ASUS has addressed concerns regarding a recent security incident involving a third-party supplier. The statement released by the company details a breach affecting specific camera source code utilized in certain ASUS mobile devices. While acknowledging the unauthorized access, ASUS maintains that this event did not result in any compromise of ASUS products themselves, internal systems, or user privacy data.
The incident underscores the increasingly complex and interconnected nature of modern technology supply chains. Manufacturers rely on numerous third-party partners for various components and software elements within their devices. This reliance introduces potential vulnerabilities that require constant vigilance and robust security measures. ASUS’s response demonstrates a proactive approach to mitigating these risks.
Understanding the Scope of the Incident
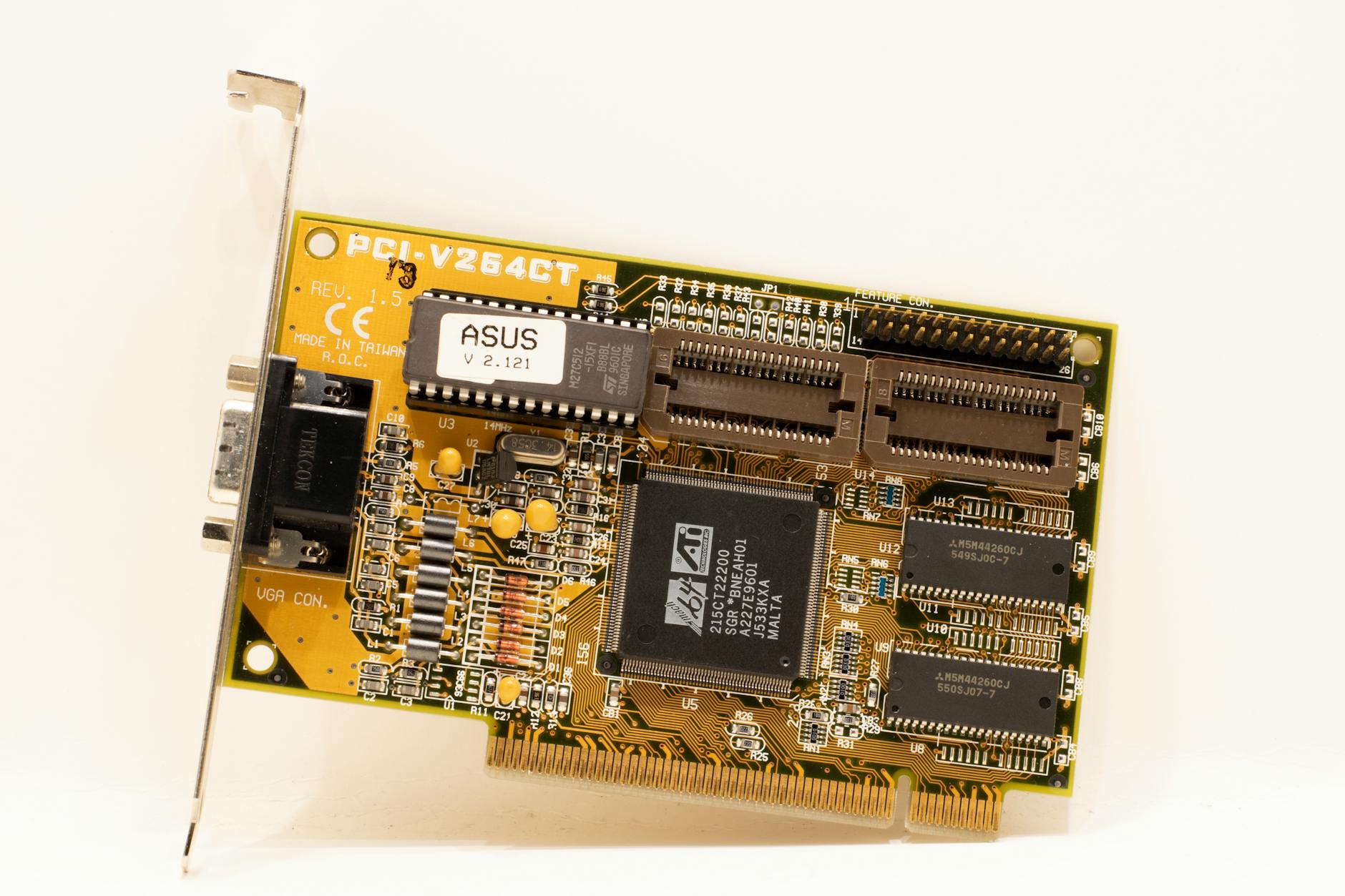
ASUS clarified that the breach targeted code related to camera functionality found in specific models within its smartphone portfolio. It's crucial to note that this was an isolated incident affecting a particular supplier’s operations, and not a systemic failure across ASUS’s broader technology ecosystem.
The company’s statement specifically states that the compromised code did not grant access to user data such as contacts, photos, or personal information stored on devices. Furthermore, the incident didn't impact ASUS’s internal network infrastructure, product development systems, or customer support databases. This is a critical distinction often made in security breaches – the unauthorized access doesn't automatically translate to a breach of sensitive user data.
Immediate Actions and Remediation Efforts
Upon discovering the incident, ASUS immediately took action to contain the breach and assess its full extent. This involved working closely with the affected supplier to isolate the compromised systems and implement enhanced security protocols. The company also initiated a thorough internal review of its supply chain management processes.
A key component of the response has been a focused effort to strengthen security measures across ASUS’s entire supply chain. This includes, but isn't limited to, increased scrutiny of third-party vendor security practices, enhanced access controls, and more frequent vulnerability assessments.
Strengthening Supply Chain Security: A Multi-Layered Approach
ASUS’s statement highlights a commitment to a multi-layered approach to supply chain security. This isn't simply about fixing the immediate problem; it’s about building resilience against future threats.
- Enhanced Vendor Audits: ASUS is reportedly increasing the frequency and depth of audits conducted on its suppliers, focusing on their cybersecurity posture and adherence to industry best practices.
- Secure Development Lifecycle (SDLC) Integration: The company intends to integrate more stringent security requirements into the SDLC for all components sourced from third-party vendors. This includes rigorous code reviews, penetration testing, and vulnerability scanning throughout the development process.
- Data Encryption & Access Controls: Strengthening data encryption methods both in transit and at rest, coupled with robust access controls, are being prioritized to minimize the potential impact of any future security breaches.
- Supply Chain Risk Management Framework: ASUS is developing a comprehensive supply chain risk management framework that encompasses identification, assessment, mitigation, and monitoring of potential vulnerabilities throughout its entire network of suppliers.
Industry Implications & Best Practices
This incident serves as a stark reminder for the broader technology industry about the importance of robust supply chain security. The interconnectedness of global tech supply chains means that vulnerabilities in one area can quickly propagate to others.
Several key best practices are emerging from this situation
- Zero Trust Architecture: Adopting a ‘zero trust’ approach, which assumes no user or device is inherently trustworthy and requires verification for every access request, is becoming increasingly vital.
- Regular Penetration Testing: Conducting regular penetration tests of both internal systems and third-party vendor environments can help identify vulnerabilities before they are exploited.
- Supply Chain Transparency: Increasing transparency within the supply chain allows companies to better understand the risks associated with their suppliers and collaborate on solutions.
- Incident Response Planning: Having a well-defined incident response plan in place is crucial for quickly containing and mitigating the impact of security breaches.
ASUS’s Ongoing Commitment
In its statement, ASUS reiterated its dedication to protecting user privacy and data security. The company emphasized that this incident has reinforced its commitment to continuous improvement in its security practices and supply chain management processes.
�We take the security of our products and the privacy of our customers extremely seriously,” stated a representative from ASUS (as quoted within the official statement). “This situation highlighted areas where we can strengthen our defenses, and we are committed to implementing those improvements swiftly and effectively.”
Looking Ahead
The tech industry is facing an increasingly sophisticated threat landscape. Companies like ASUS are recognizing that supply chain security isn’t just a compliance issue; it's a fundamental business imperative. The ongoing evolution of cybersecurity threats demands a proactive, adaptive approach – one that prioritizes collaboration, innovation, and a relentless focus on protecting user data.