A data breach targeting Rockstar Games’ upcoming GTA 6 project has shifted focus from the stolen information itself to the broader implications for IT infrastructure, platform compatibility, and development workflows. While the immediate concern is data exposure, the long-term impact may extend to how development teams integrate secure practices without disrupting progress—a critical consideration for any large-scale software or game project.
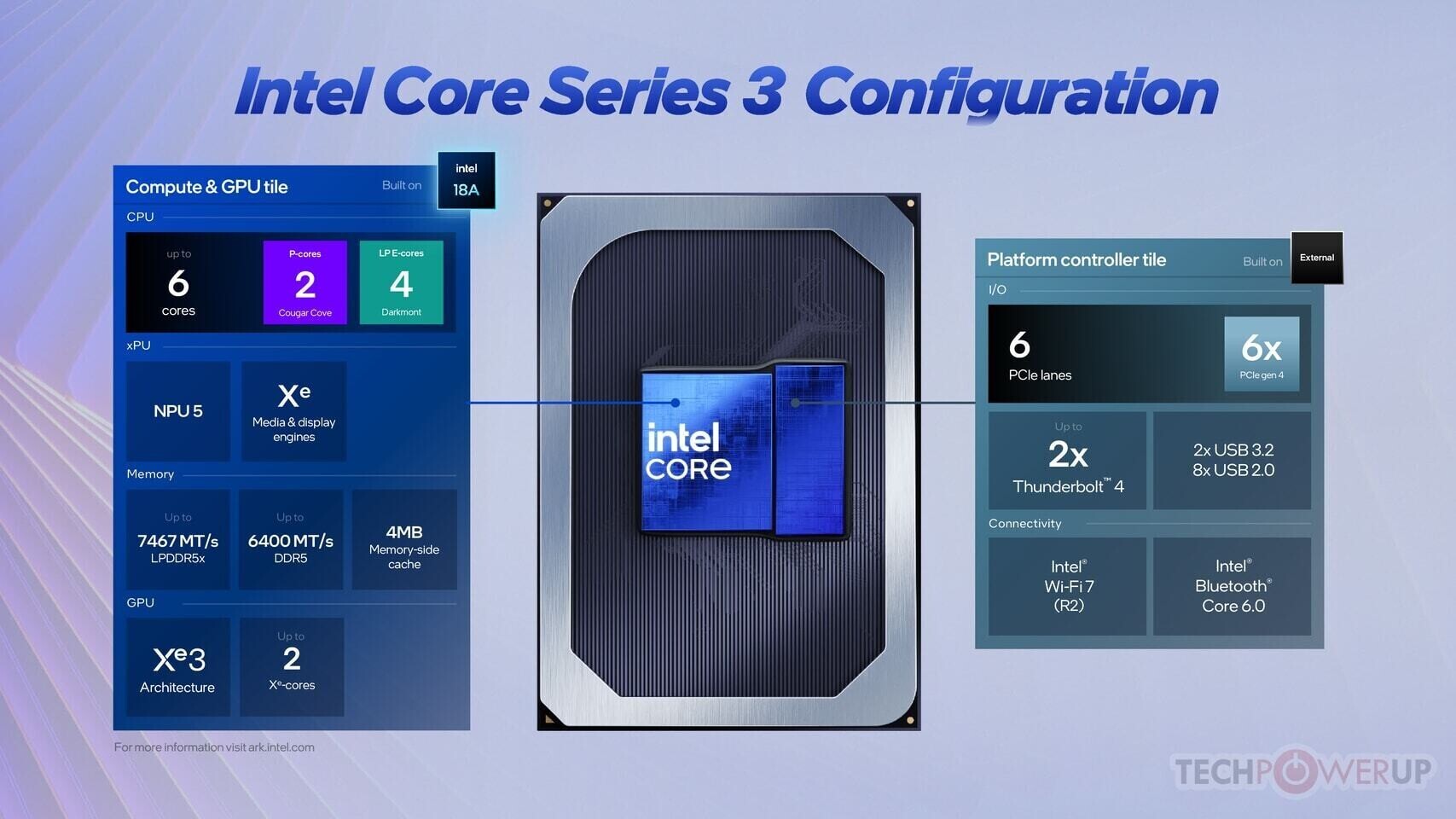
The breach, claimed by a group identifying as ShinyHunters, reportedly includes source code, build files, and internal documentation. The challenge for Rockstar’s IT team is not just verifying the authenticity of this data but also determining how its presence could complicate platform testing. Historically, Rockstar has maintained strict control over GTA titles to ensure smooth performance across Windows, macOS, and consoles with varying memory (e.g., 16GB RAM) and storage constraints (e.g., 2TB SSDs). If the stolen data contains unreleased engine optimizations or proprietary algorithms, reintegrating it into development pipelines could introduce vulnerabilities that require extensive validation.
- Platform Testing Risks: Unverified changes to build files may lead to compatibility issues across operating systems and hardware configurations, potentially delaying certification for consoles like PlayStation 5 and Xbox Series X|S.
- Secure Development Pipelines: Rockstar’s reliance on encrypted pipelines and access controls will face scrutiny, prompting other studios to adopt similar measures to prevent similar incidents during active development.
- Third-Party Dependencies: External security vendors may need to audit Rockstar’s infrastructure for gaps that could have allowed the breach, adding another layer of complexity to post-incident recovery.
The incident also serves as a case study in IT resilience. Unlike hardware launches or software updates, where performance metrics define success, a breach forces teams to prioritize intangible but critical factors: data integrity, pipeline security, and the ability to adapt without compromising timelines. For development environments, this means balancing strict access protocols with agility—no small feat when working on projects like GTA 6, which reportedly involves over 100 developers and years of planning.
Looking ahead, the breach could accelerate industry-wide shifts toward zero-trust architectures and continuous monitoring in game development. If Rockstar’s response demonstrates effective mitigation without derailing progress, it may set a new standard for how studios handle such incidents. For IT teams, the lesson is clear: the focus must shift from reactive damage control to proactive strategies that integrate security into every stage of development.
The GTA 6 breach, then, is less about the data itself and more about what it reveals—the fragility of even the most secure systems when faced with determined external threats. As Rockstar navigates this challenge, the broader takeaway for developers and IT professionals is the need for a culture of resilience, where security is not an afterthought but a foundational element of production.