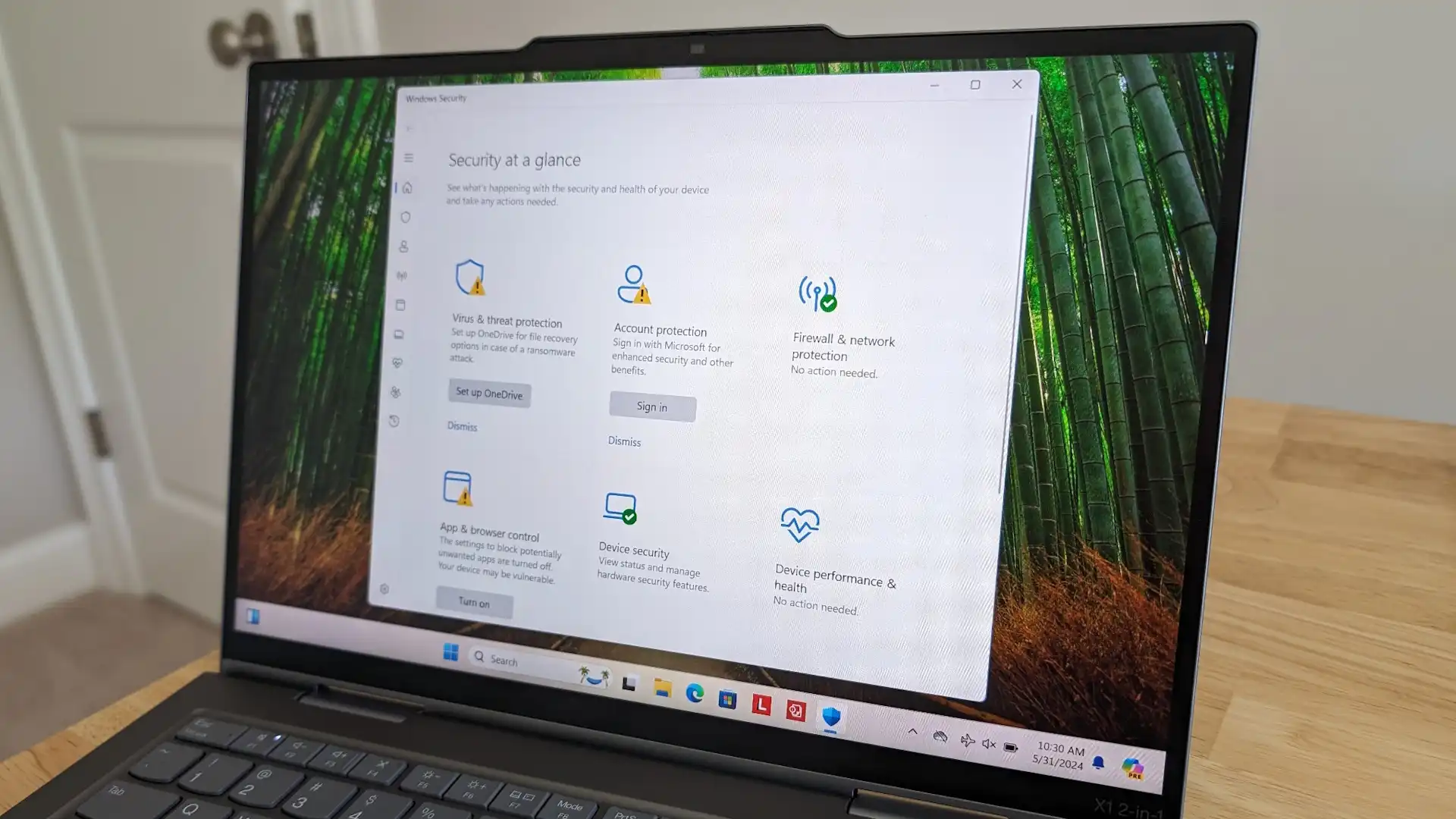
Microsoft Edge’s decision to store passwords in plaintext RAM is a rare departure from industry standards, where encryption is the norm. The browser retrieves credentials faster by skipping decryption steps, but this convenience comes with a hidden cost: increased exposure to memory scraping attacks. For PC builders, this design introduces compatibility challenges, as plaintext storage can complicate system security measures.
While most password managers encrypt stored data, Edge’s approach bypasses encryption entirely, storing passwords directly in RAM. This method is efficient but leaves them accessible to any malware that gains access to memory. The speed advantage is undeniable, yet the trade-off for users and system integrators is significant. In environments where security is critical—such as shared or enterprise systems—the risks of plaintext storage become more pronounced.
The potential consequences of this design choice are still unfolding. As malware evolves, memory scraping tools could become more widespread, making it easier for attackers to extract sensitive data without needing to break encryption. For now, users must balance the convenience of Edge’s password management against the growing threat landscape. Whether this trade-off is sustainable remains an open question.
Edge’s strategy highlights a broader tension in technology: speed and security often compete, forcing users and builders to weigh their priorities carefully. In an era where data breaches are increasingly sophisticated, the choice to prioritize convenience over encryption could have lasting implications for both individual users and larger systems.