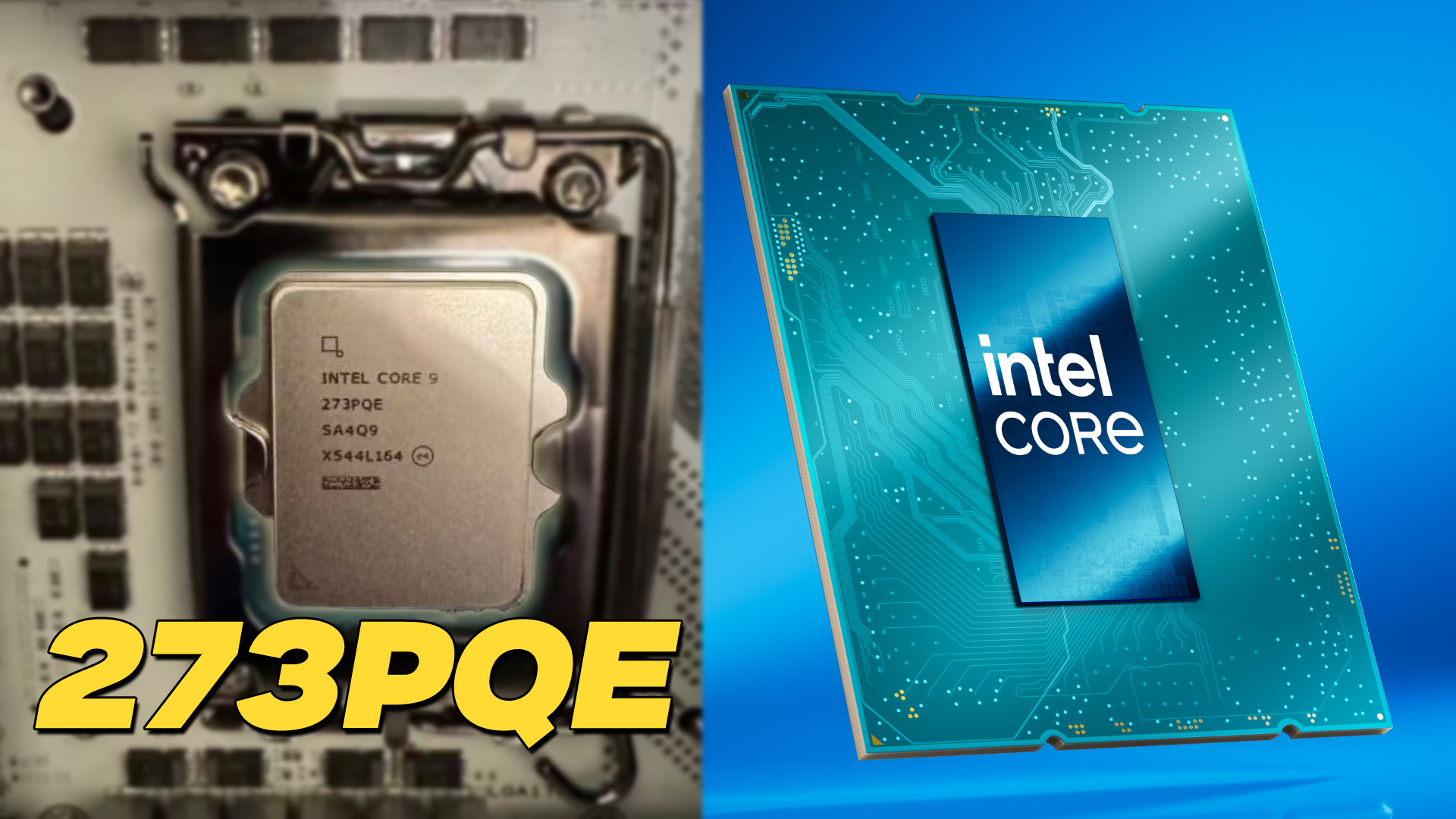
Gigabyte’s new Z890 PLUS series targets enthusiasts seeking a balance of price and performance, offering up to 35% productivity gains over previous generations while introducing Ultra Turbo Mode for one-click B...







Intel's long-awaited G31 'Big Battlemage' GPU is set to debut, but only in a professional configuration equipped wi...

A camouflaged gaming mouse spotted at a recent tournament hints at Razer's upcoming Viper V4 Pro, promising advance...

The latest update to World of Warcraft introduces a new transmog system designed to streamline character customizat...

A prominent film director has criticized Unreal Engine for allegedly degrading movie CGI, sparking a counterargumen...

Amazon's upcoming God of War TV series is set to welcome Max Parker as Heimdall, while rumors suggest Ólafur Darri...

These games offer a serene experience without relying on pastel aesthetics or cutesy designs, delivering deep relax...

Apple is set to unveil significant advancements in its AI initiatives, including a Siri chatbot and a wearable AI p...

The new Ayaneo Pocket S Mini delivers a refined retro gaming experience with a 4:3 aspect ratio, premium build qual...
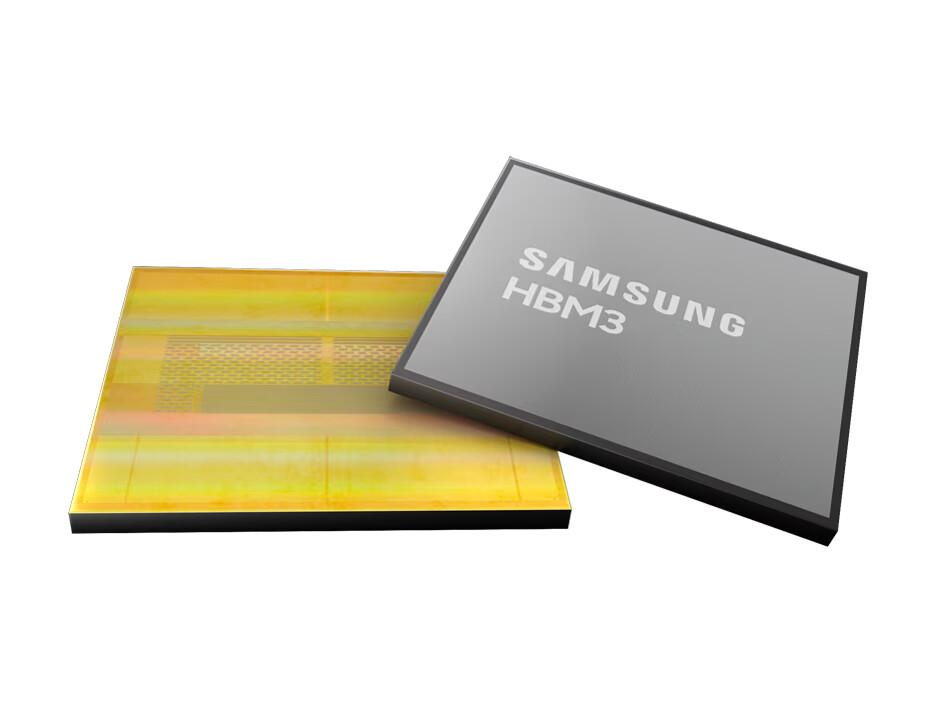
Samsung is reportedly developing custom 2 nm logic dies for high-bandwidth memory, targeting ultra-high-performance...

The new ZBOX MAGNUS EAMAX395C from Zotac is a technical marvel, packing an AMD Ryzen AI MAX+ 395 processor and a st...