A critical flaw in a line of TP-Link routers has emerged as a stealthy threat to small business networks, potentially giving Russian state-backed hackers an entry point. The vulnerability allows unauthorized access to administrative interfaces, but it's not the only concern—security researchers have observed active exploitation attempts, leaving many devices unpatched and exposed.
The issue originates in the Kasa smart plug series, which shares firmware with several TP-Link routers. While physical proximity or a compromised local network is required for initial access, attackers can then move laterally through connected devices to larger enterprise systems. The exploit chain is already being used, but patching isn't straightforward for older models.
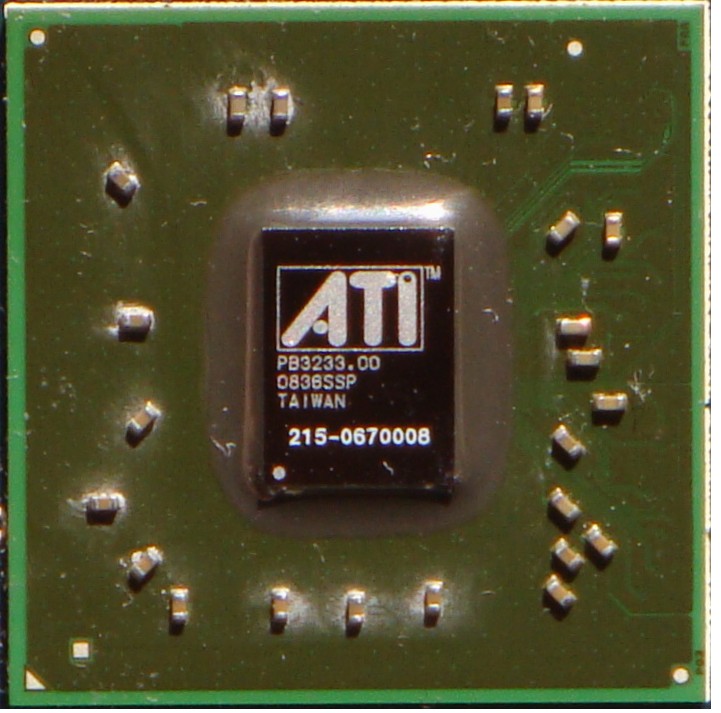
Hardware and Firmware Details
TP-Link has acknowledged the vulnerability in routers running firmware versions prior to 1.2.5 Build 20231018 Rel.69472n. Affected hardware includes the Archer C7 v2, Talon M1 5G, and Kasa smart plug (KP400). Small businesses using these devices face a dilemma: upgrading to patched firmware can disrupt existing configurations, and some older units lack support entirely.
Implications for Small Businesses
A single compromised router can serve as a gateway for deeper network breaches, enabling data exfiltration or lateral movement within an organization. The challenge lies in balancing immediate security needs with operational continuity—especially for teams without dedicated IT staff. Experts recommend isolating affected routers from core business systems while awaiting patches, but the window for action is narrowing.
Looking Ahead
This incident highlights a growing trend: state-sponsored cyber threats are no longer confined to large enterprises. Small businesses with limited resources may benefit most from adopting network segmentation and zero-trust principles, even if full-scale upgrades aren't feasible. The lesson? Upgrading isn't just about hardware—it's about recognizing when a silent threat becomes an operational risk.