For those who rely on CPU-Z and HWMonitor to keep tabs on their system's performance, a recent discovery has cast a shadow over what was once trusted software. The latest versions of these tools, designed to monitor everything from CPU usage to memory timings, have been found to harbor malicious code. While the full extent of the compromise remains unclear, the news serves as a stark reminder that even the most ubiquitous utilities can become vectors for security threats.
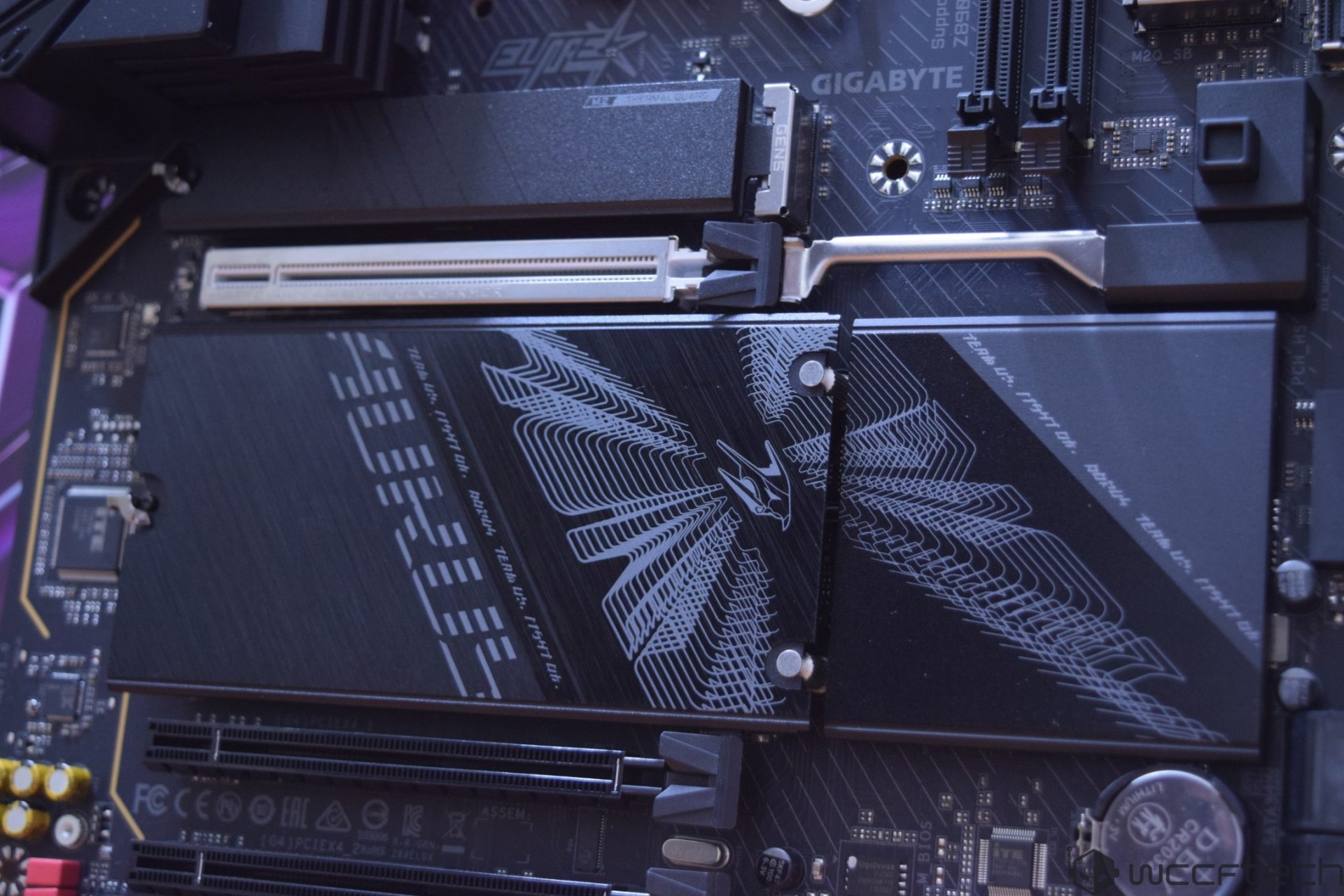
CPU-Z and HWMonitor are staples in the toolkit of hardware enthusiasts and overclockers, offering detailed insights into system components with minimal overhead. However, the discovery of malware in their latest releases has sent ripples through the community. The implications are still being unpacked, but one thing is clear: users who have downloaded these versions in recent weeks should treat them with extreme caution.
A Closer Look at the Compromise
The malware embedded in CPU-Z and HWMonitor is not yet fully understood, but early reports suggest it may be designed to evade detection while performing unauthorized actions on infected systems. This is particularly troubling given that these tools are often used by individuals who take a meticulous approach to system security—hardly the profile one would associate with casual malware victims.
Key Specs and Context
- Tools Affected: CPU-Z and HWMonitor (latest versions)
- Potential Risks: Unauthorized system actions, data exfiltration (unconfirmed)
- Detection Status: Malware signatures identified; full analysis ongoing
- Impacted Users: Hardware enthusiasts, overclockers, system benchmarkers
The malware's behavior is still under investigation, but its presence in such widely used software could have far-reaching consequences. For users who rely on these tools for performance tuning or diagnostics, the discovery raises questions about trust and security in the hardware ecosystem. While there is no evidence that earlier versions are affected, the incident underscores the need for vigilance when downloading even the most reputable utilities.
Who Should Be Concerned?
The immediate concern is for users who have installed the latest versions of CPU-Z or HWMonitor in recent weeks. However, the broader implications extend to anyone who trusts third-party software without scrutiny—a habit that may need reassessment in light of this incident. For those who use these tools as part of their workflow, the discovery serves as a wake-up call: even the smallest utilities can become gateways for more significant security risks.
The hardware community has long prided itself on its attention to detail, but this event suggests that no tool is immune to compromise. Moving forward, users may need to adopt a more cautious approach when integrating new software into their systems, regardless of its reputation. The fallout from this discovery will likely shape how enthusiasts and professionals view system monitoring tools in the future.
As for the developers behind CPU-Z and HWMonitor, the situation remains fluid. No official statement has been released, but given the gravity of the issue, a swift response is expected. Until then, users are advised to avoid downloading these versions unless absolutely necessary and to monitor their systems for any unusual activity.