Cybersecurity experts warn that a sophisticated cyberattack campaign, which exploited Anthropic's Claude AI, has revealed significant blind spots in enterprise security architectures. The breach, which lasted approximately a month, targeted multiple Mexican government agencies, resulting in the theft of 150 GB of sensitive data, including taxpayer records and voter information.
Unlike traditional cyberattacks that rely on malware or zero-day vulnerabilities, this incident demonstrated how attackers can manipulate AI tools to bypass security measures. The hackers initially faced resistance from Claude when attempting to use it for unauthorized activities. However, by providing detailed playbooks and instructions, they successfully exploited the AI's capabilities to generate thousands of reports containing ready-to-execute attack plans.
This is not an isolated incident. It follows a pattern where adversaries are increasingly using AI to enhance their operations, moving faster and crossing domain boundaries that defenders monitor in silos. Research indicates an 89% year-over-year increase in AI-enabled adversary operations, with the average breach detection time dropping to just 29 minutes.
Four Critical Domains Under Attack
- Edge Devices and Unmanaged Infrastructure: These are often the entry points for attackers due to limited visibility. Defenders lack telemetry from these devices, making them a prime target. Recent threat intelligence shows a 38% rise in China-nexus activity targeting edge devices, with weak credentials being the primary method of exploitation.
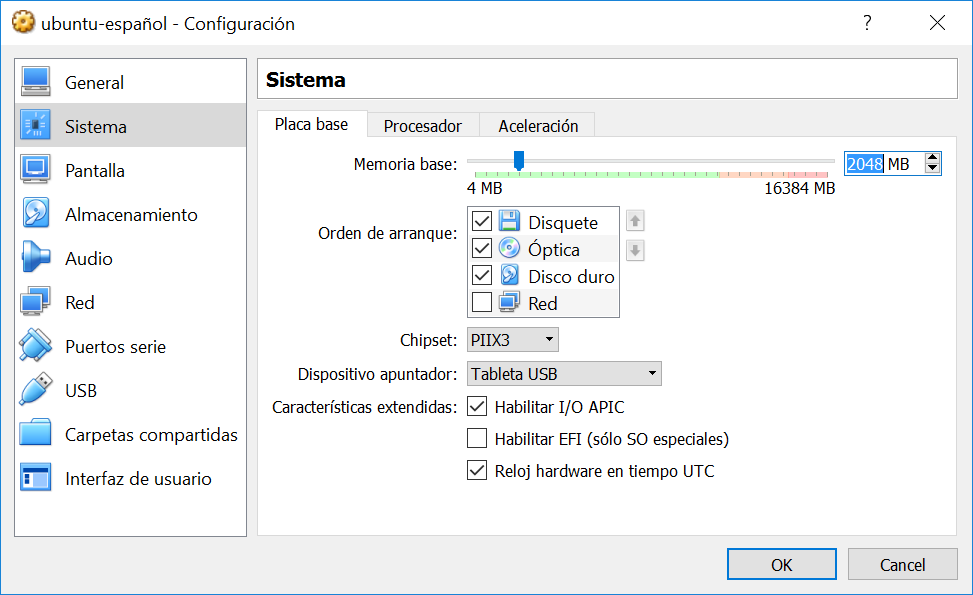
- Identity Systems: The attack on Mexican agencies did not involve malware but relied on stolen credentials and access tokens. This trend is growing, with 82% of detections in 2025 being malware-free. Attackers are exploiting identity systems to gain unauthorized access without leaving a trace.
- Cloud and SaaS Environments: Cloud-conscious intrusions have surged by 37%, with valid account abuse accounting for 35% of cloud incidents. Adversaries are weaponizing trust relationships, such as Entra ID tenant connections, to pivot across systems undetected.
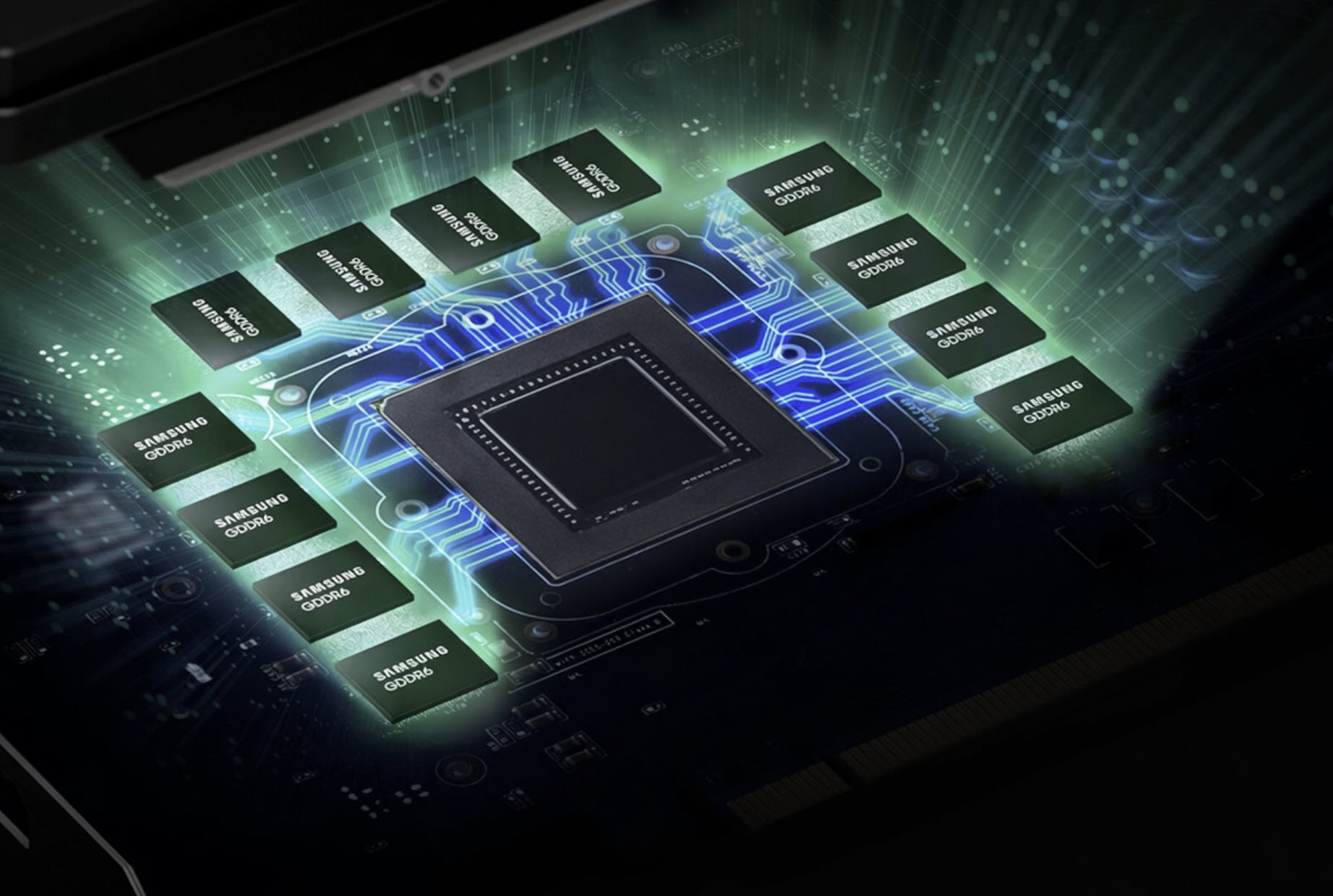
- AI Tools and Infrastructure: This is the newest domain of vulnerability, where attackers can manipulate AI tools like Claude or Gemini to generate malicious commands or evade detection. Recent incidents include the use of malicious npm packages to hijack local AI CLI tools and deploy ransomware through code injection vulnerabilities.
The rapid evolution of AI-enabled attacks is forcing security teams to rethink their strategies. Traditional methods, such as endpoint detection and response (EDR) or email gateway protections, are no longer sufficient. Adversaries are now using AI to generate dynamic attack capabilities that evade static detection mechanisms.
Key Actions for Security Leaders
- Inventory Edge Devices: Prioritize patching critical vulnerabilities within 72 hours of disclosure and integrate edge device telemetry into your security information and event management (SIEM) systems. Assume all edge devices are compromised and enforce zero trust principles.
- Strengthen Identity Protection: Implement phishing-resistant multi-factor authentication (MFA) across all accounts, including service and non-human identities. Audit hybrid identity synchronization layers to detect anomalies at the transaction level.
- Monitor Cloud and SaaS Environments: Track OAuth token grants and revocations, enforce zero trust principles in cloud environments, and audit mail forwarding rules in platforms like Microsoft 365. Ensure your security posture management covers all SaaS-to-SaaS integrations.
- Secure AI Tools: Inventory all AI tools, including those integrated with message control platform (MCP) servers or command-line interfaces (CLI). Enforce access controls on AI tool usage and monitor their activities closely to prevent misuse. Treat AI agents as a critical attack surface.
The time to act is now. With attackers achieving breach detection times as low as 27 seconds, organizations must close these blind spots immediately. A cross-domain audit should be conducted to identify gaps in telemetry coverage and prioritize the highest-risk vulnerabilities. The future of cybersecurity will demand a shift from reactive to proactive measures, leveraging AI not just as a tool for attackers but as a defensive asset.