In an evolving landscape of digital threats, a recently uncovered Chrome extension has exposed the risks associated with even seemingly legitimate tools in official app stores. This particular case involves NexShield Smart Ad Blocker, which briefly appeared on the Chrome Web Store before its removal due to its malicious nature.
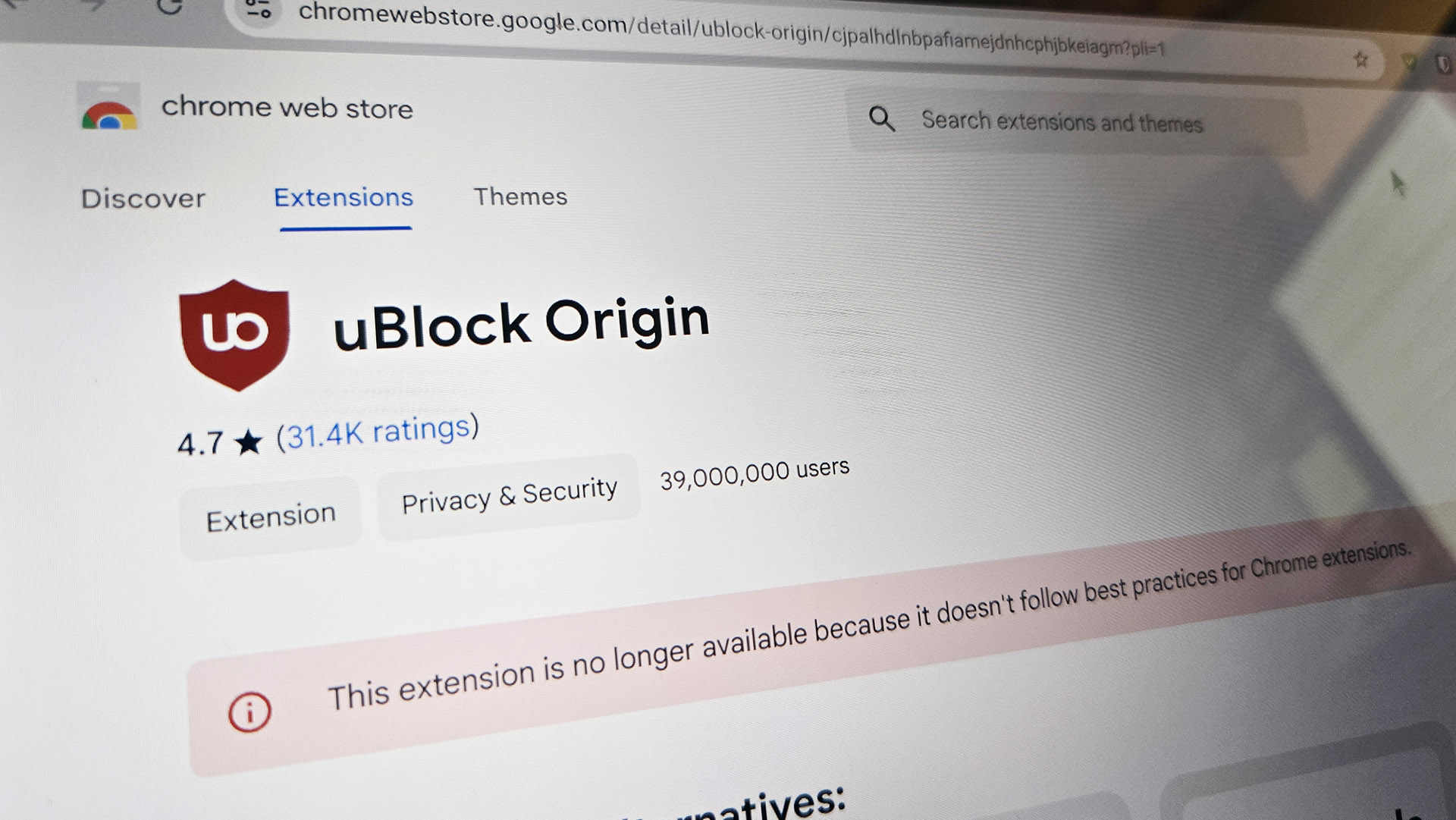
The extension's promotional materials falsely attributed its development to Raymond Hill, the creator of uBlock Origin, a widely recognized ad-blocking tool known for its effectiveness and user trust. This impersonation was particularly cunning, as it exploited Hill's reputation in the cybersecurity community, where his stance against Google's Manifest V3 changes had drawn significant attention.
NexShield's true purpose was far from benign. Once installed, the extension began sending user tracking information back to its creators without immediate detection. After a one-hour delay, it initiated a series of actions designed to overwhelm system resources, leading to browser crashes. This deliberate destabilization prompted users to restart their browsers, at which point they were instructed to execute a specific command via the Windows Run tool—effectively installing ModeloRAT, a remote access trojan (RAT) capable of spying on users, modifying system configurations, and deploying additional malicious tools.
Security researchers have linked this campaign to the threat actor known as KongTuke, which appears to be specifically targeting high-value corporate networks. The malware's sophistication lies in its ability to evade detection for an extended period while simultaneously gathering sensitive information, making it a formidable challenge for both users and cybersecurity firms.
This incident underscores the importance of vigilance when downloading browser extensions, even from trusted sources like the Chrome Web Store. While uBlock Origin remains a staple in the ad-blocking community—albeit with limitations on Chromium-based browsers due to Manifest V3—the NexShield case serves as a stark reminder that reputation can be weaponized. Users and organizations must remain cautious, verifying the authenticity of extensions and monitoring system behavior for signs of malicious activity.